Blockchain Block Hashing
Blockchain is the main technology used for digital cryptocurrencies like Bitcoin. Blockchain consists of a database that has all the records of digital events that have taken place or all the transactions that have taken place. The participant's system itself verifies every transaction. It stores every record of the transaction that has taken place. To understand how the Blockchain works, it is very important for us to learn how the concept of Hashing takes place.
The Blockchain network is divided into three main parts-
Block or Node -
It is known as the main building block of the Blockchain. It almost performs similarly to a database and stores all the information related to transactions. The records which are present contain the records that are recorded in that particular Blockchain. The period, triggering event, and size vary for each & every block in the Blockchain.
Network -
The network always consists of full nodes. You can visualize them as a computer running on an algorithm that secures the network.
Hash -
This is the most difficult topic of Blockchain. Hash helps to link one block to another and acts as a chain. Hashing is a process of chaining all blocks together. It works like magic, which connects Blockchains and allows them to maintain security and privacy, and helps to create mathematical trust. We call hash the fingerprint of data because it locks and connects blocks in time and order.
Blockchain Block Hashing -
This Secure Hash Algorithm-256 is applied to construct a block within a Blockchain. The role of miners is to build blocks, and the blocks are added to the Blockchain to construct the Bitcoin Blockchain. We will know how the bitcoin Blockchain ties or links into the miner's role.
Let's look into the image and the block consists of a data field, cryptographic hash, Nonce, and block numbers-.
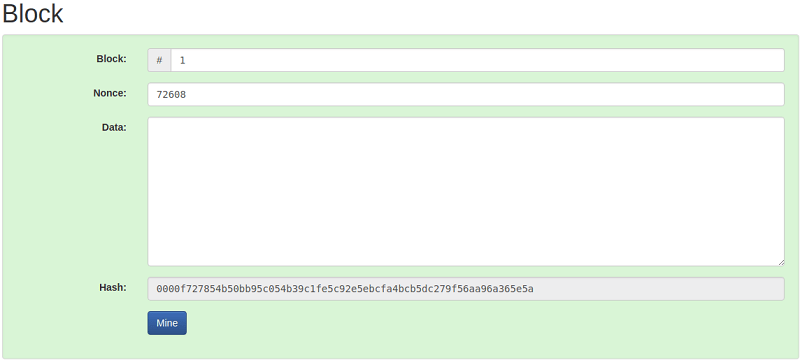
The hash which is generated will look like 00001acdm010fgh0101xxx. The main thing to notice in this is that it has four zero leading. When it comes to practical purpose, you will see that hash always corresponds to Nonce and block number corresponds to available data. It is a valid block because the hash consists of four leading zero's.
If any changes are made in the data section, it will produce a completely different hash that is shown below-
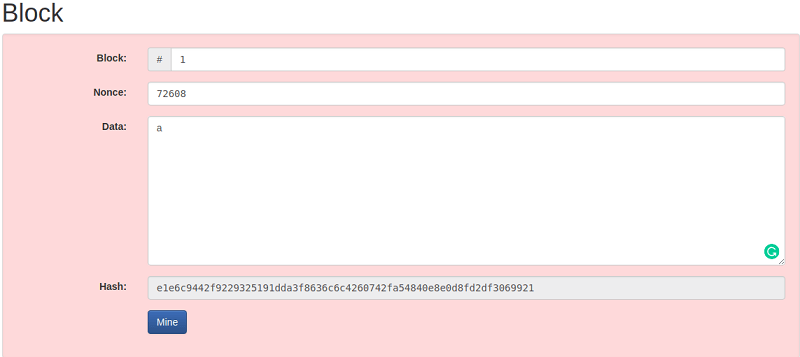
If the hash doesn't consist of four leading zero, it is not a valid block. Nonce field is used to make the block valid.
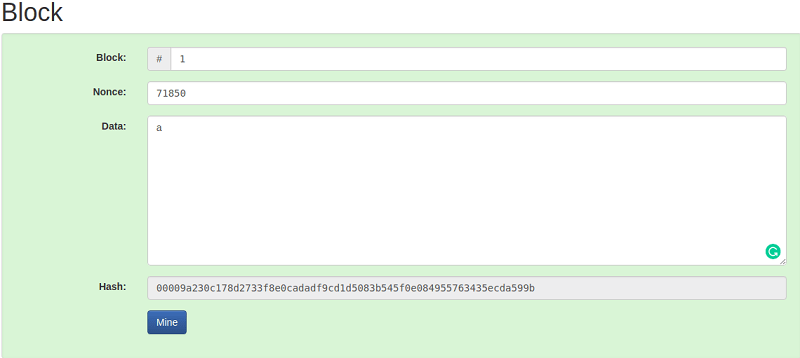
The full form of Nonce is a Number Used Once & it is used in cryptographic communication so that the hash block meets certain standards.
The Nonce is a block that figures outs how this block will give you a valid hash with a random number. Usually, miners start with value one of Nonce, and they keep on increasing till the generated hash meets the specified standard. Thus it takes several attempts until four leading zero's are generated. The time required to create a bitcoin is ten minutes. The release of the block in the system is done once the minor successfully mines the block.
When you click on the mine button under Anders Brownworth Hash, it will produce a valid block & this block is unique because it has a hash leading with 4 zero in the starting.
Applications -
- Used in Sign verification and generation-
To create an efficient & secure digital sign scheme, we use the integrity property of the cryptographic hash. All the digital signs require a cryptographic to be calculated or counted above the message. This message is verified if the signature verification is successful.
- Used in password verification-
The password entered by the user is compared and hashed with the stored or present data. An original password that is present cannot be recalculated from the present or stored data, and for this reason, password hashing is always performed.
- Used for verification of messages and files-
The main application of a secure hash is to verify the message's integrity. It compares the message digits calculated after and before, and the transaction can then decide whether any changes are made to the file or message.