Fixed and Flooding Routing Algorithms
Introduction
Before going to study fixed and flooding routing algorithms, we have to take a look back to revisit the topic of routing. Routing can be defined as
Routing: What is it?
Routing algorithms figure out the best route to take to get somewhere. Most of the time, packets must go via numerous hops in order to reach their destination. One of the trickiest and most important elements of a packet-switched network architecture is routing.
Routing Algorithm Properties
Routing algorithms have the following characteristics: they are reliable, stable, easy to use, optimum, and efficient. They should also be simple, and fair. The routing algorithm is only then regarded as being a decent routing algorithm.
Routing Techniques
There are different types of routing techniques available in routing algorithms. The list of the routing techniques is as follows:
- Flooding
- Fixed routing
- Flow-based routing
- Random routing
- Dynamic routing
Let's discuss the first two routing algorithms in this tutorial. These are fixed and flooding routing algorithms.
Flooding
A routing algorithm that doesn't require any network knowledge is called a flooding algorithm. Each neighbour will receive a packet that is sent by a node. All links except the incoming link will retransmit the incoming packets. In this routing algorithm, many copies reach their destination.
Each packet will have a distinct number, allowing duplicates to be thrown away from the packets. Packets may contain a hop count. To control network load, nodes can remember the packets that have already been forwarded. It takes every route that could exist.
Example
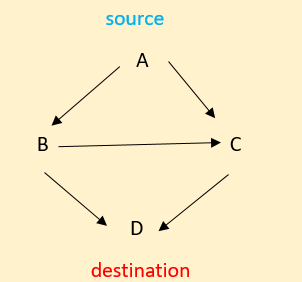
We are aware that every incoming packet—aside from the one it arrives on—is sent out on every other outgoing line. Flooding is the term for this.
From the above example we can observe that the A is the source and D is the destination. Every node sends the data packets in all the possible paths. But the main drawback is that the repetition of same data increases that means duplicate packets gets increased.
To stop and eliminate this duplicate packets. We have three ways to prevent this problem. They are
- Using HOP counter
Simply decrease in each router while delivering data packets from the source, and delete packets if the counter reaches 0. - Sequence numbering of packets
Every package must have a special number. It will refrain from delivering the same data packet again. also maintain a record of packets already observed in each router for each source. - Selective flooding
Use just the lines that appear to be heading in the appropriate direction.
Characteristics of Flooding
- There will at least be one quickest path once all options have been explored.
- Access is granted to every node that is directly or indirectly linked.
- We attempt every path between the source and the destination. A packet will always pass through if the route is there.
Limitations for Flooding
There are a few limitations to this routing algorithm in which a few drawbacks arise. The limitations are
- During flooding, a great deal of duplicate packets is produced.
- We should use an appropriate dampening mechanism.
Benefits of Flooding
The major advantages of flooding are
- The flooding algorithm is highly robust and communications may be transmitted immediately or in an emergency. And this algorithm will send messages to all nodes in a broadcast.
- This algorithm will create the virtual circuit for the route. The flooding process always takes the quickest route.
Fixed Routing
A technique known as a fixed routing algorithm establishes a defined path or route for transferring data packets from their source to their destination. The route is the "least-cost path," or optimal path, that the packet can take based on mathematical calculations. The routes are kept in routing tables, which can only be altered if the network topology changes.
- The benefits of this fixed route algorithm are that it is a simple routing algorithm. It will operate effectively on a steady network with a stable load. This is a similar routing algorithm for datagrams and virtual circuits.
- The major drawback of this fixed routing algorithm is that it is not flexible and it is not responsive to failure or network congestion.
The packets could not get to their destination if the routers malfunctioned. As a result, data packets are not duplicated. It does not cause needless traffic. There is no bandwidth wastage.
Conclusion
Finally, we conclude that data packets can be sent using flooding and fixed routing techniques across a network of intermediary routers linked by transmission lines.