What is Point-to-Point Protocol?
PPP is an initialism for Point-to-Point protocol. It is the most widely used protocol for point-to-point communication. If any user wants to operate the internet from home, then the PPP will be in use.
It is a data connection layer protocol that is part of the OSI model's layer 2. It is used to enclose layer three protocols. as well as all of the information accessible in the payload for transmission via serial connections. The PPP protocol may be used on both synchronous and asynchronous links, such as ISDN and dial-up. It is mostly used to communicate between the two devices.
It may be accessed using a number of physical networks, such as serial cables, phone lines, trunk lines, cellular phones, and fibre optic connections, such as SONET. Because the data link layer protocol is utilised to indicate where the transmission begins and stops, ISPs (Internet Service Providers) employ the PPP protocol to provide dial-up internet access.
Service provided by PPP protocol:-
- It specifies the frame format in which transmission takes place.
- It specifies the procedure for establishing links. If a user connects to a server, the PPP protocol handles the link connection part.
- It outlines the data exchange procedure, i.e., how data will be shared and at what pace.
- The PPP protocol's main feature is encapsulation. The important and useful function of the PPP protocol is encapsulation. It shows the encapsulation of the network layer and data link layer in a single frame.
- It specifies the authentication procedure for the two devices. The PPP protocol governs the authentication, handshaking, and password transmission between the two devices.
Service not provided by PPP protocol:-
- It is not compatible with the flow control method.
- It offers a straightforward error control method.
- Since PPP only supports point-to-point communication, it lacks an addressing method for handling frames in a multipoint setup.
PPP has two major applications, which are listed below:
- It is commonly utilised in high-speed broadband communications with huge loads. For example, the internet runs under high demand and speed.
- It is used to send multiprotocol data between two computers that are linked from point to point. It is mostly utilised in point-to-point devices, such as routers, where the PPP protocol is frequently employed since it is a WAN protocol rather than a standard LAN ethernet protocol.
The frame format of PPP protocol:-
The PPP protocol frame format includes the following fields:
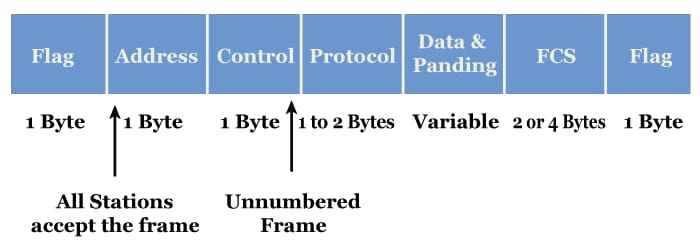
- Flag:- The flag field indicates the start and end of a frame. Each frame's flag field is a single byte that appears at the beginning and end of the frame. The flag pattern is equivalent to the HDLC bit pattern, which is 01111110.
- Address:- It is a 1-byte constant field with the value 11111111. These are the eight broadcast messages.
- Control:- It is a 1-byte field with the value 11000000 set as a constant. Because PPP lacks flow control and has a very restricted error control mechanism, this field is unnecessary. The control field is a mandatory component of protocols that provide flow and error control techniques.
- Protocol:- It is a one or two-byte field that specifies what will be conveyed in the data field. The data might be useful information or other information.
- Payload:- The payload field contains either user data or other data. The payload field can be up to 1500 bytes long.
- Checksum:- The function of a checksum is to detect errors. It has 16-bit files.
Transition phases of PPP protocol:-
A PPP protocol's transition stages are as follows:
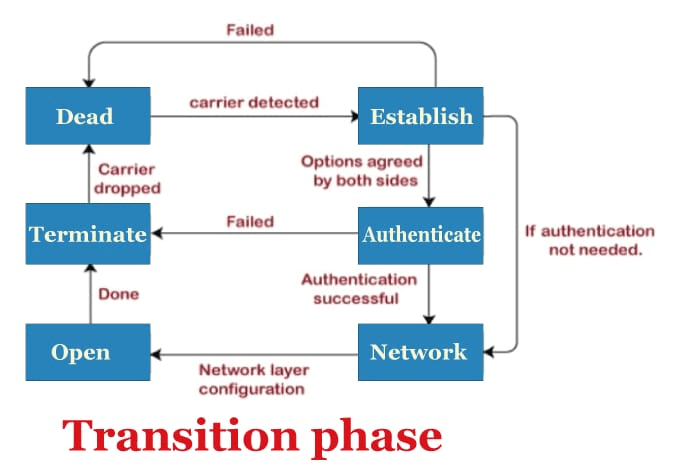
- Dead:- Dead is the special phase in which activation of any carrier user in the physical layer can be detected.
- Establish:- If any node starts functioning, then the phase is shifted into an established phase. In summary, when a node initiates communication or detects a carrier, it passes from the dead to the established phase.
- Authenticate:- It is an optional step that signals that the connection can also go to the authenticate phase. The phase of the communication changes from establish to authenticate only when both communicating nodes agree.
