What is VRRP Protocol?
This article will help you in providing a basic understanding of VRRP in the computer network.
Virtual Router Redundancy Protocol (VRRP) is a network protocol that allows multiple routers to work together as a virtual router, providing redundancy for the default gateway IP address on a LAN (Local Area Network). VRRP provides a way for network administrators to improve network reliability by creating a highly available default gateway that is virtually represented by a single IP address.
In a network without VRRP, there is only one router acting as the default gateway, which means that if that router fails, the entire network loses its connection to the outside world. With VRRP, multiple routers can act as the default gateway, and if one router fails, another router automatically takes over the job of forwarding packets, ensuring that network connectivity is maintained.
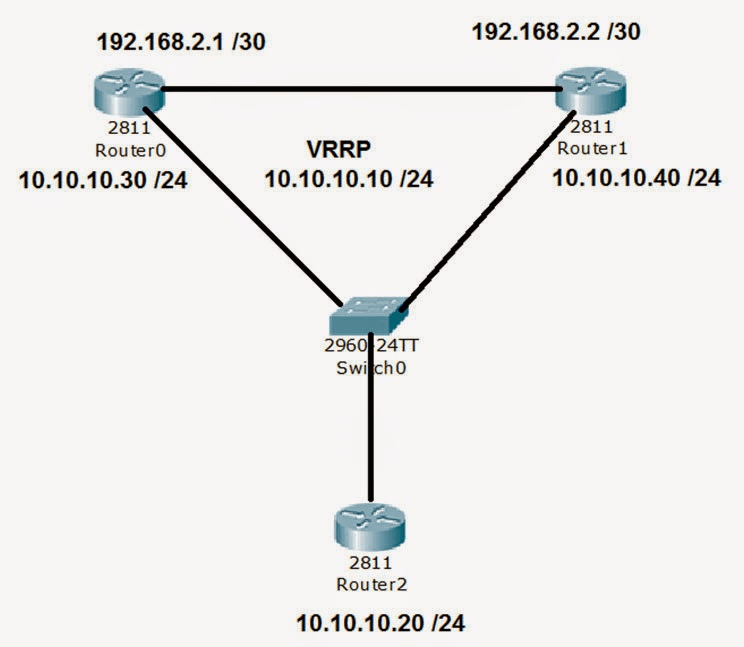
VRRP works by creating a virtual router that is represented by a virtual IP address. This virtual router is shared among multiple physical routers, which participate in the VRRP group.
The VRRP group elects one router as the master, who is in charge for forwarding packets which are to be submitted to the virtual IP address. Other routers in the group act as backups, monitoring the master router's availability and taking over if it fails. All packets transmitted to the virtual IP address are forwarded by one of the backup routers if the master router fails. This happens if the backup router is chosen to replace the master router.
According to a priority system, the router with the highest priority is chosen to serve as the master router. Administrators can adjust the priority of each router in the group to control which router becomes the master.
VRRP is widely used in enterprise networks to provide redundancy for critical network resources, such as servers and gateways.
Important Aspects in VRRP
Here are some important terms used in VRRP:
- Virtual Router: The virtual router is a logical entity that is represented by a virtual IP address. Many physical routers in the VRRP group share the virtual router. One of the routers in the group is designated as the master in order to forward packets sent to the virtual IP address.
- Master Router: The master router is the router in the VRRP group that is responsible for forwarding packets sent to the virtual IP address. The router with the highest priority wins the election to become the master router, which is based on a priority system.
- Backup Router: The backup routers in the VRRP group are responsible for monitoring the master router and taking over its role if it fails. The backup routers continuously communicate with the master router to determine whether it is still functioning properly.
- Priority: The priority is the value assigned to each router in the VRRP group that determines which router becomes the master if the current master fails. Administrators can change the priority of each router to determine which router becomes the master by selecting the router with the highest priority.
- Advertisement Interval: The advertisement interval is the time interval between VRRP packets sent by the routers in the VRRP group. The advertisement interval is used to determine the availability of the master router.
- Preemption: Preemption refers to a router's capacity to replace a router with a lower priority as the master router, even if the lower priority router is operating normally.
- Hello Message: The hello message is a message sent by the routers in the VRRP group to announce their presence and to determine the availability of the other routers in the group. The hello message is used to elect the master router.
- Dead Interval: The dead interval is the time interval after which a router is considered to have failed if it does not send VRRP packets. The backup router with the greatest priority takes over as the master router in the event that the primary router fails.
Steps to configure VRRP
Here are the basic steps to configure VRRP:
- Enable VRRP on the interfaces of each router in the VRRP group by entering the "vrrp" command in the interface configuration mode.
- In the interface configuration mode, issue the command "vrrp [group number] ip [virtual IP address]" to give the VRRP group a virtual IP address..
- Set the priority for each router in the VRRP group by entering the "vrrp [group number] priority [priority]" command in the interface configuration mode. The router with the top priority will take over as the master router.
- Set the advertisement interval for the VRRP group by entering the "vrrp [group number] timers advertise [advertisement interval]" command in the global configuration mode.
- Configure preemption for the VRRP group by entering the "vrrp [group number] preempt" command in the interface configuration mode. This allows a higher-priority router to take over the role of the master router if necessary.
- Verify the VRRP configuration by entering the "show vrrp [group number]" command in the privileged EXEC mode. This will show the VRRP group's status and configuration.
This is all about VRRP in computer network. Hope you understood this topic.