Separate Chaining vs Open Addressing
Hash tables are commonly used data structure for storing and retrieving data efficiently. Hash tables store data in an array-like structure, assigning each item a unique key. When multiple items have the same hash value, a collision occurs, and two methods are used to resolve these collisions: separate chaining and open addressing. In this article, we will compare these two methods in detail to understand their pros and cons.
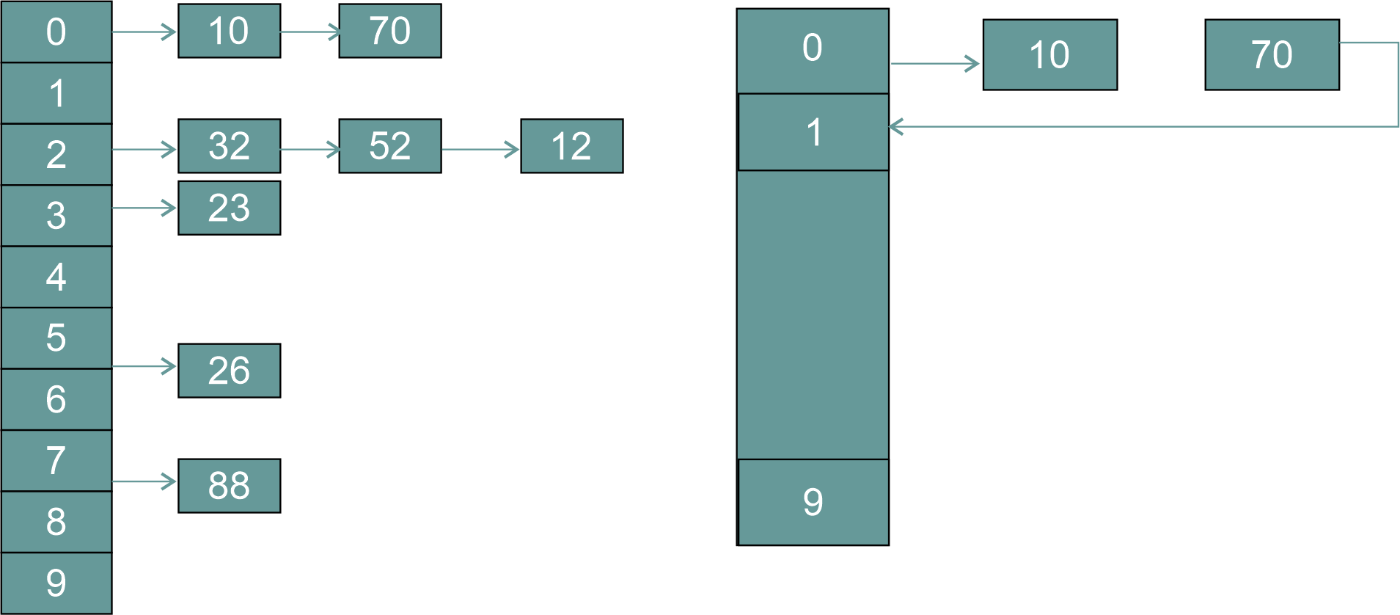
Separate Chaining
Each position in the hash table is a linked list in separate chaining. Each item with the same hash value is stored in the linked list at that position. The hash value is computed to retrieve an item, and the linked list at that position is searched for the item with the specified key.
Pros of Separate Chaining
- Simple Implementation: Separate chaining is straightforward, making it a popular choice among developers.
- Dynamic Memory Allocation: In separate chaining, memory is dynamically allocated, so the hash table can grow or shrink as needed.
- Less Overhead: Separate chaining requires less overhead than open addressing, making it a more efficient choice for hash tables with many items.
Cons of Separate Chaining
- Increased Memory Usage: Separate chaining requires more memory than open addressing as it stores each item in a separate linked list.
- Slower Performance: Separate chaining can be slower than open addressing as it requires searching through a linked list to find an item.
When to Use Separate Chaining
- When the number of items in the hash table is large: Separate chaining is more efficient in this case as it requires less overhead than open addressing.
- When the load factor is high: The load factor is the ratio of the number of items in the hash table to the size of the hash table. A high load factor can result in frequent collisions, and separate chaining is better equipped to handle these collisions.
- When dynamic memory allocation is desired: Separate chaining allows for dynamic memory allocation, which is beneficial when the number of items in the hash table constantly changes.
Open Addressing
All items are stored in the same array in open addressing, and collisions are resolved by finding the next available position in the array. Several techniques are used in open addressing, including linear probing, quadratic probing, and double hashing.
Pros of Open Addressing
- Reduced Memory Usage: Open addressing requires less memory than separate chaining, as all items are stored in the same array.
- Faster Performance: Open addressing can be faster than separate chaining as it requires only a linear search through the array to find an item.
Cons of Open Addressing
- Complex Implementation: Open addressing is more complex than separate chaining, making it a less popular choice among developers.
- Fixed Memory Allocation: In open addressing, memory is fixed, so the hash table cannot grow or shrink dynamically.
- Increased Overhead: Open addressing requires more overhead than separate chaining, making it a less efficient choice for hash tables with many items.
When to Use Open Addressing
- When the number of items in the hash table is small: Open addressing is more efficient in this case as it requires less memory than separate chaining.
- When the load factor is low: A low load factor results in fewer collisions, and open addressing is better equipped to handle these collisions.
- When memory usage is a concern: Open addressing requires less memory than separate chaining, making it a better choice when memory usage is a concern.
Difference between separate chaining and open addressing
| Feature | Separate chaining | Open Addressing |
| Collision resolution | Via linked-lists | Within the table |
| Space usage | Potentially more | Potentially less |
| Load factor | Can handle higher load | May have a lower load threshold |
| Table size | Can be smaller | Must be larger |
| Deletion | May require tombstones | Can have clustering |
| Search performance | May have slower search | May have faster search |
| Insertion performance | May have slower insertion | Doesn't need extra memory nodes |
Conclusion
In summary, separate chaining and open addressing are two commonly used methods for resolving collisions in hash tables. Separate chaining is a simpler and more efficient method for hash tables with many items. At the same time, open addressing is a more efficient method for hash tables with fewer items. The choice between these two methods will depend on the application's specific requirements, including the number of items in the hash table, the load factor, and the need for dynamic memory allocation. Developers must carefully consider these factors when choosing between separate chaining and open addressing.