Controlled Access Protocols in Computer Networks
In this tutorial, we will discuss Controlled Access Protocols in Computer Networks.
Introduction
On a shared platform, it is a strategy to minimise data frame collision. As in controlled access technique, every station engages in communication and chooses whether to provide a data frame that has been accepted by every other station. This implies that until all other stations are rejected, a single station cannot provide the data frames. For more understanding, controlled access protocols in computer networks can be explained with the above points as follows:
- All stations in the controlled access approach must communicate with one another to determine which station has the authority to deliver the data.
- The primary goal of restricted access protocols is to prevent collisions on shared media by allowing only one node to transfer data at a time.
- No station may send data until the other stations have made their decision.
- To prevent the message collisions on a shared medium, it only permits one node to send at a time.
We understand that stations check among themselves with others while sending the information called "communication." And this process will lead to selecting only one station to send the information correctly. This technique implies that no collisions should happen while sending data, such that only one node of data is sent at a time.
Types of Control Access Protocol Methods
The protocols or methods that come under control access methods in computer networks are as follows:
- Reservation Method
- Polling Method
- Token Passing Method
- CSMA/CD
- Aloha
- Time Division Multiplexing
These are the three important techniques for controlling access to a shared medium. Let’s dive deep into each protocol with their examples for a complete understanding of control access protocols in computer networks of a system clearly.
Reservation
Reservation is the first of the three major techniques to be implemented for controlling access. The title itself suggests that this process has something needs to be reserved.
A station using this approach must make a reservation before providing the data.
While making reservations, make sure before sending information that the above process involves a few steps for controlling the access of the protocols present in the system are as follows:
- The whole amount of the time is split into small intervals.
- A reservation frame comes before the data frame that is transmitted at each interval as well.
For better understanding, consider that there are X stations in a system. The time interval for reservations is divided into X slots. Every station has a unique small time slot.
Now, if the first station needs to send some data, it will send a few bits of information while others are not allowed to send any data. Every station has a clear idea of to which station it sends data for the transmission.
In that sequence, the stations will transfer their data frames on their corresponding time slot. that have reserved their slots transfer their frames. The subsequent reserve period starts after the data transmission time. There will never be any crashes because everyone has agreed on who will go next.
The reservation protocol for control access can be explained with a diagram containing multiple stations and mini slots with data frames in the below diagram:
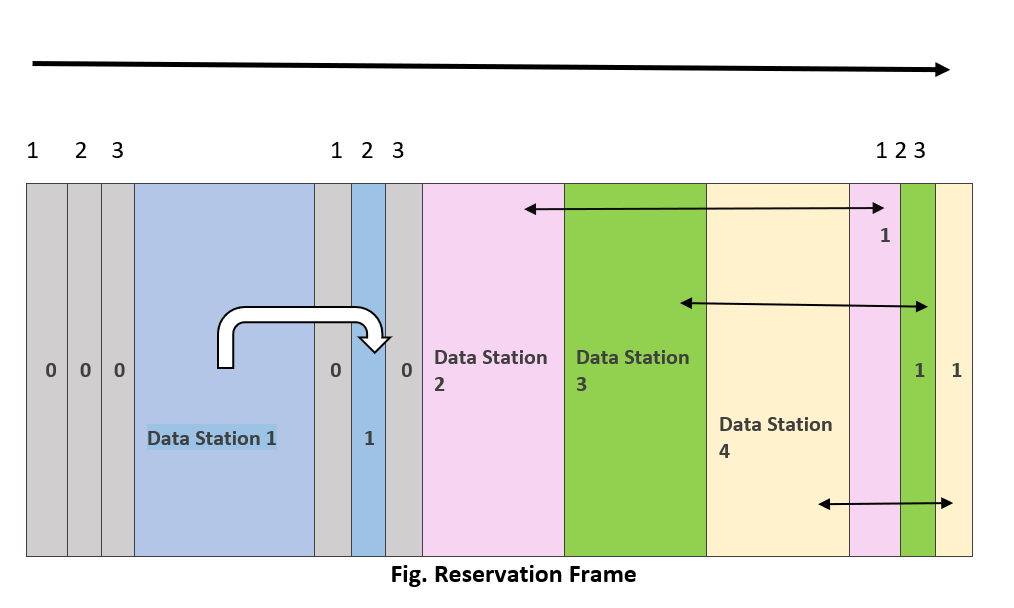
Diagram Explanation
The above diagram is the reservation frame in which it consists of stations and mini slots. In the above reservation frame, all the last three mini slots are booked by all the stations. That means that all the stations are reserved for sending the information one at a time. You can see that in the first interval, the first three slots are empty, and the next station is reserved by mini slots 2 and 1,3 are empty. The next occurring stations booked all the mini slots in the next interval, respectively.
