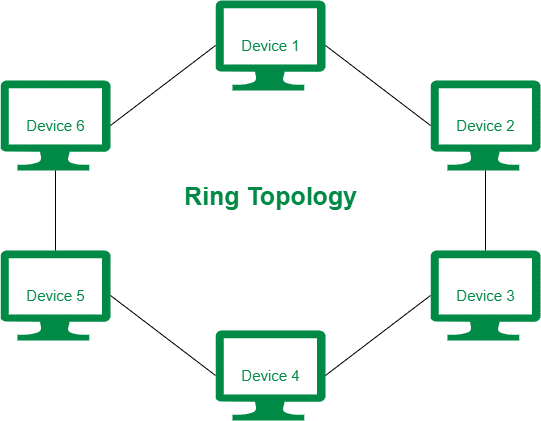
Ring Topology in Computer Network
Ring topology is a topology that was invented by IBM in 1984 by the Institute of Electrical and Electronics Engineers. It is defined as a type of network topology where every device is connected with two other types of devices, where it forms a circular shape. Here data is transferred in a circular way or we can say that data is transferred in a single direction only. The transfer of data from one device to another takes place until it reaches its final destination or point and the data which is being transmitted is known as a token. Also, the structure of this topology is similar to a ring shape because of its connections.
Ring topology is also known as active topology as all the nodes are active during the transmissions. The tokens in this topology are jumped if the number of nodes is large. Also, ring topologies are designed using cables that are twisted or of fiber optics. And these cables are chosen according to the distance and the speed required. This topology consists of repeaters that help in minimizing data loss and help or improve the network strength.
In the past years, ring topology was one of those networks which were used in a wide range of offices, institutes, etc.
Types of Ring Topology
There are two types of ring topology and they are:
1. Bidirectional:
In a bidirectional ring topology, the flow of the data in a network is both in clockwise and anti-clockwise directions.Bidirectional topology has a key property and that is 'dynamic clustering'. Clusters in this topology are not rings, logically it forms a chain-like structure where data can move in both directions. This ring functions smoothly with an increase in the locality.
2. Unidirectional:
Whereas in unidirectional ring topology, the flow of data in the network is in one direction only. This topology provides only one way for the nodes to reach their destination. It is also known as a half-duplex network. Here, devices are connected in such a way that they can communicate directly with the other device. This topology flows in one direction only and one cannot change it.
Features of Ring topology
- This topology consists of repeaters.
- Data is transmitted in a single direction only.
- It is reliable.
- In this topology, if one computer stops functioning then the entire network will break down.
- Cables play an important role in this network.
- They transfer data at a great speed.
- The flow of data is systematic.
- They are mostly used in small network areas.
Advantages/ Disadvantages of Ring Topology
The advantages are:
- For connectivity, it does not require a network server.
- It has a higher rate of information.
- Modifications are done easily.
- New devices can be added without creating any disruption.
- When compared to the bus topology, ring topology has better performance because of the presence of tokens.
The disadvantages are:
- It is expensive.
- Difficulties arise during the process of troubleshooting.
- It is not scalable.
- Tokens should be passed so that the flow will be continuous.
- If one node fails, then the whole process is disrupted.
- It is not used for large networks.
Why Ring Topology?
Ring topology is not used in huge numbers, but this topology helps in solving issues that are not being done by bus or star topology, such as it helps during collisions and many more. Ring topology follows a network protocol and shows or describes how the entire network process works. Ring networks are set up when there is a requirement for a simple network. This topology is best suitable for places where there is less requirement for high-speed data.
Conclusion
Ring topology is a network where data flows in a circular direction. This topology is rarely found to be used in this contemporary world. Ring topology is known to be a logical topology because of its connections. Overall, in simple terms, this topology is used only for the connections of LAN or WAN and this network is in the shape of a ring therefore, it’s given the name ring topology, also that it is every node follows a loop. Ring topology is being used as a wireless sensor network as its power consumption is low and of cluster routing. The most important reason for using this topology as a wireless sensor is that, suppose when a case arises where sensor communication gets disconnected due to the failure of one node then one side is failed but the other side or the opposite direction can be sent the data again by using this site as data can be transferred bidirectionally too.