What is Network Topology and Types in Computer Networks?
Network topology refers to the layout or organization of a computer network, including the physical and logical arrangement of devices on the network. It describes how the different devices in a network are connected to one another and how they communicate. This includes the arrangement of devices, the types of connections between them, and the flow of data through the network. Different types of network topologies have their own unique characteristics, advantages, and disadvantages, and the choice of topology depends on the specific requirements of the network. Network topology is a crucial aspect of network design and deployment, as it determines the performance, scalability, and reliability of a network.
Network topology is a detailed and comprehensive concept that encompasses both the physical and logical layout of a network. It is the way in which the various elements of a communication network are arranged, including the devices, links, and protocols that make up the network.
The physical topology of a network refers to the physical layout of the network and the location of devices and the cables that connect them. This includes the type of cabling used (such as copper, fiber optic, etc.), the type of connectors used (such as RJ-45, SFP, etc.), and the distance between devices. Common physical topologies include bus, star, ring, mesh, and tree.
The logical topology of a network refers to the way in which data is transmitted through the network, regardless of the physical layout. This includes the type of communication protocols used, such as TCP/IP, and the method of data transmission, such as circuit switching, packet switching, or message switching.
In addition, there are also Hybrid topologies, which combine the characteristics of two or more basic topologies, such as Star-Bus, Star-Ring, and so on.
Each topology has its own advantages and disadvantages. For example, a bus topology is simple and inexpensive to implement but a single point of failure can take down the entire network. A star topology is more resilient but requires more cabling and infrastructure. A mesh topology is highly resilient but can be difficult and expensive to implement.
When designing or implementing a network, it is important to carefully consider the specific requirements of the network and choose the appropriate topology to meet those requirements. Factors to consider may include the size of the network, the number of devices, the required level of availability, and the budget for the project.
Properties of Network Topologies
There are several properties of network topology that are important to consider when designing or implementing a network. These include:
- Scalability: The ability of the network to expand and accommodate more devices or users as needed. This is an important property for networks that need to grow or change over time. A scalable topology is one that can accommodate new devices or users without requiring a significant redesign of the network.
- Fault tolerance: The ability of the network to continue functioning even if one or more devices fail. This is an important property for networks that need to be highly available and resilient. A fault-tolerant topology is one that can continue to function even if one or more devices fail, either by providing redundant paths for data to travel or by using redundant devices that can take over if the primary device fails.
- Redundancy: The ability of the network to provide multiple paths for data to travel, so that if one path becomes unavailable, data can still be transmitted along another path. This is an important property for networks that need to be highly available and resilient. A redundant topology is one that provides multiple paths for data to travel, so that if one path becomes unavailable, data can still be transmitted along another path.
- Bandwidth: The amount of data that can be transmitted through the network at any given time. This is an important property for networks that need to support a large amount of data transfer, such as multimedia or large file transfers. A high-bandwidth topology is one that can support a large amount of data transfer, such as fiber-optic cabling or high-speed switches.
- Latency: The amount of time it takes for data to travel through the network. This is an important property for networks that need to support real-time applications such as VoIP or video conferencing. A low-latency topology is one that can support real-time applications by minimizing the amount of time it takes for data to travel through the network.
- Security: The ability of the network to protect against unauthorized access or data breaches. This is an important property for networks that handle sensitive or confidential information. A secure topology is one that includes measures to protect against unauthorized access or data breaches, such as firewalls, VPNs, or encryption.
- Cost: The cost of implementing and maintaining the network, including the cost of devices, cabling, and other infrastructure. This is an important property for networks that need to be implemented within a budget. A cost-effective topology is one that can be implemented and maintained at a reasonable cost.
- Manageability: The ease with which the network can be configured, managed, and troubleshot. This is an important property for networks that need to be easily manageable by the IT staff. A manageable topology is one that is easy to configure, manage, and troubleshoot such as a star topology.
As stated earlier, these properties can interact with each other and trade-offs can be made in order to achieve a balance between them. For example, a network with a high level of fault tolerance may be more expensive to implement and maintain but it will also be more reliable and available.
