Mesh Topology Diagram in Computer Network
Topology in simple terms can be defined asthe arrangement of a computer network, which is further divided into logical and physical arrangements. Logical arrangement refers to how the data flow inside the computer whereas, for physical arrangement, it refers to the connection made on the network.
Mesh topology is a type of network topology where all the devices are interconnected in the network. It is a type of network topology which has multiple ways to travel the information to the connected nodes. This topology network is commonly used for wireless connections. Further, this topology consists of two techniques which are known as 'flooding' and 'routing', where messages or information are being sent by hopping from one node to the other until it reaches its final destination.
Mesh topology can include hundreds of wireless mesh nodes. It is the best example of a wireless network which are used these days, and the best example that we can give of this network is the internet itself.
Wireless Mesh Network (WMN) is a mesh network, which comprises various nodes that are wireless. The nodes of this network help in transferring various data.
The structure is easy and simple to understand. WMN helps in connecting people who are staying or working in remote areas. Further, this network works better with other types of networks as it is very flexible.
Also, wireless mesh networks are more stable as compared to other topologies. This network works with the help of mesh nodes, mesh clients, and gateways.
- Mesh nodes refer the radio system,
- Mesh clients refer to all the wireless connections,
- Gateways refer to the infrastructure where various wireless nodes are connected.
WMN network consists of nodes that are not required to be cabled for the information to transmit.
Diagram of Mesh Topology
Below is the diagram showing how various computer and network devices are connected with each other.
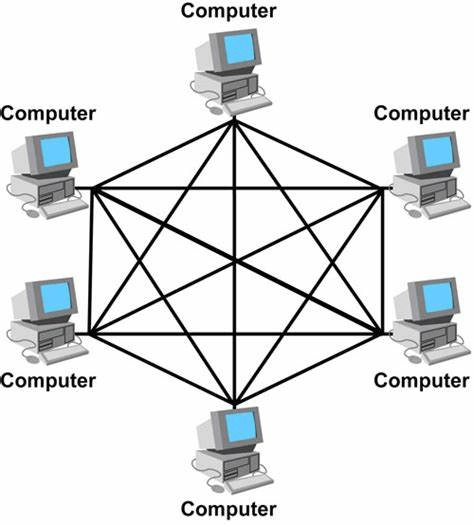
The connections which are being shown in the above diagram make sure that the connections between the computers cannot be broken or disconnected. And also that the nodes which are being created help in transmitting the data in the network in a proper and appropriate way.
Types of Mesh Topology
There are two types of mesh topology and they are:
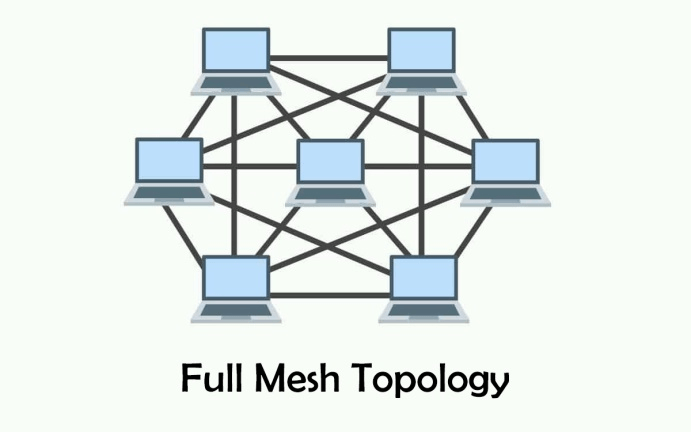
1. Full Mesh Topology:
In this topology, all nodes are connected with each other directly. Full mesh topology is considered to be the best topology as it provides multiple ways in order to succeed at the particular destination. Further, it provides high security and a single failure does not disrupt the entire process. Also, this topology has direct links with all pairs of nodes. And so, it works well in small network connections, but when the connection devices increase network issues arise.
Full mesh topology is often used for server connectivity. But above all this, the disadvantages of full-mesh topology are that its cable is expensive and further that it is not easy to troubleshoot. In a full mesh network devices are interconnected with each other.
2. Partial Mesh Topology:
This topology is the same as full mesh topology, but the only difference is that in this topology all the nodes are not connected with each other. This topology minimizes the hops. Further, it creates better management of the datasets. It is used commonly in peripheral networks. It is less complex as compared to the full-mesh topology. However, the setup of this partial mesh topology is tough.
Advantages and Disadvantages of Mesh Topology
There are several benefits or advantages of mesh topology and they are:
- Messages in mesh topology are received on a quick node if the route is short.
- Nodes can be added easily without any interruption.
- It is easily replaceable if attacked.
- It has better security.
- Mesh networks have a great range which means that signals can transmit to great distances.
- It is more stable.
- It can easily manage high-level traffic.
- It is more reliable.
- Its data load can be carried by itself only.
- Troubleshooting is easy in this topology.
The various disadvantages are:
- Its structure is complex.
- It is expensive compared to others.
- Its power consumption is more.
- It requires a lot of maintenance because of many connections.
- In this topology, the installation process is extremely difficult.
- More cable work is required as compared to other topologies.
Application of Mesh Topology
- Mesh topology network can and is being used both in small as well as large organizations. It is used in homes, industries, and also for public service communication.
- Mesh Topology is often used by military organizations in order to stop or avoid communication breakdowns.
- Mesh topology is being used in cities in a rapid manner, where street lighting, traffic lights, etc are being controlled wirelessly.
- Also, emergency services such as hospitals, police services, fire services, etc use mesh topology so that they can be easily in touch with each other.
- Overall, the best example which can be given about mesh topology is the internet, which is being used in our daily life, where various pieces of information are being shared worldwide.
Conclusion
In a mesh network topology, each device on the network is connected to multiple other devices, forming a mesh-like structure. It is more systematic in terms of network resources. Mesh networks are often used in situations where reliable communication is important. This network offers several benefits, including increased reliability, flexibility, etc. It is more complex for networks to set up and manage other types of networks. Also, the increased number of connections in a mesh network can result in higher overhead and slower communication speeds