Bitcoin Mitigating Attacks
Bitcoin is the most secure & protected cryptocurrency, with security built into the protocol at numerous levels. It frequently executes persistent sophisticated attacks. In this part, we will look at numerous sorts of potential Bitcoin system attacks.
Sybil's Attack
The Sybil assault takes place on a peer-to-peer network. This assault on the Bitcoin network is intended by a hostile actor. In this case, a network node operates numerous identities at the same time, undermining the reputation system's authority. Its primary goal is to obtain the majority of network influence in order to carry out illicit operations in the system.
Although the Sybil attack is difficult to detect and avoid, the following procedures may be beneficial:
- By raising the expense of developing a new identity.
- Validation of identities or trust is required for network access.
- Give varying levels of authority to different individuals.
Race Attack
The recipients of the Race Attack must accept unconfirmed transactions as payment. As an attacker, you can use two distinct devices to send the identical coin to different vendors. If the sellers send the goods without first waiting for block confirmation, they will quickly discover that the transaction was denied during the mining process. The answer is for the vendor to wait at least one block confirmation before sending anything.
When an attacker has direct access to the victim's node, this attack is easy to execute. As a result, it is recommended that you disable incoming connections to nodes for accepting payments so that your node can identify its own peers. It also does not allow the payer to send the payment straight to the payee.
Finney Attack
The Finney assault takes its name from Hal Finney. One sort of double-spending problem is the Finney attack. The attacker in this attack is the miner who mines blocks normally. He includes a transaction in the block that returns part of his coins back to himself without publicising the transaction. When he comes across a pre-mined block, he sends the same coins in another transaction. Other miners would reject the second transaction, but this would take time. To avoid this attack, the vendor should wait at least six blocks before delivering the items.
Vector76 Attack
The Vector76 attack is a mix of the Race and Finney attacks, allowing the reversal of a transaction with only one confirmation. A miner launches this assault by establishing two nodes, one of which is linked one to the exchange node, and the other to the Blockchain network's well-connected peers The miner now creates two transactions, one of large value and one of low value. The assailant then generates a high-value transactionto a service of exchange He transmits the pre-mined block to the exchange service as soon as a fresh block is revealed. When the high-value transaction is confirmed by the exchange provider, the infected attacker is released. submits the low-value transaction to the Blockchain network, that rejects the high-value transaction at the end As a result, the high-value transaction's value has decreased. gets put into the corrupted attacker's account. This attack can be avoided by limiting incoming connections and connecting only to nodes that are well-connected.
The 51% Attack
The 51% assault is a possible attack on the Blockchain network. It refers to a single miner or group of miners attempting to control more than 50% of the mining power, processing power, or hash rate of a network. The attacker can prevent fresh transactions from taking place or being confirmed in this attack. They can also reverse transactions that have already been confirmed while in control of the network, resulting in a double-spending problem.
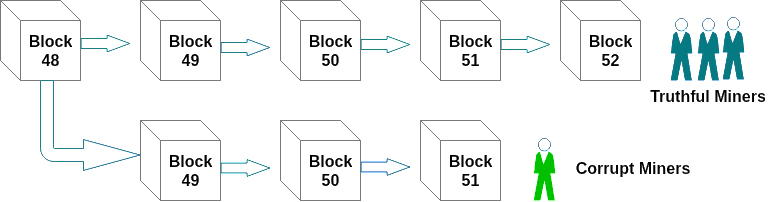
When a miner creates a legitimate block of transactions, the block is broadcast to certain other miners just on network. It can only be approved if all transactions in a block are valid according to the Blockchain's existing record. A corrupt minor who controls more than half of a network's hash rate, on the other hand, doesn't make solutions available to the rest of the network As a result, the establishment of two Blockchain versions. The first is the public version of the Blockchain, which is used by legitimate miners. The second method is utilised by corrupt miners who do not publish it to the rest of the network.
The dangers of a 51 percent attack
Users of cryptocurrency may lose digital assets or even cash as a result of a 51 percent attack. This raises severe questions regarding a Blockchain's dependability, security, and integrity. The trust of its consumers and miners is severely shaken.
Attackers can trick unskilled and new users into validating and confirming transactions that they can subsequently invalidate. The reason for this is that attackers can disrupt unconfirmed blocks and transactions on a Blockchain.
Furthermore, the attackers may not confirm or even reverse the victims' transactions. This causes consumers to distrust the Blockchain, causing its value to fall. Because of security concerns, these kinds of assaults may force some cryptocurrencies to be delisted.
This form of assault is imaginary because it is expensive to obtain computing power, which accounts for more than half of the total processing power of the network.