What is a Proxy Server?
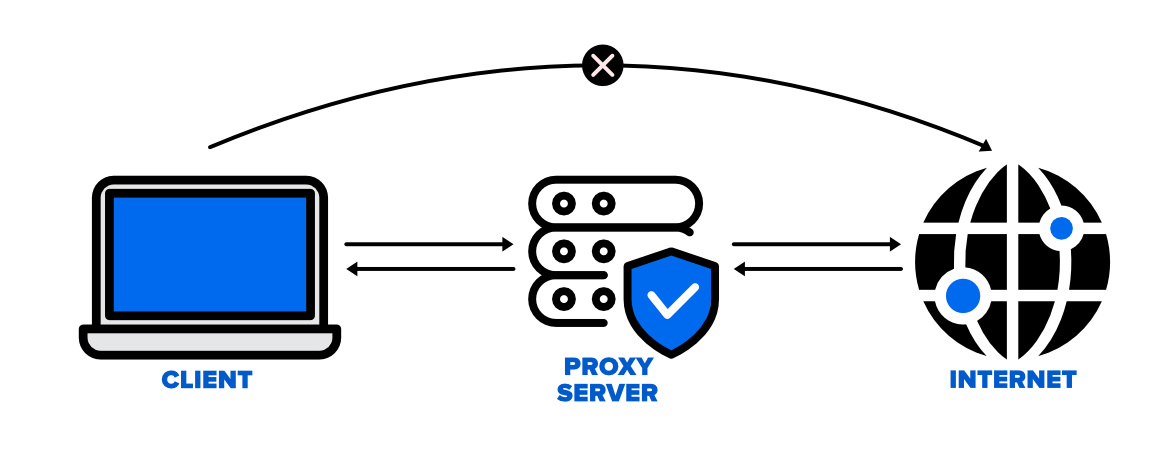
When a client and a server need to communicate, a proxy server is a computer system or piece of software that mediates the communication. Instead of going straight to the server, when a user requests a resource from a server, the proxy server receives the request. After reviewing the request, the proxy server sends it to the server on the client’s behalf. The proxy server delivers the response from the server to the client once the server responds to the request.
There are several reasons why someone might use a proxy server. One common reason is to improve privacy and security. By using a proxy server, a user can hide their IP address and other identifying information from the server they are accessing. This can make it more difficult for someone to track their online activity or for their personal information to be compromised.
There are several types of proxy servers, including web proxies, reverse proxies, and open proxies. Web proxies are used to access web pages and other online resources, while reverse proxies are used to improve performance and security for web servers. Open proxies, on the other hand, are public proxy servers that anyone can use to access the internet.
Need for Proxy Server
- Security: Proxy servers provide an additional layer of security by acting as a buffer between clients and the internet. Proxy servers can block potentially harmful traffic, such as malware, viruses, and spam. They can also provide anonymous browsing and prevent websites from collecting personal data, which enhances privacy and security for users.
- Improved Performance: Proxy servers can improve performance by caching content, reducing the amount of data that needs to be transferred between clients and servers. Caching means that frequently accessed data is stored on the proxy server, which can be accessed by clients more quickly, reducing load times and reducing network traffic.
- Access Control: Proxy servers can provide access control and authentication for users, preventing unauthorized access to sensitive information. Proxy servers can also enforce usage policies, such as blocking access to certain websites, or limiting bandwidth for certain types of traffic.
- Monitoring and Logging: Proxy servers can be configured to log network traffic, providing administrators with detailed information about how the network is being used. This can help in identifying potential security threats, or identifying areas where network resources may be overused.
- Geo-restriction bypass: Proxy servers can be used to bypass geo-restrictions, allowing users to access websites that may be blocked or unavailable in their location. By connecting to a proxy server in a different location, users can access content that may otherwise be unavailable to them.
Working of Proxy Server
A proxy server operates by intercepting communication between clients and servers, and acting as an intermediary for requests and responses. The general steps involved in the operation of a proxy server are as follows:
- Client sends a request to access a resource on the internet, such as a website or a file download.
- The proxy server intercepts the request, and after evaluating it, decides whether to allow it or not.
- The proxy server transmits the request on behalf of the client to the target server if it is approved
- The response is sent back to the proxy server by the target server after processing the request.
- The response is then assessed by the proxy server to decide whether or not it should be approved.
- The proxy server sends the reply back to the client if the response is accepted.
Proxy Servers can be configured to perform various tasks such as caching, filtering, and blocking traffic. Proxy servers can boost performance and cut network traffic by storing frequently accessed material. By filtering traffic, proxy servers can prevent access to malicious or inappropriate content, and enforce usage policies. Proxy servers are able to restrict access to select websites or services by blocking traffic.
Types of proxy servers
There are several types of proxy servers, each with its specific use case. Here are some of the most common types of proxy servers:
- Forward Proxy: Clients can access internet resources through a forward proxy, which is a proxy server. A client requests a resource, and the forward proxy passes the request to the target server on the client’s behalf. Returned to the proxy server, which subsequently passes it on to the client, is the response from the target server.
- Reverse Proxy: A reverse proxy is a type of proxy server that servers utilise to deal with client requests. When a client requests a resource, the request is forwarded to the reverse proxy, which on the server's behalf passes it to the target server. The response from the target server is sent back to the reverse proxy, which then forwards it to the client.
- Open Proxy: A proxy server that is open to the public is known as an open proxy. Open proxies can be used by anyone to browse the internet anonymously, bypass content filters or for malicious purposes.
- Closed Proxy: An authentication process is necessary to access a closed proxy server. Closed proxies are typically used by organizations to control access to the internet and enforce usage policies.
- Transparent Proxy: A proxy server that doesn't alter the request or response headers is known as a transparent proxy. It is called "transparent" because it is not visible to the client or the target server. These type of proxy servers are mainly used for content filtering and caching
- Anonymous Proxy: An anonymous proxy is a proxy server that hides the IP address of the client. This can be useful for users who want to browse the internet anonymously, but it can also be used for malicious purposes.
- High Anonymity Proxy: A high anonymity proxy server is one that conceals the client's IP address in addition to keeping its own identity a secret. The most secure kind of proxy server is one with a high level of anonymity.
This is all about proxy servers. Hope you understood this topic.