Types of Network Topology
There are several common types of network topologies which are given below:
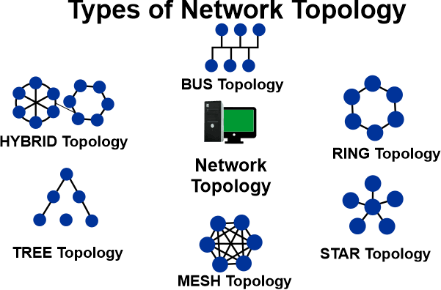
Fig 1.2: Types of Network Topology
1. Bus Topology
Bus topology is a type of network topology in which all devices are connected to a single cable, called a bus. In this type of topology, the bus acts as a backbone for the network and all devices connect to it directly or through a T-connector.
In bus topology, data is transmitted in a sequential manner, meaning that the data is sent to all devices connected to the bus in a continuous stream. All devices on the network can access the data but only the device that is addressed can accept and process it.
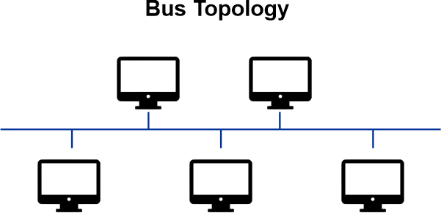
Fig 1.3: Bus Topology
Here are some of the characteristics of bus topology:
- Linear: The bus cable is a linear cable that connects all devices in a line.
- Single cable as backbone: The bus cable acts as the backbone of the network and all devices connect to it directly or through a T-connector.
- Data transmission: Data is transmitted in a sequential manner, meaning that the data is sent to all devices connected to the bus in a continuous stream.
- Addressing: Each device on the network has a unique address, and only the device with the matching address can accept and process the data.
- Easy to implement and manage: Bus topology is simple and inexpensive to implement and easy to set up and manage.
- Limited scalability: As the number of devices on the network increases, the amount of traffic on the bus also increases, which can lead to data collisions and slow down the network.
- No redundancy: Bus topology does not provide redundancy, meaning that if the bus cable or any device connected to it fails, the entire network will go down.
- Limited security: Bus topology does not offer a high level of security, and it is vulnerable to eavesdropping, tampering, and other malicious activities.
- Limited fault tolerance: Bus topology does not have the ability to tolerate faults, and a single point of failure can take down the entire network.
Advantages of Bus Topology
Some advantages of bus topology are:
- Easy to implement: Bus topology is simple and inexpensive to implement, as it only requires a single cable to connect all devices.
- Easy to manage: It is easy to set up and manage, which makes it well-suited for small networks or home networks.
- Low cost: The cost of the cable and the connectors is relatively low compared to other topologies.
- Suitable for small networks: Bus topology is well-suited for small networks, where the number of devices is limited and the network traffic is low.
Additionally, Bus topology is also easy to understand and troubleshoot, as all devices are connected to a single cable, making it easy to identify any issues or problems with the network.
Disadvantages of Bus Topology
Some disadvantages of bus topology include:
- Limited cable length: The maximum cable length for a bus topology is limited, typically around 500 meters. This can make it difficult to expand or connect large networks.
- Single point of failure: In a bus topology, if the main cable fails, the entire network will fail. This can cause significant downtime for users.
- Limited number of devices: The number of devices that can be connected to a bus topology is limited by the number of available connections on the main cable.
- Difficult to isolate network problems: It can be difficult to identify and isolate network problems in a bus topology, as a problem with one device can affect the entire network.
- Limited scalability: Bus topology is not easy to expand, making it less suitable for large networks.
In summary, bus topology is a good choice for small and simple networks, where cost and simplicity are important factors. However, it may not be the best choice for larger or more complex networks that require more robustness and scalability.
2. Ring Topology
In a ring topology, devices are connected in a circular chain, with each device connected to exactly two other devices (one on either side). Data travels around the ring in one direction, passing through each device along the way. This type of topology is less common than others, such as the star and bus topologies, but it has the advantage of being highly fault-tolerant (if one device or connection fails, the rest of the network can still function). One of the example of ring topology is Token Ring network.
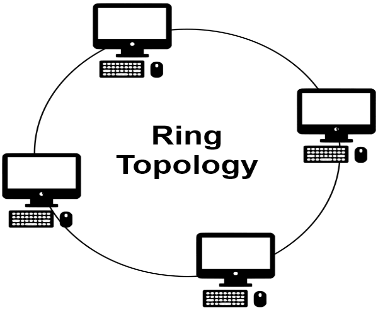
Fig: 1.4: Ring Topology
Characteristics of Ring Topology
Some of the key characteristics of a ring topology in a computer network include:
- Devices are connected in a circular chain, with each device connected to exactly two other devices.
