Uses of Computer Networks
During the twentieth century, the most significant technology is information collecting, processing, and distribution. Computers and communications have been integrated, which has considerably influenced the organization of computer systems.
The previous paradigm, in which a single computer served all of an organization's computing needs, has been replaced by a new system which accomplishes the job. Computer networks are the name given to such systems.
Computer networks have proven important to both businesses and people. The following are some of its primary applications:
Sharing of Information and Resources: Computer networks enable businesses with dispersed components to communicate information efficiently and effectively. Any computer's programs and software can be accessed by other computers connected to the network. With the help of this feature, we can also allow the user to share devices like printers and scanners.
Remote Information Retrieval: Users can access distant knowledge on various topics via computer networks. The data is kept in distant databases which the user can access via information systems such as the World Wide Web.
Quick Interpersonal Communication: Computer networks have expanded communication speed and volume like never before. Electronic mail (email) is widely used to transfer messages, documents, photos, and videos all over the world. Through social networking sites, online communication has risen by orders of magnitude.
E-commerce: Computer networks have cleared the way for a wide range of business and commercial activities to be conducted online, sometimes known as e-commerce. Users and companies can use the system to pool funds, purchase and sell things, pay bills, manage bank accounts, pay taxes, transfer cash, and manage investments.
Extremely Dependable Systems: Computer networks enable systems to be dispersed in nature, allowing data to be stored in different locations. As a result, the system is extremely dependable. If one of the sources fails, the system will continue to work, and data from the remaining sources will be available.
Inexpensive systems: Computer networks have lowered the cost of installing computer systems in businesses. Previously, corporations were required to establish highly costly mainframes for calculation and storage. With the introduction of networks, setting up networked personal computers (PCs) for the same function is adequate.
VoIP: Voice over Internet Protocol, has completely transformed telecommunications networks. Nowadays, telephone calls are also made using the internet protocol; the traditional system is not in use.
Money Saving:- Computer Network saves money in the various businesses.
- Organizations can employ independent personal computers for each user instead of pricey mainframe computers.
- Organizations can employ the work-group paradigm (peer-to-peer), in which all PCs are networked together, and each has access to the others for communication or sharing.
- If the firm requires security for its operations, it can use the domain model, which includes a server and clients. The server allows all clients to communicate and access data.
- The entire setup is known as the client-server model.
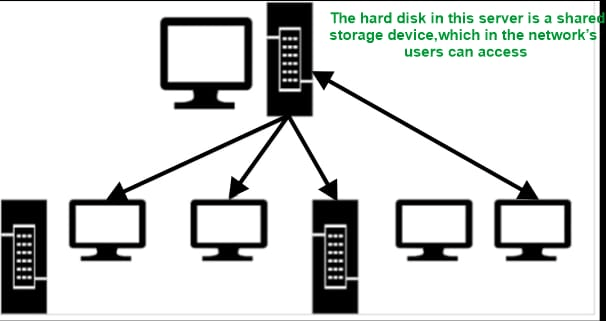
Simultaneous access: A computer network enables a small number of people to develop programs and data at the same time. For example, a company's quarterly sales document requires many managers to examine and amend. We can save the data within the network server, Which is a central computer with a big storage device and other resources available to all users.
When any server stores files for the user to access, that time file server is commonly used. As shown in the image, We may save a unique copy of a data file on the server for each employee. Furthermore, if one user modifies the file, other users will notice a difference when utilizing it.
High Reliability as a Result of Multiple Record Sources:- The fundamental advantage of networks is their dependability, which is why they are becoming increasingly popular among businesses. Critical data may be preserved in several locations utilizing systems. In any case of a computer breaking or if the computer crashes, the data can be saved in another computer by the network. By this method, the data in any network can be protected.
Provide a Mode of Communication: A computer network provides a dynamic communication medium for geographically separated persons. It is simple for two or more people living in different locations to collaborate on the same project by splitting it via a network.
Remote Information Access:
Remote information may be accessed in a variety of ways.
As an example,
- Home shopping, telephone bill payment, e-banking, internet stock trading, and so on.
- It is possible to gain access to an information system such as the World Wide Web, which contains information on the craft, business, cookery, government, health, history, recreation, science, and sports, among other things.
- The newspaper is now available online. You may get the news based on your interests.
Person-to-person communication:
Email:
- The sender creates and sends an email message.
- After sending the mail, the server saves the message in it.
- The server notifies the receiver that a message has arrived.
- When the receiver is ready to view the message, then he/she retrieves it from the server.
Video conferencing and Teleconferencing:
A teleconference is a virtual conference in which participants from many locations hold talks by typing messages. Each communication in the teleconference is visible to every one other.
Clients that have the necessary technology and software may watch and chat with each other face-to-face online rather than simply typing messages. This is referred to as videoconferencing.
Top business applications of computer networks in several fields:-
Software sharing:
In a computer network, application software is often placed on a centralized computer (Server Computer). Instead of purchasing a separate copy of the program for each user, the software may be shared over the network.
Hardware sharing:
Hardware devices in a computer network include printers, access points, HDD, SATA, SSD, drivers, and so on. Many people, for example, can share a single network-connected printer.
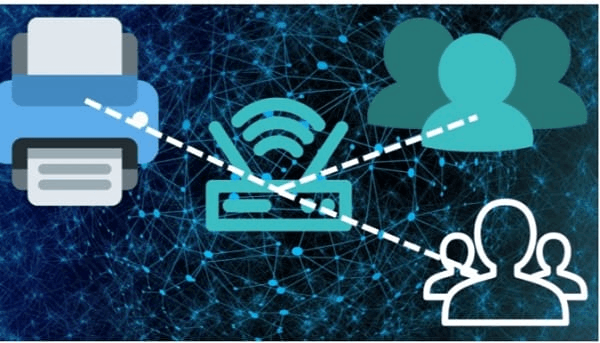
By sharing many devices in a single network, we can save money. With the network, the devices can be organized individually for each user, which is quite expensive for an enterprise.
Internet sharing:
Many users on a computer network can access the internet over a single connection and utilize various services.
Centralized Software Management:
All software are already installed and updated on any computer which has a single server. This saves time while installing/updating individual network computers. These software products are available to network users.
Data Security and Management:
In the computer network, the data is stored in center format. It means that all data is kept on a single server. An administrator improves the management of the company's vital data in a business setting.

By this, the data is very easily available to anyone. A system administrator has complete control and can view or modify crucial data. A system administrator can quickly create a backup of data. Similarly, security measures may be added to data.
Saving disk space:
Computer Network Applications are quite important. All machines on a computer network utilize the same copy of the data files. These are only saved on the server computer's hard drives.
There is no need to save the data files and run any application on a different computer if you are working on the network. This conserves disk space on each PC.
Performance Enhancement:
Using distributed computing, a network may be leveraged to increase the performance of many applications. A calculation task is divided across several machines on the network in distributed computing. This improves the performance of any program.
Entertainment:
People may find a variety of forms of amusement on the computer network. There are many activities that are performed under computer network activities like playing games, watching movies or shows, and listening to music. We can also meet new people on the internet.
Remote access:
A network also makes it possible to access data remotely. By this, the user can access, store or handle their data anywhere in the world.

Network packet:
The majority of current computer networks employ packet-mode communication methods. The network packet is the data unit, which can be transmitted via the packed switched network.
Packets include two sorts of data: control data and user data (payload). The control data provides information that the network needs in order to transfer data to the user, such as source and destination network addresses, error detection codes, and sequencing information. Packet headers and trailers frequently carry control information with payload data.
The bandwidth of the transmission channel can be better among users with network packets than the circuit-switched networks.