Network Attack in Computer Networks
This article will provide you good understanding on basic network attacks in computer network. Before moving onto type of network attacks. Let us understand what are actually network attacks are.
What is a Network Attack?
Network attacks are malicious actions or attempts to exploit vulnerabilities or weaknesses in a computer network or its components, such as servers, routers, switches, and other network devices, with the intention of stealing, altering, or destroying data, disrupting network operations, or gaining unauthorized access to sensitive information or resources.
Network attacks can also be categorized according to their methodology. Some attacks make use of well-known flaws in network hardware or software, while others con users into disclosing sensitive data through social engineering techniques.
Here are a few instances of network attacks:
- Denial of Service (DoS) attacks
- Distributed Denial of Service (DDoS) attacks
- Phishing attacks
- Sniffing attacks
- Malware attacks
- IP Spoofing
- SQL injection
- Man-in-the-Middle Attack
1. Denial of Service (DoS) Attacks
Denial of Service (DoS) is a type of cyberattack in which an attacker attempts to disrupt the normal functioning of a targeted system or network by overwhelming it with a flood of traffic, requests, or other data. The goal of a DoS attack is to prevent legitimate users from accessing the system or network by making it unavailable or slow to respond.
A DoS attack can take many forms, but some common techniques include flooding the target with traffic from multiple sources (distributed denial of service, or DDoS), exploiting vulnerabilities in the system to crash it or overload its resources, or simply sending large amounts of data to the target in order to consume its bandwidth.
2. Distributed Denial of Service (DDoS) attacks
Distributed Denial of Service (DDoS) is a type of cyberattack in which multiple compromised systems (often called "botnets") are used to flood a targeted system or network with traffic, requests, or other data, making it unavailable or unresponsive to legitimate users.
In a DDoS attack, the attacker typically gains control of a large number of computers or devices by infecting them with malware or by exploiting vulnerabilities. These compromised systems are then used to flood the target with traffic, overwhelming its resources and preventing legitimate users from accessing it.
DDoS attacks are more powerful than traditional DoS attacks because they involve multiple sources of traffic, making it more difficult to block or filter out the malicious traffic. DDoS attacks can also be more difficult to trace back to the attacker, since the traffic comes from multiple sources.
3. Phishing attacks
An example of a social engineering assault is phishing, which tries to persuade people to divulge sensitive data like login passwords or financial information. A phishing attacker's goal is to steal sensitive data, obtain unauthorised access to a stoner's accounts, or influence them.
4. Sniffing attacks
A sniffing attack is a kind of network attack that targets networks with price-sensitive data and intercepts and tests them.
A sniffer is a device or piece of software used to record and analyse network packets, often known as a packet sniffer or network analyzer. In order to collect and analyse network activity in order to steal sensitive data, such as login credentials, financial information, or other sensitive data, hackers employ sniffing tools.
5. Malware attacks
Malware is a type of software that is designed to harm, exploit, or steal information from a computer system or network.
Malware is a broad term that encompasses many different types of malicious software, including viruses, worms, trojans, ransomware, spyware, adware, and more. Malware typically aims to do one of the following things, despite its diverse nature and capabilities:
- Give an attacker remote access to a compromised machine.
- Use the compromised device to send spam to unaware recipients.
- Look into the impacted user's local network.
- stealing confidential information.
6. IP spoofing
IP spoofing, one method by which one user might impersonate another, is the ability to inject packets into the Internet with a bogus originating address. End-point authentication, or a system that will enable us to know for sure if a message originates from the location, we believe it does, will be necessary to address this issue.
7. SQL injection
An attack known as SQL injection takes advantage of holes in websites or web-based applications' SQL code. It is a technique for taking advantage of holes in online applications that let an attacker insert harmful SQL statements into a web application's input fields, which the back-end database then executes.
An attacker can use SQL injection to access databases without authorization, steal confidential data, edit or remove data, or even run arbitrary server instructions.
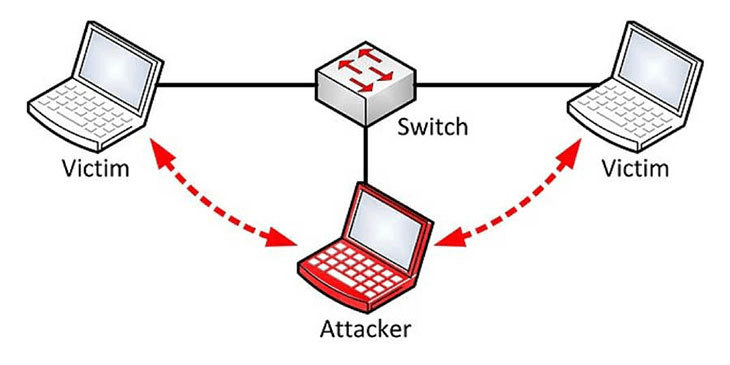
8. Man-in-the-Middle Attack
A man-in-the-middle assault, as its name suggests, happens when someone is actively observing, recording, and transparently managing your communication while it is being exchanged between you and the other party. Computers may not be able to distinguish amongst one another when they are sharing data at low levels of the network layer.
This is all about basic network attacks in a computer network. Hope you understood this topic.