Blockchain Data Management
As we all know, Blockchain is a distributed systems that follows peer-to-peer network and acquire the benefits of peer-to-peer networks such as speed, single-point failure avoidance, and so on.
The Peer-to-Peer networks are depicted in the figure below.
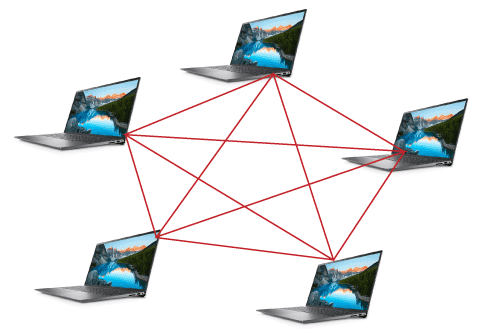
Each node is connected to others and distributes resources; therefore there is no reliance on central machines like in traditional client-server architecture.
Data Management on Chain
In this lesson, we'll look at how data is saved on Blockchains and what each block just on Blockchain contains. Each transaction is broken down into smaller chunks, each referred to as a block.
For example:
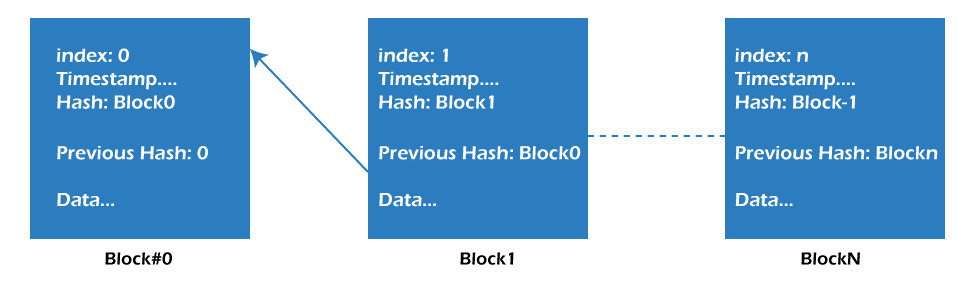
Some of the blocks in the diagram above include real transaction data. Aside from transaction data, every block has additional similar properties, such as these:
Index: The term "index" simply refers to a number that represents a consecutive block no.
Timestamp: The date on which the information was added to the block.
Hash: It's a one-of-a-kind hash value that's used to identify data. Mathematical formulas are used to produce it. Each block has its own hash value, which directly interacts with one another when data is updated (i.e., if the data is changed, the hash value will be modified as well).
Previous Hash: In order to obtain references backward, that has data for the hash of prior blocks.
Immutability over Blockchain
We're all aware of the benefits of databases. Create, Read, Update, and Delete (CRUD) activities are the foundation of traditional databases. However, Blockchain can only append and retrieve data, which means that it can't be erased or modified after it's been added.
Any node with access to the ledgers on the Blockchain may verify and check if the ledger has been tampered with, and whether any transaction in either block has changed. This is usually accomplished by computing a hash function value of the block's data and compares it to the hash values of prior blocks within next block.
Example:
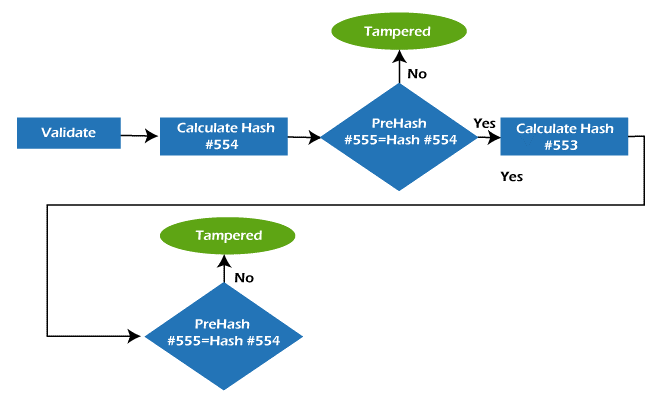
The Blockchain is shown here, with Block#555 as the most recent block.
The peer or node in this case may ascertain the hash value of block#554 and if the hash value for block#554 is the same as the value for block#555. If it isn't, the block is considered to be compromised. The verification process is shown in the diagram below.
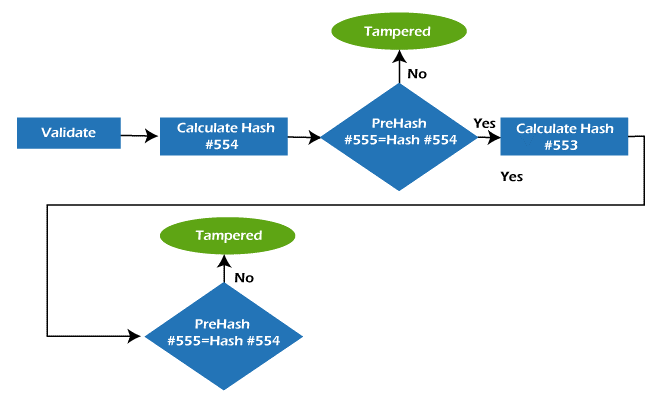
If the data is changed & invalid validation fails, all nodes will reject the block.
To validate transactions, Blockchain employs the consensus (general agreement) approach.
Blockchain Consensus
It's a way in which peers agree on the ledger's present status. It ensures that all peers have access to the same ledger copy. False transactions are not recorded in the ledger. It also guarantees that transactions are recorded in a chronological way.
Here's a quick rundown of the consensus processes that apply to everyone.
Protocols of Common Consensus:
1. Proof of Work: Proof of Work (PoW) is the certification of completed work and proof that it is accurate, as the term indicates. This is the consensus process used to confirm the chain's legitimacy.
PoW's main disadvantage is that it needs greater electrical power and high-end computing gear, both of which can be costly.
2. Proof of stake: PoS (Proof of Stake) is a distinct technique of validating and verifying a block or transaction. The validator is chosen via PoS based on the stake held by the validator and their stake age. The validated player earns the full or a portion of the transaction fee in PoS.
PoS solves the primary problems of PoW which is said to have an advantage because it does not require expensive hardware. Because it uses less electricity, it is also more energy efficient than PoW.
3.Tendermint: The Tendermint is an open-source project that intends to overcome the size, performance, and environmental concerns of Bitcoin's Proof-of-Work consensus mechanism. The Byzantine fault-tolerant consensus (BFT) algorithm is employed. In the Bitcoin and Ethereum Blockchain networks, Proof of Work is employed.
What is the Business Appeal of Blockchain?
A big portion of the appeal stems from the technology's distinctive characteristics. A Blockchain is a series of blocks linked together by a cryptographic hash of the block before it. A timestamp and transactional data are also included in the blocks. Blockchain is immutable, as it can only be broken with the network's consent. This implies it's absolutely safe and can't be tampered with. It is also unique in that it's decentralised, which means it's not run by a single authority. Public and private Blockchain networks exist, with the latter requiring network authorization to join.