Data Encryption Standards
The Data Encryption Standards was introduced by the National Institute of Standards and Technology. A Feistel Cipher is implemented in DES. The Data Encryption Standards was developed by the company named IBM in the early 1970s and the development of this system is based on the inventions of Horst Feistel.
The popularity of the Data Encryption Standard (DES) has been discovered to be slightly declining because of the discovery that DES is susceptible to very strong attacks. Data encryption standard usually works based on block cypher, and it encrypts the data in 64bits each. The key is 56 bits long.
History of Data Encryption Standards
The National Bureau of Standards first studied the security of US government computers in 1972 and found a need for a government-wide standard for encrypting sensitive, unclassified data. This is when DES was born.
How does Data Encryption Work?
As a result, the original 64-bit key is reduced to a 56-bit key by throwing away every eighth bit of the key. DES is built on substitution (also known as confusion) and transposition, two key components of cryptography (also called diffusion). Each of the 16 steps in DES is referred to as a round. In Data Encryption standards, all the 16 steps are a single round. The stages of substitution and transposition are carried out in each round.
- The 64-bit plain text block is sent to the initial Permutation (IP) function in the first phase.
- The first permutation is applied to plain text.
- The encryption process now includes 16 cycles for both LPT and RPT.
- After reuniting LPT and RPT, the combined block is sent through a Final Permutation (FP).
- This procedure generates 64-bit ciphertext as the result.
Steps in Data Encryption Standards
There are three steps in the Data Encryption.
- Initial Permutation
- Key Transformation
- Expansion Permutation
Initial Permutation
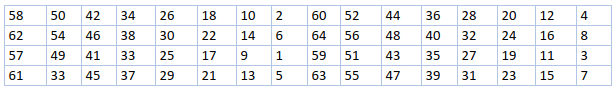
Before the first round, the initial permutation (IP) occurs only once. As seen in the graphic, it makes suggestions for how IP transposition should go. Nothing more than a bit-position juggling game with the initial plain text block is being done here. All other bit locations are subject to the same regulation.
Simple bit-position juggling with the initial plain text block is all that is involved in this. The same principle applies to all other bit places shown in the illustration.
Key Transformation
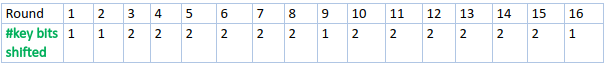
As mentioned, the initial 64-bit key is reduced to 56 bits by throwing away every eighth bit. Consequently, a 56-bit key is accessible for each. A procedure known as key transformation is used to create a unique 48-bit Sub Key from this 56-bit key throughout each round. The 56-bit key is split into two parts, each of 28 bits, for this purpose. Depending on the round, these halves have a circular left shift of one or two locations.
For instance, if the round number is 1, 2, 9, or 16, the circular shift is carried out by two positions for additional rounds. The figure displays how many key bits are shifted per cycle.
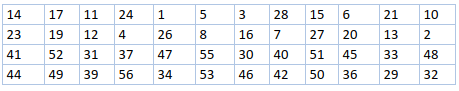
48 of the 56 bits are chosen after the proper shift. The table is depicted in the image below for choosing 48 of the 56 bits. For instance, bit number 14 shifts to the first position following the shift, followed by bit number 17, and so on. We can see that the table only has 48-bit positions if we look at it closely. To decrease a 56-bit key to a 48-bit key, bit number 18 is eliminated along with 7 other bits (bit number 18 will not appear in the table).
Expansion Permutation
The term "expansion permutation" refers to the permutation of bits as well. This occurs because the 32-bit RPT is split into 8 blocks, each of which has 4 bits. Then, after adding 2 extra bits to each 4-bit block, each 4-bit block from the previous phase is increased to a corresponding 6-bit block. While producing output, this process causes the input bit to expand and be permuted. The 56-bit key is compressed to 48 bits during the key translation procedure. The 32-bit RPT is then expanded to 48 bits by the expansion permutation method. The 48-bit key and 48-bit RPT are now XORed before the output is given to the S-Box substitution.