Blockchain Hash Function
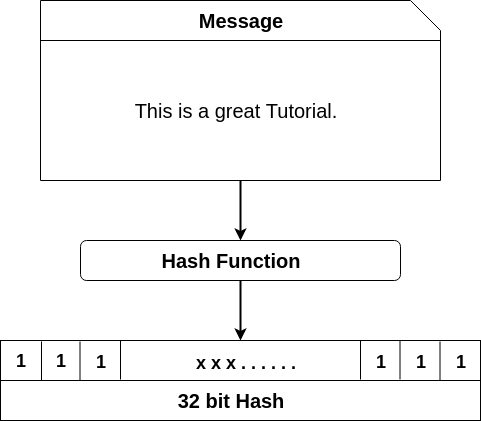
A hash function is a type of function which takes input in string format (alphabets, media files, numbers) of any length provided by the users and converts it to a fixed length. Depending on the hash function used, the bit length may vary from 256-bit or 128-bit or 64-bit or 32-bit.The cryptographic by-product of hash algorithm is also hash.
Cryptographic hash functions
SHA-2 and SHA-3(Secure Hashing Algorithm) .
RIPEMD (RACE Integrity Primitives Evaluation Message Digest) .
MD5 (Message Digest Algorithm 5) .
BLAKE2.
Hash algorithm contains certain properties such as-
- It follows one-way function.
- It gives unique output or hash.
Bitcoin is a cryptocurrency and it contains Blockchain which uses cryptographic hash function. A hash is a digital fingerprint or a digit which has a certain quantity of data in it. In cryptographic hash, the input is a transaction and is run or passed through hashing algorithm which produces a output with a fixed size.
Secure Hash Algorithm - 256 -
A secure hash algorithm is an algorithm used in Bitcoin Blockchain. It is developed by NSA (National Security Agency) in USA in the year 2001.
How does Hashing Process work?
We use programs which are developed by Anders Brownworth for the hash function.
You can find the program of Anders Brownworth regarding hash function on : https://anders.com/Blockchain/hash.html.
Secure Hash Algorithm 256 Hash-
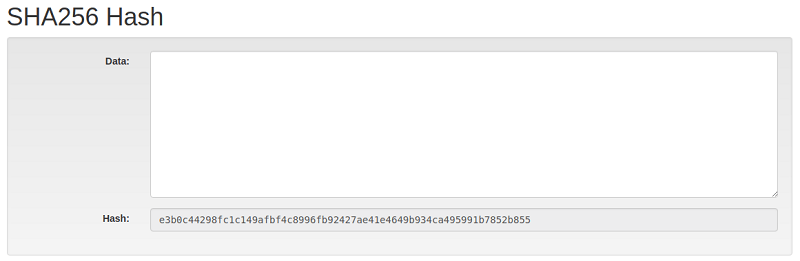
We can see the corresponding cryptographic hash in the section of hash whenever we type any character in data section.
For example-
If you type “This is a great learning platform” in data section then-
It will generate -
4bc36380892ed7885df411abe1fa5gc3e83ab2db76f76dc83e1bbecf48d61019 hash.
There can be three possible scenarios
- Best case-
You get the answer on first run or try.
- Average case-
We get huge or big numbers in answer.
- Worst case -
We get the answer but it is present at the end of the data.
Note: If we write same test repeatedly in the data section, then it will always produce the same output no matter what so ever.
Hash functions are always one-way functions; there are no ways to get back the complete text which is generated from hash. This is completely different from the earlier cryptographic functions which used to have the encryption where one can do the encrypt using the key & by the help of description, you can decrypt the message to the earlier form (original form).
Hash function in the mining process -
Let see the validation process of Bitcoin network, a block usually contains many transactions and also contains the information of the previous blocks. This specifies that if someone wants to double - spend on a transaction or alter the ledger then he or she can do the changes to the hash in all the previous blocks which are present.
In order to add the bundle block to Blockchain, miners are supposed to find the hash which meets the target difficulty. Each block always contains a block header in it and it consists of several no. of blocks. The hash of nonce & the previous block also contains a timestamp. The nonce is used or is present because the different input given to the cryptographic hash function which will intern increase the randomness and in the counting during the mining process.
How Hash value is calculated -
It uses very complex mathematical algorithms which help to convert the data of random length of data to a fixed length of data (256 characters). If there is a change of even a bit in the original data then complete hash value is changed and this makes it helpful to verify the accuracy of digital files and other data which are present.
Hashes used in Blockchains-
Blockchain system uses hashes in its several parts. The block header is present in hash of each block of the previous block that ensures that nothing has disturbed when the new blocks are added. PoW (power of work) is used in cryptographic mining and it utilizes the hashing of unsystematically generated orders to arrive at a mentioned hash value containing sequence of leading zeroes. These arbitrary functions are resource-intensive and this makes it difficult for bad actor to overcome the network.