Basic Characteristics of Computer Network
A computer network is a system of interconnected devices that are linked together to share information, resources, and services. Computer networks can be used in various settings, including homes, businesses, educational institutions, and governments. Networks can range from simple setups with just a few devices to complex systems connecting thousands or millions of devices.
The basic characteristics of computer networks are essential for building a reliable, secure, and high-performance network that can accommodate growth and changing needs over time. These characteristics include:
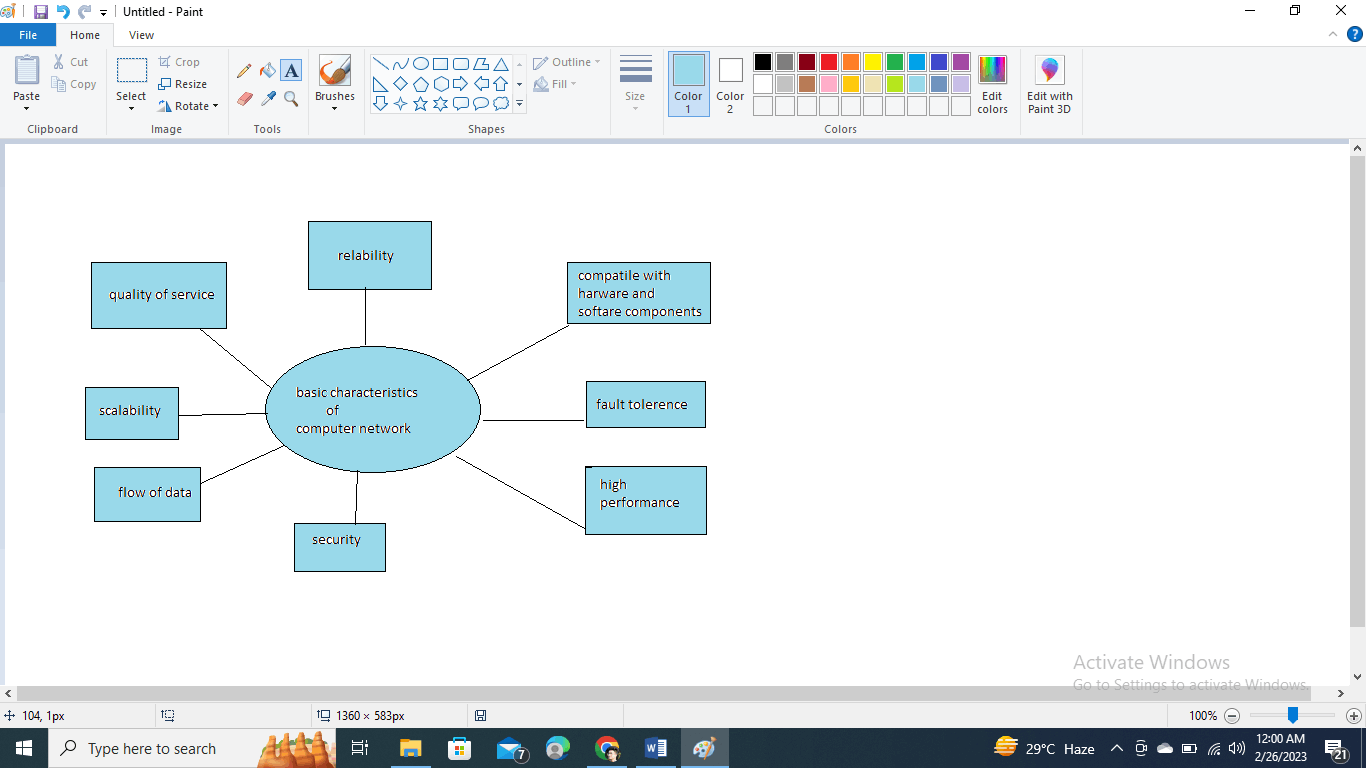
- Reliability: Reliability is the ability of a computer network to consistently provide uninterrupted and error-free service. A reliable network should be able to recover from failures and continue to operate without interruption. This is achieved through redundancy in hardware and software, backup systems, and fault-tolerant designs. Reliability is crucial for network users, who rely on the network to access critical information, communicate with others, and complete important tasks. Downtime or service interruptions can be costly and result in lost productivity, revenue, or data. Therefore, ensuring network reliability is a top priority for network administrators and designers.
- Quality of Service: Quality of Service (QoS) refers to the ability of a computer network to provide a specific level of service to its users, such as guaranteed bandwidth, latency, or packet loss. QoS is important for applications such as voice and video, which require consistent and reliable network performance. QoS is achieved through traffic shaping, queuing algorithms, and network prioritization.
- Flow of Data: The flow of data refers to the movement of data across a computer network. A well-designed network should have efficient and reliable data flow to ensure data is transmitted accurately and promptly. This is achieved through network design, routing protocols, and error detection and correction techniques.
- High Performance: High performance refers to the ability of a computer network to provide fast and efficient data transmission. High-performance networks can handle large amounts of data quickly and efficiently, allowing for fast communication and data transfer. This is achieved through network optimization, high-speed connections, and load-balancing techniques. Achieving high network performance requires careful planning and implementation of network infrastructure and technologies. This includes high-speed data connections, optimized network protocols, and efficient data routing and delivery mechanisms. Network designers and administrators must also ensure that the network can scale up or down to accommodate changing usage patterns and growing user demand.
- Security: Security protects data and network resources from unauthorized access, theft, and damage. A secure network should have measures to prevent and detect security threats, such as firewalls, encryption, and intrusion detection systems. Security is achieved through various security protocols, policies, and procedures.
- Fault Tolerance: Fault tolerance refers to the ability of a computer network to continue operating even in the presence of hardware or software failures. A fault-tolerant network should have redundant components and backup systems to ensure that failures do not cause service interruptions. This is achieved through redundancy, failover mechanisms, and disaster recovery procedures.
- Scalability: Scalability refers to the ability of a computer network to accommodate growth and increasing demands on resources. A scalable network should be able to add more users, devices, and data without significant degradation in performance. This is achieved through distributed architectures, virtualization, and cloud computing technologies.
- Compatibility with hardware and software components: Compatibility refers to the ability of a computer network to work with different types of hardware and software components. A compatible network should be able to communicate and interoperate with various devices and software applications, regardless of their origin or manufacturer. Compatibility is crucial for enabling interoperability and ensuring the network can support a wide range of users and applications. This is achieved through standardized protocols, interfaces, and APIs.
These basic characteristics are essential for building a reliable, secure, high-performance computer network that can accommodate growth and changing needs over time while remaining compatible with various hardware and software components.