Flooding in Computer Network
Introduction
Flooding is a routing approach in computer networking where a sender node sends messages via all outbound connections. Flooding also occurs in the same way that broadcasting occurs when sender packets are sent to every connected network node without any routing information.
Flooding techniques are made to identify and use the shortest routes possible for packet transfers because flooding inherently uses every way in the network. Flooding may also be employed to soak network traffic to bring down a network using D.O.S. (Denial of Service) assaults.
Flooding
Static routing methods like flooding operate on a fundamental rule:
" Once a packet reaches a router it is routed to all outbound connections except the connection from which it originated."
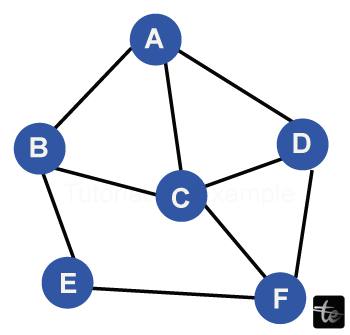
Peer-to-peer file transfers, connecting, Usenet, torrenting, routing algorithms, and peer-to-peer networks all employ flooding. To better comprehend this, let's look at an instance. Presume, as in the following diagram, that transmission lines connect a network of six routers.
What Happens During Flooding in computer networks is listed below.
- D, C, and B get every package that arrives at A.
- To E and C, B forwards this packet
- To F, D, and B, C forwards this packet
- D forwards F and C this packet
- F receives the package from E.
- E and C get a package from F.
Types of Flooding in computer networks
Three types of flooding commonly occur in computer networks:
Uncontrolled Flooding
Every node shares the packets unrestricted to all other nodes under uncontrolled flooding. If conditional reasoning is not there to prevent the unrestricted resending of the same box, broadcast emergencies might turn disastrous.
Controlled Flooding
Because of its two methods, controlled flooding is more dependable:
- Sequence Number Controlled Flooding (SNCF): Every node has storage space for addresses and series numbers, so it attaches its unique addresses and serial numbers to the packets. If a node receives a packet already in memory, it dumps the packet right away.
- Reverse Path Forwarding (R.P.F.): A packet is only sent from a single node to another in the forward direction. The package is returned to the sender if it originated from the subsequent node.
Selective Flooding
This type of flooding only sends messages to routers in one direction. Routers only send packets on those connections, pointing in roughly the right order, rather than broadcasting every received packet on every link.
Features of Flooding
Here are a few characteristics of flooding:
- Every path between the origin and the intended recipient is explored in flooding.
- At least one fastest path is always available.
- Every linked node—directly or indirectly—is investigated.
- The network's structure, load levels, prices of different pathways, and other details are unnecessary for flooding. Consequently, it lacks adaptability.
Benefits of Flooding
- Finding the quickest path is always the goal of flooding.
- Neither node is likely to be overlooked since every linked node—directly or indirectly—is investigated.
- Flooding is excessive. Nevertheless, packets manage to reach their destination even when many routers fail.
- A router can only learn about other routers. Therefore, flooding is very simple to set up and execute.
Drawbacks of Flooding
- A network can get jammed by repeated, illegal data transmissions. Additional data packets may be hampered as a result.
- Because flooding broadcasts the data packet to all nodes unconditionally, it turns wasteful when only one target needs the package.
- When flooding occurs, it helps create an endless amount of duplicate data packets unless logic is in place to restrict the number of packages that may be made.
- The wasted bandwidth caused by flooding is costly. Messages must be transmitted to every host, even if only intended for one.
- Network dependability may be harmed by flooding that results from D.O.S. (Denial of Service) attacks or ping floods.
Conclusion
- When sending packets across all outbound connections, a sending node uses a method called flooding to route the computer network.
- Peer-to-peer file transfers, connecting, Usenet, torrenting, routing algorithms, and peer-to-peer networks all employ flooding.
- Controlled, uncontrolled, and selected flooding are the three forms of flooding.
- Finding the quickest path is always the goal of flooding.
- A router can only learn about other routers. Therefore, flooding is very simple to set up and execute.
- A network can get blocked by repeated, illegal data transmissions. Additional data packets may be hampered as a result.
- Network dependability may be harmed by flooding that results from D.O.S. (Denial of Service) attacks or ping floods.