Unicast Routing Protocol
Unicast Routing Protocol: Unicast is a point to point communication arrangement that only occurs between the sender and receiver.
Routing Information Protocol
RIP is an open standard protocol that can work with any company's router. RIP is a classful routing protocol; therefore, it does not support VLSM (variable length subnet mask).
The RIP is a distance-vector protocol. It is used in small networks. In this, the hop count is used as a matrix to determine the most appropriate path (s). So that data packets may reach the destination from that path. In this protocol, the maximum number of hops count can only be up to 15. The hop count 16 is considered infinite. The hop count 16 is used to indicate networks that cannot be accessed.
Note: It uses UDP port 250 for the routings table updates.
Distance Vector Routing
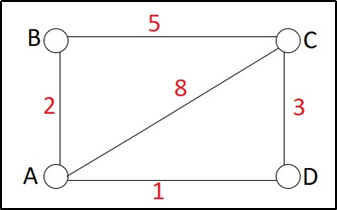
Let take an example to understand the distance-vector routing protocol better.
In this example, is a network consisting of four routers A, B, C, and D. The weights are shown in the edges. And the weights could be distances or costs or delays.
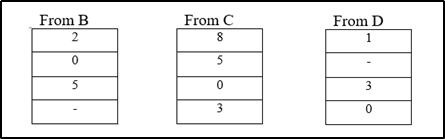
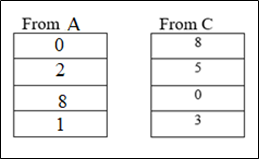
Step 1: Every router prepares its routing table using its information. Every table of the router is shown below.
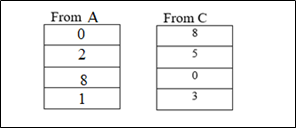
At Router A
| Destination | Distance | Next Hop |
| A | 0 | A |
| B | 2 | B |
| C | 8 | C |
| D | 1 | D |
At Router B
| Destination | Distance | Next Hop |
| A | 2 | A |
| B | 0 | B |
| C | 5 | C |
| D | Infinite | - |
At Router C
| Destination | Distance | Next Hop |
| A | 8 | A |
| B | 5 | B |
| C | 0 | C |
| D | 3 | D |
At Router D
| Destination | Distance | Next Hop |
| A | 1 | A |
| B | Infinite | - |
| C | 3 | C |
| D | 0 | D |
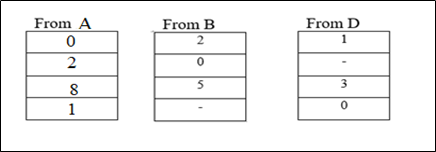
Step 2:
- Every router shares its distance vector with its neighbors obtained in Step-01.
- Every router prepares a new routing table after exchanging of distance vectors.
At Router A new table:
Cost (A -- B) = 2 Cost (A -- C) = 8 Cost (A -- D) = 1
Cost of reaching destination
B from router A = min {2+0, 8+5, 1+?} = 2 via B.
C from router A = min {2+5, 8+0, 1+3} = 4 via C.
D from router A = min {2+?, 8+3, 1+0} = 1 via D.
| Destination | Distance | Next Hop |
| A | 0 | A |
| B | 2 | B |
| C | 4 | D |
| D | 1 | D |
At Router B new table:
Cost (B -- A) = 2 Cost (B -- C) = 5
Cost of reaching destination
A from router B = min {2+0, 5+8} = 2 via A.
C from router B = min {2+8, 5+0} = 5 via C.
D from router B = min {2+1, 5+3} = 3 via D.
| Destination | Distance | Next Hop |
| A | 2 | A |
| B | 0 | B |
| C | 5 | C |
| D | 3 | A |
At Router C new table:
Cost (C -- A) = 8 Cost (C -- B) = 5 Cost (C -- D) = 3
Cost of reaching destination
A from router C = min {8+0, 5+2, 3+1} = 4 via A.
B from router C = min {8+2, 5+0, 3+?} = 5 via B.
D from router C = min {8+1, 5+?, 3+0} = 3 via D.
| Destination | Distance | Next Hop |
| A | 4 | D |
| B | 5 | B |
| C | 0 | C |
| D | 3 | A |
At Router D new table:
Cost (D -- A) = 1 Cost (D -- C) = 3
Cost of reaching destination
A from router D = min {1+0, 3+8} = 1 via A.
B from router D = min {1+2, 3+5} = 3 via B.
C from router D = min {1+8, 3+0} = 3 via D.
| Destination | Distance | Next Hop |
| A | 1 | A |
| B | 3 | A |
| C | 3 | C |
| D | 0 | D |
Final routing tables of every router.
Open Shortest Path First
OSPF is a Link-State routing protocol. It uses SPF (shortest path first) or dikistra algorithm. It is a classless routing protocol; therefore, it supports VLSM (variable length subnet mask). OSPF is a dynamic protocol that takes information (data) from its nearest routers and passes that information to all other routers.