Stream Control Transmission Protocol
Stream Control Transmission Protocol: SCTP stands for Stream Control Transmission Protocol. SCTP was developed by the Internet Engineering Task Force (IETF). It is a reliable message-oriented protocol of the transport layer. It provides the best features of the TCP and UDP. It is designed for specific applications, such as multimedia.
SCTP Services
- It provides process-to-process communication like UDP and TCP.
- It allows the multi-stream service in every connection of device that is called association. In the device, if one connection is blocked, the other connection may still deliver that data.
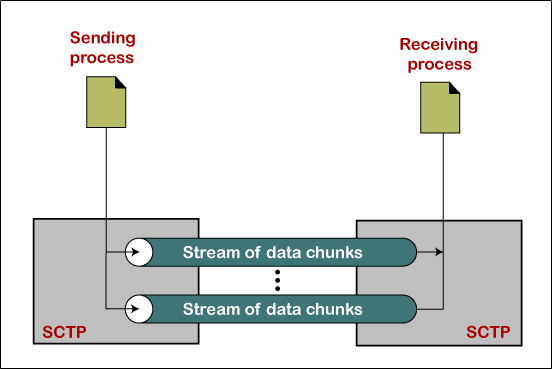
- It offers a full-duplex service like TCP, where the data can flow both directions at the same time.
- It uses the acknowledgment (ACK) mechanism to validate the data delivery.
SCTP Packet Format
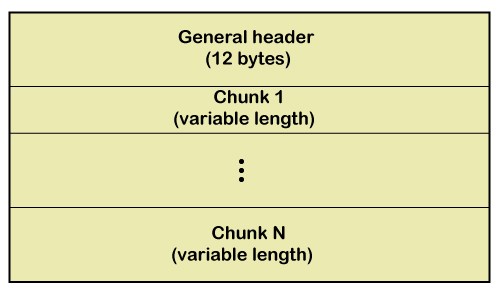
The SCTP packet contains a general header and a group of blocks that is called chunks. There are two types of chunks in the SCTP packet: control chunks and data chunks. The first chunk of the packet maintains the association, and the second chunk of the packet carries the user data. The control chunks arrive in the packet before the data chunks.
The general-header format of the SCTP is shown below.
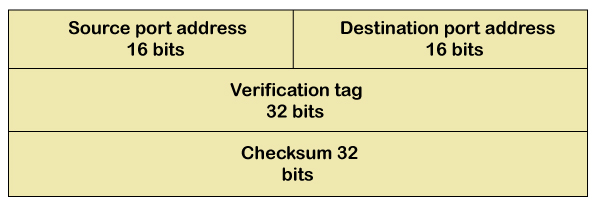
In the general header, there are four fields.
- Source Port Address: The size of the source port address is 16 bits. It defines the port number of the process that is sending the packet.
- Destination Port address: The size of the destination port address is 16 bits. It defines the port number of the process that is receiving the packet.
- Verification Tag: The size of the verification tag is 32 bits. This field is used to check that the packet receives from the correct sender or not.
- Checksum: The size of the checksum is 32 bits.
Comparison of SCTP, TCP, and UDP
| Services | UDP | TCP | SCTP |
| Sequence data delivery | No | Yes | Yes |
| Multi-Streaming | No | No | Yes |
| Multi-Homing | No | No | Yes |
| Connection-Oriented | No | Yes | Yes |
| Connection-less | Yes | No | No |
| Allows half-closed connection | N/A | Yes | No |
| Application PDU bundling | No | Yes | Yes |
| Congestion Control | No | Yes | Yes |
| Application PDU fragmentation | No | Yes | Yes |
| Preserve message boundaries | Yes | No | Yes |
| Partial reliable data transfer | No | No | Optional |
| Selective Acknowledgements | No | Optional | Yes |
Congestion
Congestion: If the network load is more than the network capacity, such a situation is called the congestion.
Congestion control: It refers to the mechanisms that are used to control the congestion and keep the traffic below the capacity of the network. Congestion control is divided into two categories: Open-loop and Close-loop, which are shown below in the figure.
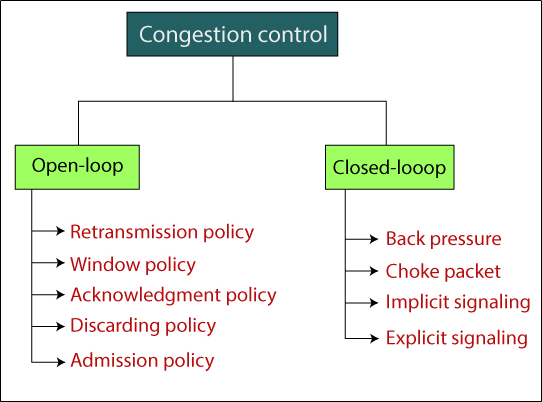
Open-loop congestion control
The open-loop congestion control strategies are implemented to stop congestion before it occurs. The congestion control is controlled by either source or destination. Open-loop congestion control is divided into some categories.
- Retransmission Policy: It is the policy in which the packet is sent again. When the sender perceives that the transmitted packet is lost, the sender sends that packet again.
- Window Policy: In window policy, uses the selective repeat window method to control the congestion.
- Discarding Policy: The less sensitive packets can be discarded by the routers to ensure congestion.
Closed-loop congestion control
The closed-loop congestion control strategies attempt to reduce congestion after it happens. Closed-loop congestion control is divided into some categories: Back-pressure, Choke-point, Implicit signaling, and Explicit signaling.