Advantages of Reservation
- The main advantage of reservation is high and low rates of the data and accessing time of the respective channel can be predicted easily and rates and time are fixed.
- Priorities can be set to provide speedier access from secondary.
Drawbacks of Reservation
- High reliance on controller dependability
- Decrease in throughput and channel data rate under light loads; increase in turn-around time.
Polling
Polling is the second of the control access methods. In this method, different types of topologies are required. For implementing this polling method, the topologies are chosen based on the above condition, that is, the topology in which the first device is allotted as a primary station whereas the second device is the secondary station.
This will result in the main collection data will always start the session respectively.
The roll-call procedure used in class is comparable to the polling process. A controller works similarly to the instructor by communicating with each node one at a time. The controller's communication includes the address of the node it has chosen to allow access to. The controller's communication includes the address of the node it has chosen to allow access to.
In this scenario, one station serves as the controller and the others as backup stations. The controller must be used for all data transfers.
Even if all nodes get the message, only the one being addressed reacts and, if necessary, delivers data. A "poll reject" message is often returned if there is no data.
Important points to be noted while implementing Polling:
To enforce control on a network of independent users, one station must be established in the network to serve as a controller and to regularly poll every other station. This process is known as polling.
The important point in polling is all the data exchanging process must be held under the control of primary station. The end of the transmission is secondary station but only the first station is used for exchange.
Which device is permitted to utilise the channel at a certain moment must be decided by the primary device.
Advantages of Polling
- Never is a slot wasted.
- Maximum effectiveness and bandwidth use are the results.
Disadvantages of Polling
- Since each station has an equal opportunity to succeed in each round, link sharing is unreasonable.
- Polling is a waste of time and unnecessary.
- Only a few stations could run out of data to send.
Token Passing
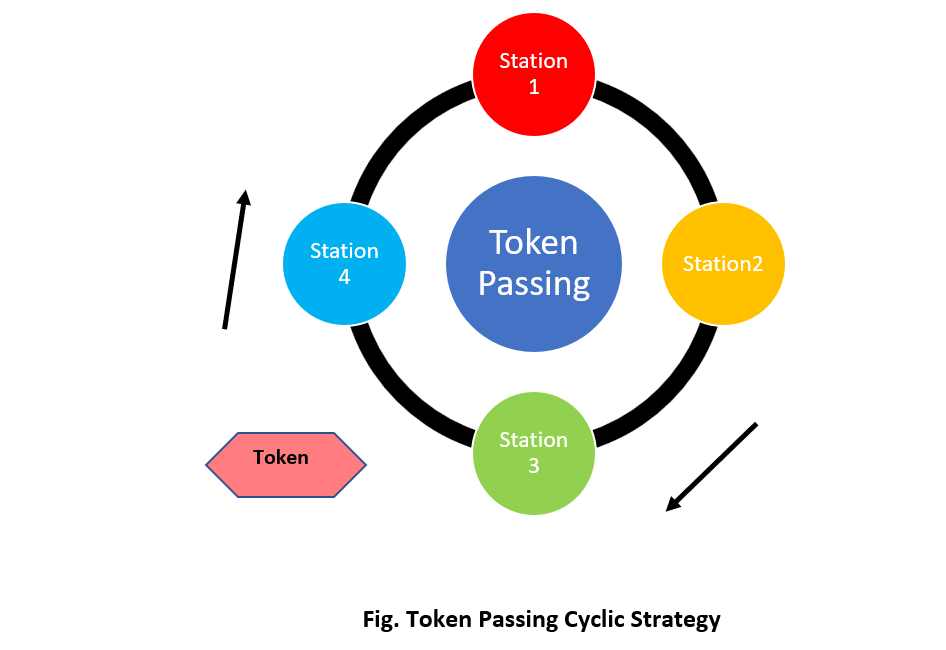
It is the third major technique for controlling access. In this method, access is done by tokens. In a simple explanation, the respective stations are formed in the form of a cycle or ring. There is a logical relation between the stations. All the access is covered by tokens.
