Benefits of SOCKS5 Proxy in Computer Networks
This article will help you in providing a good understanding of the SOCKS5 proxy.
What is SOCKS5 Proxy?
A SOCKS5 (Socket Secure 5) proxy is a type of proxy server that allows internet users to route their web traffic through a remote server, thereby hiding their actual IP address and geographic location. Unlike other types of proxies, such as HTTP or HTTPS, SOCKS5 is a more versatile and secure protocol that supports various types of internet traffic, including web browsing, email, file transfer, and online gaming.
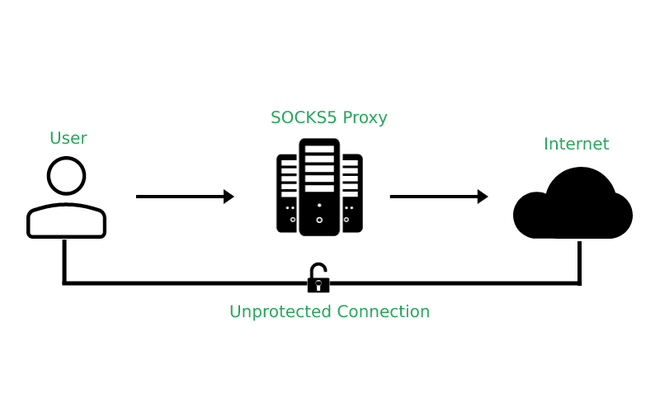
A SOCKS5 proxy server works by establishing a connection between the user's device and the remote server, creating a virtual tunnel through which all internet traffic passes. The proxy server receives the user's requests and sends them to the internet on their behalf, thereby hiding the user's actual IP address and geographic location. This allows users to access geo-restricted content, bypass internet censorship, and protect their online privacy and security.
SOCKS5 is also designed to be more efficient than its predecessors, with features such as connection reuse and connection pooling. This helps to reduce the amount of network overhead and improve performance.
Features of SOCKS5 proxy
- Authentication: SOCKS5 supports several authentication methods, including username and password authentication, as well as authentication using public and private keys. This helps to ensure that only authorized users are granted access to the proxy server.
- Support for TCP and UDP traffic: SOCKS5 can handle both TCP and UDP traffic, making it more versatile than its predecessors, which only supported TCP traffic.
- Improved efficiency: SOCKS5 includes features such as connection reuse and connection pooling, which help to reduce the amount of network overhead and improve performance.
- Remote DNS resolution: SOCKS5 allows for remote DNS resolution, which means that DNS queries can be sent through the proxy server, rather than directly from the client. This helps to improve privacy and security.
- Firewall-friendly: SOCKS5 is firewall-friendly, as it can use the same port for incoming and outgoing traffic, making it easier to configure in restrictive network environments.
- Support for IPv6: SOCKS5 supports both IPv4 and IPv6 addresses, making it compatible with modern network infrastructure.
- Proxy chaining: SOCKS5 can be used in combination with other proxy protocols, such as HTTP or HTTPS proxies, to create a chain of proxies that offer, greater anonymity and security.
- Encryption: While SOCKS5 does not provide encryption on its own, it can be used in conjunction with other protocols, such as VPNs, to add an extra layer of security.
Overall, SOCKS5 is a versatile and secure proxy protocol that offers a range of features designed to improve network performance, security, and privacy. However, it is important to note that the effectiveness of a SOCKS5 proxy will depend on the specific use case and the steps taken to ensure privacy and security.
Benefits of SOCKS5 Proxy
The benefits of using a SOCKS5 (Socket Secure version 5) proxy include:
- Improved security: SOCKS5 provides an extra layer of security by acting as an intermediary between the client and the server, preventing direct communication between the two. This can help to protect against attacks such as IP spoofing, port scanning, and other network-based attacks.
- Anonymity: SOCKS5 allows users to connect to the internet through a different IP address than their own, making it more difficult for third parties to track their online activities. This can be useful for accessing geo-restricted content or for maintaining online privacy.
- Bypassing internet restrictions: SOCKS5 can be used to bypass internet restrictions or firewall rules, as it allows users to connect to the internet through a different IP address than their own. This can be useful for accessing websites or online services that may be blocked in certain regions or by certain network administrators.
- Versatility: SOCKS5 can handle both TCP and UDP traffic, making it more versatile than earlier versions of the protocol, which only supported TCP traffic. This makes it a popular choice for a variety of network applications and protocols.
- Efficiency: SOCKS5 includes features such as connection reuse and connection pooling, which help to reduce network overhead and improve performance. This can be particularly beneficial for high-traffic networks or for users with limited bandwidth.
- Firewall-friendly: SOCKS5 is firewall-friendly, as it can use the same port for incoming and outgoing traffic. This makes it easier to configure in restrictive network environments.
- Remote DNS resolution: SOCKS5 allows for remote DNS resolution, which means that DNS queries can be sent through the proxy server, rather than directly from the client. This helps to improve privacy and security.
Few limitations of the SOCKS proxy
With the benefits of SOCK5 proxy, there are also some limitations which are described below:
- Bottom of Form
- Slow speeds: In some cases, using a SOCKS5 proxy can result in slower network speeds, particularly if the proxy server is located far away from the user's location or if the server is handling a high volume of traffic.
- Lack of encryption: SOCKS5 proxy does not provide encryption on its own. While it can be used in combination with other protocols, such as VPNs, to add an extra layer of security, it is important to ensure that appropriate measures are taken to protect sensitive data.
- Security risks: While SOCKS5 can provide an extra layer of security by acting as an intermediary between the client and the server, it is important to be aware of potential security risks. For example, if the proxy server is compromised, an attacker may be able to intercept and view sensitive data transmitted through the server.
This is all about the SOCKS5 proxy and its benefits. Hope you understood this topic.