What is ICMP Protocol?
This article will provide you a detailed explanation of a computer network concept called ICMP.
ICMP, or Internet Control Message Protocol, is a protocol that is used to send error messages and operational information about the status of network devices on the Internet. It is a fundamental component of the Internet Protocol (IP) suite and is used by network devices, such as routers and switches, to communicate with each other.
ICMP is used to send error messages, such as when a network device is unreachable, a packet is too large to be transmitted, or a route is not available. These error messages are important for network administrators to diagnose and troubleshoot network issues, and they help to ensure that network traffic is properly routed to its destination.
In addition to error messages, ICMP can also be used to transmit operational information about the status of network devices, such as the round-trip time of packets sent between devices. This information can be used to monitor the health of the network and to detect any potential issues that may need to be addressed.
ICMP is an essential component of the Internet Protocol (IP) suite, and it is used by virtually all network devices that are connected to the Internet. It is a simple and efficient protocol that is designed to work with a wide range of network technologies and can be used to communicate between devices that are using different network protocols.
While ICMP is primarily used for error reporting and operational information, it can also be used for more advanced network functions, such as network discovery and security scanning. However, these uses are less common and may require additional tools or software to implement.
What is ICMP used for?
ICMP, or Internet Control Message Protocol, is primarily used for error reporting and operational information in IP networks. It is a protocol that runs on top of the IP layer and is used by network devices to communicate status and error messages to each other. Here are some of the most common uses of ICMP:
- Error reporting: ICMP is used to report errors in network communication, such as when a packet cannot be delivered to its destination, a device is unreachable, or a route is not available. These error messages are important for network administrators to diagnose and troubleshoot network issues.
- Ping and traceroute: ICMP can be used to test connectivity and measure the round-trip time between network devices. The "ping" command sends an ICMP echo request to a device, which then responds with an echo reply. Traceroute uses ICMP to determine the route that packets take to reach their destination.
- Path MTU discovery: ICMP can be used to discover the maximum transmission unit (MTU) of a path between two network devices. This is useful for ensuring that packets are not fragmented along the path, which can degrade network performance.
- Redirects: ICMP can be used to redirect traffic to a more efficient route or gateway. When a router determines that a better path exists, it can send an ICMP redirect message to the sender, indicating the new route.
- Security and network scanning: ICMP can be used for various security and network scanning purposes, such as identifying hosts that are online or determining the operating system running on a device. However, these uses are less common and may require additional tools or software to implement.
Overall, ICMP plays a crucial role in IP networking by providing a means of communicating status and error messages between network devices.
Types of ICMP messages
ICMP, or Internet Control Message Protocol, includes a variety of different message types that are used for different purposes. Here are some of the most common types of ICMP messages:
- Echo request and Echo reply: These messages are used by the "ping" command to test network connectivity and measure the round-trip time of packets sent between devices. The echo request message is sent by the sender, and the echo reply message is sent by the recipient.
- Destination Unreachable: This message is sent by a network device to indicate that a packet cannot be delivered to its destination. The message includes information about the reason for the failure, such as an unknown host or an unreachable network.
- Redirect: This message is sent by a router to redirect traffic to a more efficient route or gateway. When a router determines that a better path exists, it can send an ICMP redirect message to the sender, indicating the new route.
- Time Exceeded: This message is sent by a network device to indicate that a packet has exceeded its time-to-live (TTL) value and has been discarded. The message includes information about the reason for the time-out, such as a network loop or a misconfigured router.
- Parameter Problem: This message is sent by a network device to indicate that a packet contains an error in one of its header fields. The message includes information about the specific field that contains the error.
- Router Advertisement and Router Solicitation: These messages are used by network devices to advertise the presence of routers on the network and solicit information about available routers.
- Address Mask Request and Address Mask Reply: These messages are used to determine the subnet mask of a network device. The request is sent by the sender, and the reply is sent by the recipient.
Overall, ICMP messages play a crucial role in IP networking by providing a means of communicating status and error messages between network devices. By using different types of ICMP messages, network devices can communicate with each other and diagnose and troubleshoot network issues.