Tokens are patterns, also called small messages, which travel through all the stations, informing all the stations of a little message in a defined order. The order is predefined and circulated in ring order.
Since it is in the ring order, when using a token bus, each station utilises the bus to deliver its token to the following station in a certain order, as opposed to passing the token from one station to another neighbouring station in a ring.
While sending the token for message passing, the token needs to be verified for permission. When there is a condition like a few of the frames are queued for the transmission, and at the same time, the token also comes, the transmission should be done before sending the token. After sending the data frame, the token will be sent for message passing to the next station.
Now, after completing the sending of a frame, the station needs to wait for all the stations to complete the token passing, and then the station, except itself, will wait for frame passing.
The problems that are faced in the token passing method of control access are losing tokens in the process or may be adding in or removing stations. And the token duplication is said to be the main drawback of token passing.
The diagrammatic representation of token passing is shown in the below diagram:
Advantages of Token Passing
1. It may now be utilised with Routers cabling and includes built-in debugging features like protective relay and auto-reconfiguration.
2. Under conditions of high load, it provides good throughput.
Disadvantages of Token passing
- It costs a lot to buy a token ring.
- Topology's components are all substantially more expensive than those of other, more widely used standards.
- The hardware elements of Token Ring are designed to be complicated. This implies that you should choose on a manufacturer and use them exclusively.
Other Important Control Access Protocols
There are few other control access protocols like
- Time division multiplexing
- Aloha
- CSMA / CD
Time Division Multiplexing
This process is somewhat like the polling method. The whole time is divided into equal time intervals. These time intervals are called "time slices" or "time slots."
The only difference between polling and division multiplexing is that it is implemented using a round-robin method. Transmission of data is done in the specific time slot given to the station. If there is no information to transmit, then the whole time allocated goes to waste.
Aloha
This aloha method is implemented and done in two ways. They are slotted and pure alohas respectively.
Pure Aloha
Pure Aloha states that the stations can send the data at their convenience, whereas it waits for some time after sending. They can send information whenever they want.
Slotted Aloha
In the slotted aloha method, the whole-time interval is parted ways into different time slots. Unlike previous processes discussed above, the stations can send the data at any time. The drawback of this slotted aloha is collision. It states that if stations transfer the data at the same time, collision may occur.
The condition that needs to be noted while implementing slotted aloha is that sending data needs to be done from the beginning state. If the stations lose the beginning slot, then the station needs to wait until all the stations send the data and then start again from the beginning slot to start sending data again.
CSMA/CD
Carrier Sense Multiple Access / Collision Detection are the abbreviations of CSMA and CD respectively. The CSMA protocol's addition is collision detection. As a result, a process that governs how communication must occur in a network with a shared transmission medium is established. The addition also specifies what to do in the event of collisions, which happen when two or more nodes attempt to transfer data packets across the transmission medium (bus) at the same time and obstruct one another.
The steps that are implemented in this control access method are
- Carrier sensing
- Collision detection
- Releasing jam signal
- Wait for back off time