- Network:- The network is established, or the phase is network when the authentication is successful. Network layer protocol negotiations take occur during this stage.
- Open:- The network establishment phase is followed by the open phase. The open phase here denotes that data exchange is happening. Perhaps we could say that it enters the open phase following network layer configuration.
- Terminate:- The connection is disconnected, and the process continues to the terminal phase once all the work has been completed. As the link reaches the terminate phase, it transitions to the dead phase, which denotes that the previously established carrier has been dropped.
During the period of transition, there are two more possibilities that could exist:
- The authentication fails when the connection transitions exist from the authenticate phase to the terminate phase.
- The carrier fails when the link exist from the established to the dead state.
PPP stack:-
There are three sets of protocols in the PPP stack:
1. The Link Control Protocol (LCP):-
Establishing, maintaining, configuring, and terminating links are the responsibilities of LCP. Additionally, it offers a bargaining method.
2. Authentication Protocol:-
PAP (Password Authenticate Protocols) and CHAP are the two different kinds of authentication protocols (Challenged Handshake Authentication Protocols).
a) PAP (Password Authentication Protocol):-
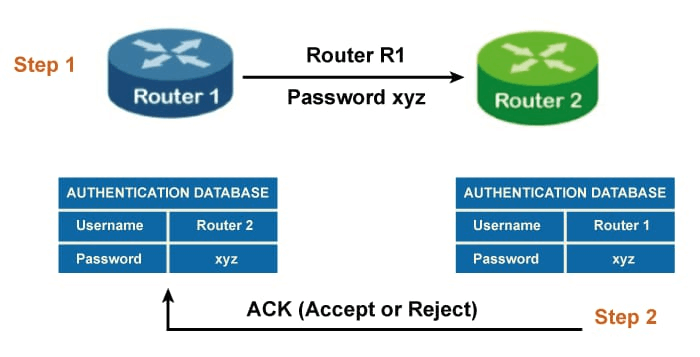
Compared to CHAP, PAP is less secure because the password is sent in clear text while using the PAP protocol. The procedure entails two steps. Let's assume there are two routers. Router 1 and router two, and router 1 send all the information of the username and password for authentication as the initial stage in the authentication process. The second step involves routers 2 and 1 authenticating each other. If the username and password match, the authentication succeeds; otherwise, it fails.
b) CHAP (Challenge Handshake Authentication Protocol):-
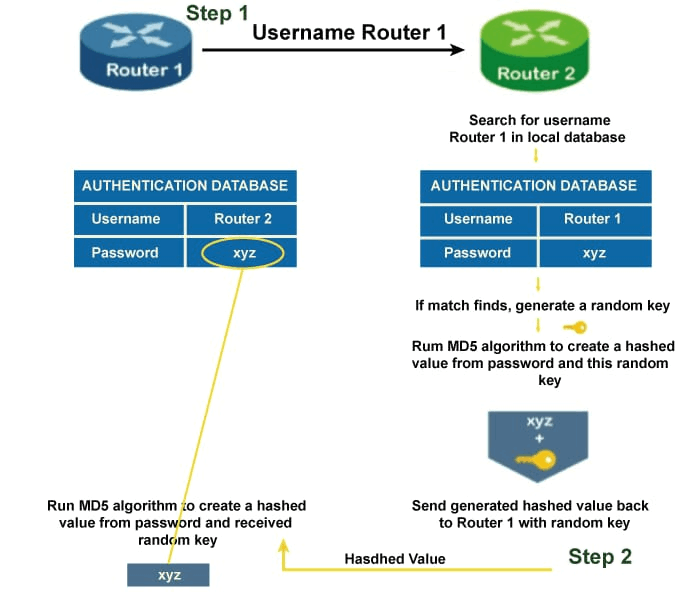
CHAP consists of three steps. Let's understand the following these three steps:
- Step 1:- Assume there are two routers, namely router 1 and router 2. Router 1 transmits the username to router 2, but not the password.
- Step 2:- Router 2 has a database containing a list of permitted hosts and their login information. If no data is discovered, router one is deemed to be an invalid host for connection and the connection is cut off. The random key is passed if a match is made.
The MD5 hashing algorithm accepts the random key and the password, and they are used to produce the hashed value from the password and the random key. The "Challenge" is another name for the hash value. Router 1 will receive the challenge and the random key.
- Step 3:- Router 2 sends hashed value with the random key to router 1. Router 1 will then send the locally saved password and random key to the MD5 hashing function.
The random key and password are combined to create the hashed value using the MD5 hashing method. The connection will cut off if both hash values generated and received are different. The connection is allowed if it matches. The authentication signal—which may be approved or rejected—is transmitted to router 2 based on the aforementioned authentication outcome.
3. The Network Control Protocol (NCP):-
The above step is to connect to the network layer when the link has been formed and authenticated. As a result, PPP utilises a distinct protocol known as network control protocol (NCP). The NCP protocol allows data moving from the network layer to PPP frames which are to be encapsulated.