Working of ICMP
ICMP (Internet Control Message Protocol) is a protocol used by network devices, such as routers and hosts, to send error messages and operational information about network conditions. ICMP messages are sent as IP (Internet Protocol) packets, and they are used to help diagnose network problems and to control the flow of network traffic.
When a device encounters an error, such as a packet being dropped due to network congestion or a destination being unreachable, it may send an ICMP message to the source of the packet to notify it of the error. For example, if a router receives a packet destined for a network that it cannot reach, it will send a Destination Unreachable ICMP message to the sender of the packet. This allows the sender to take appropriate action, such as choosing a different route or sending the packet to a different destination.
Another common use of ICMP is for network diagnostic purposes, such as the ping command. Ping sends an ICMP Echo Request message to a remote host, and if the host is reachable, it responds with an ICMP Echo Reply message. This allows a user to determine whether a remote host is up and running and to measure the round-trip time of packets sent to the host.
ICMP messages also play a role in network congestion control. For example, if a router detects that its buffer is becoming full, it may send an ICMP Source Quench message to the sender of the packets to indicate that it should slow down the rate at which it is sending packets. This helps prevent network congestion and ensures that packets are delivered more reliably.
In summary, ICMP is a crucial protocol that is used for network diagnostics, error reporting, and congestion control. It plays an important role in ensuring that network traffic flows smoothly and that errors are detected and resolved quickly.
ICMP packet format
ICMP (Internet Control Message Protocol) is a protocol used for sending error messages and operational information about network conditions. The ICMP packet format consists of:
- Type (8 bits) - specifies the type of ICMP message, such as echo request or echo reply.
- Code (8 bits) - provides further information about the ICMP message type. For example, the code for a destination unreachable message indicates the reason for the unreachable status, such as a network or host unreachable.
- Checksum (16 bits) - a checksum calculated over the entire ICMP packet, used for error checking.
- Identifier (16 bits) - an identifier that can be used to match ICMP requests with replies.
- Sequence number (16 bits) - a sequence number that can be used to identify individual ICMP requests and replies.
- Data - optional data that can be included in the ICMP message, such as a timestamp or error message.
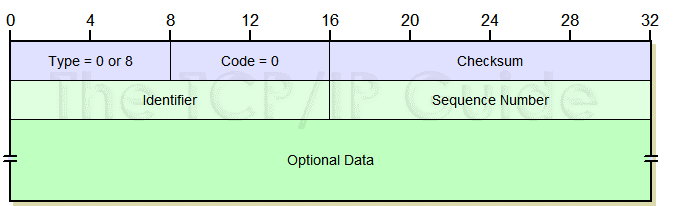
The total length of an ICMP packet varies depending on the type of message and the amount of optional data included.
ICMP security concerns
ICMP (Internet Control Message Protocol) has several security concerns that network administrators should be aware of:
- ICMP Redirect attacks: An attacker can exploit ICMP Redirect messages to redirect traffic to a malicious destination. For example, an attacker can send a spoofed ICMP Redirect message to a router, causing the router to redirect traffic to the attacker's machine. This can be mitigated by filtering ICMP Redirect messages at the network perimeter.
- ICMP Flood attacks: As mentioned earlier, ICMP Flood attacks can be used to conduct DDoS attacks. These attacks can consume network bandwidth and overwhelm network resources, causing a denial of service.
- ICMP Echo Reply attacks: An attacker can use ICMP Echo Reply packets to conduct reconnaissance on a network. By sending ICMP Echo Request packets to a range of IP addresses, the attacker can determine which IP addresses are active and responding. This information can be used to identify potential targets for further attacks.
- ICMP Timestamp and Address Mask Request attacks: ICMP Timestamp and Address Mask Request packets can be used to obtain information about a target network's configuration. For example, an attacker can use an ICMP Timestamp Request packet to determine the current time on a target system, which can be useful for planning attacks.
To mitigate these security concerns, network administrators can implement measures such as filtering ICMP traffic at the network perimeter, rate limiting ICMP traffic, and using intrusion detection and prevention systems to detect and block malicious ICMP traffic. Additionally, implementing security best practices such as network segmentation and access control can help to limit the impact of ICMP-based attacks.