Process of Penetration Testing
Companies or organizations use penetration testing manually or automatically to identify the system's vulnerabilities. All companies need to protect their assets and themselves from cyber-criminal attacks by updating their security measures simultaneously.
At the same time, it is difficult to know which and how the method is being used in the attack. Organizations hire skilled, ethical hackers to help identity, update and replace the defective or attacked parts of their system. Ethical hackers use penetration testing to detect weaknesses in the system because it is unique from other cyber security evaluation methods.
Depending on the organization's infrastructure and operation, penetration testing can be adapted to any organization or industry, but this follows a certain process that creates a set of results to help the organization. Let’s discuss the process of penetration testing step by step.
Stages of penetration testing
The penetration testing process starts long before a simulated attack. An ethical hacker is allowed to study the system to explore its strength and weakness and to identify the right tools & strategies to break into the system. Penetration is based on the structured procedure and performed step by step such as follows:-
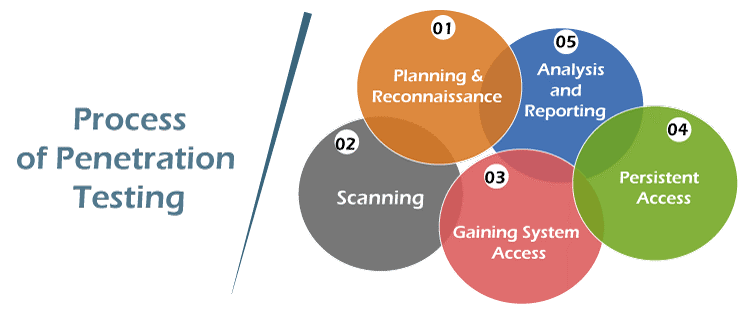
- Planning and Reconnaissance
This is the first step in the testing module, where planning and preparation are executed depending on the organization's needs. This step can be short or lengthy according to the requirement. Here, clients and testers properly aligned the test's scope, goal, and execution. They must have some knowledge about the tests like:
- What kind of test are they running?
- Who has to be aware about the test is running?
- With how much information and access permission tester should start the work
- Some of the other important details ensure that the test is a success
- Emails address and names of the company's employees to a network topology with the IP address, among others
- For the planning and searching process, these methodologies are used:
- Dumpster diving
- Social engineering
- Network scanning
- Domain registration information retrieval
- Discovery/ Scanning
After the planning phase, the discovery and planning phase is designed to identify the threats and how the target system responds to all the attempts at intrusion.
For the scanning purpose of initial vulnerabilities, the tester uses automated testing tools. This phase is necessary to obtain all the information about the system accurately, which includes usernames, passwords, and all the data in the system. This process is called fingerprinting. It probes and scans the ports where vulnerabilities exist. Here three types of discoveries are carried i.e.
Host discovery = It discovers the open ports on the devices
Service interrogation = In this, all the services running on ports are discovered by interrogating them
Network discovery = It includes the discovery of servers, additional systems, and other devices
- Gaining system access
After learning about all the system vulnerabilities, pen-testers mimic an actual attack in a simulated and controlled environment. This phase analyses how far a tester can get into an IT environment without detection.
After controlling a device, the tester performs a web application attack or a physical attack like cross-scripting or SQL injection attack. This pen tester infiltrates the system or infrastructure by exploiting security weakness, demonstrating how the target gets deep into the environment.
- Persistent access
In this step, once the penetration tester gets access to the device and holds the access or their presence as long as possible, it also simulates an attack long enough to accomplish & replicate malicious hacker goals. This phase is designed to obtain the maximum level of privileges and access to many systems as much as possible and network information by identification of data or services are available.
- Analysis and reporting
It is the last stage of penetration testing, where the testing team prepares a detailed report describing the entire penetration testing process. The pen tester writes all the detail of each step, consisting of how the pen tester took steps to in-filtrate systems and process, clean up after stress test, details of all the vulnerabilities, and suggestions for fixing the vulnerabilities.
Reporting is important for both parties because it is the base of working of the IT staff and non-technical managers; therefore, it is suggested to prepare a separate report. One part is on general explanation (executive report) and the other on a more technical aspect (technical report).