Difference between NFC and RFID
This article will provide you with a detailed comparison between NFC and RFID technologies. Before diving into the main context let us understand what are NFC and RFID technologies.
What is NFC?
Using a wireless communication technique called Near Field Communication (NFC), two devices can communicate data simply which are located within a few centimetres of one another. NFC is a type of radio-frequency identification (RFID) technology.
NFC is widely used in a range of applications, such as mobile payments, contactless ticketing, access control, and data sharing between devices.
For example, you can use your smartphone to tap an NFC-enabled payment terminal to make a purchase or tap an NFC-enabled poster to receive information about a product or event.
NFC is a secure and convenient way to exchange data and it uses a technology called a "secure element" to protect sensitive information. The secure element is a chip that stores and encrypts data, and it can only be accessed by authorized parties.
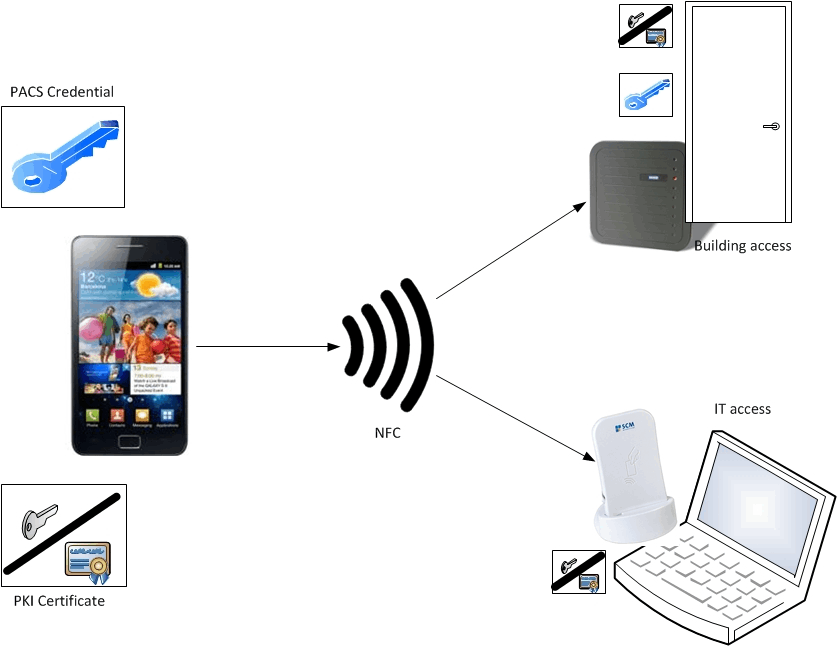
One of the unique aspects of NFC is its ability to operate in two modes: active and passive. In active mode, both devices generate a radio signal, and they can exchange data in both directions. In passive mode, one device generates a radio signal, and the other device only responds to it. The majority of contactless payment systems employ this method.
In summary NFC is a wireless communication technology that enables devices to exchange data with just a tap. It is a secure and convenient way to perform a variety of functions, and it is widely used in mobile payments, contactless ticketing, and access control.Bottom of Form
What is RFID?
Wireless technology called Radio Frequency Identification (RFID) uses radio waves to identify and track items.
It consists of a reader that communicates with the tag and a tiny chip or tag that is attached to an item. When the tag is brought within the range of the reader, it is powered by the reader's radio waves, and it sends back a unique identifier or other data to the reader.
RFID technology has many applications in industries such as retail, healthcare, logistics, and manufacturing. It is used for inventory management, supply chain optimization, asset tracking, and security. RFID tags can be attached to products, vehicles, and even living beings, and they can be read without a line of sight or direct contact.
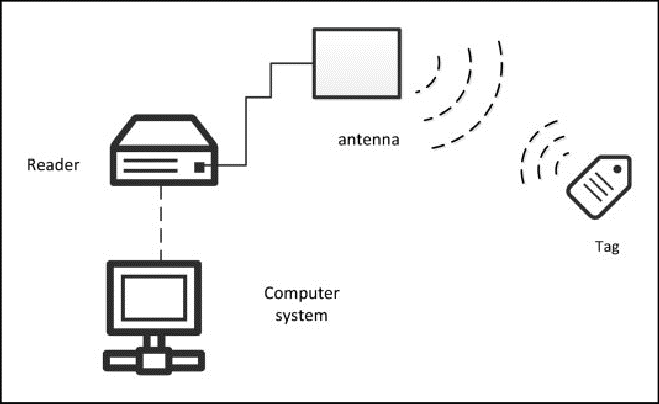
RFID tags come in two varieties: passive and active. Passive tags rely on the reader's radio waves for electricity because they lack a power source of their own. They are smaller and less expensive than active tags, and they are often used for inventory management and asset tracking. Active tags have their power source, and they can transmit data over longer distances. They are often used for vehicle tracking, cargo monitoring, and other applications where longer-range communication is required.
RFID technology has many benefits, including improved accuracy, efficiency, and security.
It can help organizations track and manage their assets more effectively, reduce inventory costs, and improve supply chain visibility. However, RFID also raises privacy concerns, as it can be used to track individuals without their knowledge or consent. To address these concerns, many RFID systems include privacy safeguards, such as encryption and access control.
Differences between NFC and RFID
| Aspect | Near field communication(NFC) | Radio Frequency Identification(RFID) |
| 1. frequency | Operates at 13.56 MHz | Operates at 13.56 MHz |
| 2. Range | Short range, typically within a few centimetres. | Can operate over a longer range, depending on the type of RFID. |
| 3. Communication | Two-way communication between devices. | Reader and tag only have one-way communication. |
| 4. Power | Only one-way communication is possible between the reader and the tag. | Passive RFID tags require an external power source to operate. |
| 5. Security | Uses a secure element to protect sensitive data. | Security features may vary depending on the type of RFID. |
| 6. Data Transfer | Can transfer data at a higher speed. | Transfer of data may be slower compared to NFC. |
| 7. Applications | Primarily used for mobile payments, access control, and data sharing between devices | Widely used in inventory management, supply chain optimization, and asset tracking. |
| 8. Size of the tag | Generally smaller than RFID tags. | Can be larger than NFC tags depending on the application. |
| 9. Types of tags | Only one type of NFC tag. | Several types of RFID tags such as passive, active, and semi-passive. |
| 10. Reader | Both devices generate a radio signal in active mode. | The reader generates a signal to power the RFID tag in passive mode. |
| 11. Compatibility | Can only communicate with other NFC devices. | RFID tags can communicate with different readers depending on the frequency used. |
| 12. Interference | Less susceptible to interference from other signals. | Can be affected by electromagnetic interference. |
This is all about the comparison between NFC and RFID. Hope you understood this topic.