Turn Variable or Strict Alternative Approach
Turn Variable or Strict Alternative Approach
Turn Variable Approach is used for process synchronization mechanism, which offers synchronization between two processes.
Turn variable is implemented on user mode, and it is a software mechanism. We can only use Turn variable or strict alteration approach on two processes, and it is a busy waiting solution.
We can understand the concept of Turn Variable with the help of the following example. Suppose we have two processes Pa and Pb, which share a variable named Turn Variable.
The below section gives the pseudocode of the program for two processes are:
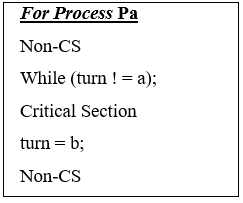
’
The problem which arises in the lock variable mechanism is that if the value of the lock variable is 1, then in this condition, the process enters into the critical section. At the same time, more than one process can see the value of lock variable 1. That's why mutual exclusion is not given in the lock variable mechanism.
We can solve this problem with the help of turn variable approach. The approach is that if the turn variable value is equivalent to the process PID then the process can enter into the critical section.
The value of the turn variable is either ‘a’ or ‘b’. If the turn variable value is not 'a', then the value of the turn variable will be ‘b’ and vice versa.
In the entry section, there is a condition that ‘Pa’Process cannot enter in the critical section till the value of the process is 'b', or we can say that until the value of the process ‘Pb’ is'a'. It cannot be entered into the critical section.
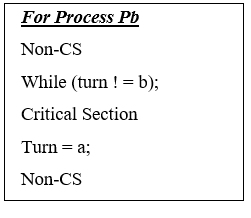
Now we have two processes, ‘Pa’ and ‘Pb’, and both the processes, which are ‘Pa’, and ‘Pb’ need to execute in the critical section.
The process ‘Pa’ gets the opportunity to enter into the critical section because the value of the turn variable is equal to ‘a’.
The value of Process ‘Pa’ will be 'a' till the process ‘Pa’ completes its execution in the critical section. When the process ‘Pa’ completes its execution in the critical section, then we assign the value ‘b’ to the turn variable.
Now the value of turn variable is 'b'. So, the process ‘Pb’ will enter into the critical section. The turn variable value will be ‘b’ till the process ‘Pb’ completes its execution in the critical section.
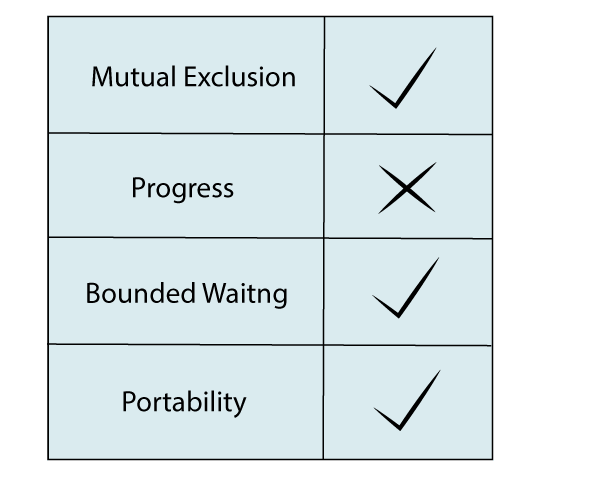
Analysis of Turn Variable or Strict Alteration Approach
Now based, on four requirements, we analyze turn variable or strict alteration approach:
- Mutual Exclusion: - In every case, the Turn Variable approach offers Mutual exclusion. The turn variable or strict alteration approach is only applicable to two processes. In this, if the turn variable is equivalent to the Process ID, then the process enters into the critical section. Otherwise, no process will enter into the critical section.
- Progress: - In Progress, if a process ‘Pa’ doesn't want to enter in the critical section at its turn, there may be a chance that another process, which is ‘Pb’ gets blocked for a long time. That's why the approach of turn variable does not guarantee Progress.
- Portability: - Turn Variable or strict variable approach is implemented on the user mode, and it is a software mechanism. In turn variable, the operating system does not give any special instructions.