- Data travels around the ring in one direction, passing through each device along the way.
- The ring topology is highly fault-tolerant, as the network can still function if one device or connection fails.
- It uses token passing protocol to avoid collision and to control the access of the network.
- It is less common than other types of topologies, such as the star and bus topologies.
- It is relatively more expensive to implement compared to other topologies.
- It is typically used in local area networks (LANs) and metropolitan area networks (MANs)
- It can be difficult to expand the network or add new devices once the ring is established.
Advantages of Ring Topology
Some of the advantages of using a ring topology in a computer network include:
- High fault tolerance: If one device or connection fails, the rest of the network can still function.
- Data integrity: Data is transmitted in one direction, which reduces the risk of data collisions and improves data integrity.
- Token Passing: Tokens are used to control access to the network, which helps to prevent data collisions.
- Isolation of devices: A device that is causing a problem on the network can be isolated without affecting the rest of the network.
- Good for real-time applications: Since there is a dedicated path for data, it is well suited for real-time applications such as audio and video streaming.
- Security: It is harder to tap into the network and steal information than other topologies, since data is transmitted in one direction and each device only receives the data intended for it.
Note: It is worth noting that ring topology is less used today and other topologies like star, mesh, and tree are more common.
Disadvantages of Ring Topology
Some of the disadvantages of using a ring topology in a computer network include:
- Limited scalability: It can be difficult to expand the network or add new devices once the ring is established.
- Single point of failure: If the ring is broken at any point, the entire network will fail.
- Limited throughput: Since all data must pass through each device on the network, the overall throughput may be limited.
- High cost of implementation: It can be relatively more expensive to implement a ring topology compared to other types of topologies.
- Limited flexibility: There is less flexibility in terms of how devices can be connected and reconfigured.
- Limited distance: The maximum distance between devices is limited, which can make it difficult to expand the network over a large area.
- Complex Maintenance: In case of any fault, it is difficult to detect and repair the problem.
- Limited support: Many newer devices and technologies may not be compatible with ring topologies, which can limit the types of devices that can be used on the network.
In conclusion, a ring topology network is a type of network architecture where all devices are connected in a closed loop, with each device connected to two other devices in the network. This type of topology offers some advantages such as high reliability and improved performance as data travels in one direction only. Additionally, it has specific characteristics such as no central point of failure, all devices have equal access to the network, and it's easy to detect and isolate problems.
3. Star Topology
A star topology is a type of network topology in which all devices are connected to a central hub. The hub acts as a central point of communication, controlling the flow of data between devices on the network. This topology is commonly used in home and small office networks because it is easy to set up and manage.
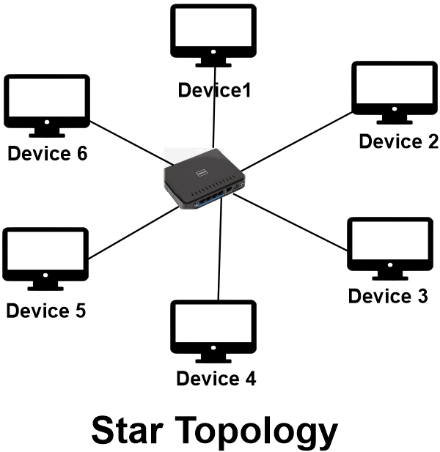
Fig 1.5: Star Topology
Characteristics of Star topology
Some characteristics of a star topology in a network include:
- Centralized hub: All devices in the network are connected to a central hub, which acts as a central point of connection and control.
- Point-to-point connections: Each device has its own dedicated point-to-point link to the central hub, providing a direct communication path.
- Independent devices: Each device in a star topology network is independent and has no direct connection to any other device, except through the central hub.
- Easy to expand: Adding new devices to a star topology network is relatively easy and can be done by connecting them to the central hub.
- Improved signal quality: Since each device has its own dedicated link to the central hub, signal quality is improved and noise and interference are minimized.
- Scalable: Star topology networks can be easily expanded by adding new hubs or switches to accommodate more devices.
- Easy to troubleshoot: Star topology networks can be easy to troubleshoot as it is easy to identify and isolate problems in the network.
Advantages of star topology
Some advantages of a star topology in a network include:
- Easy to install and configure: Each device in a star topology is connected to a central hub, making it easy to add or remove devices from the network.
- Isolated failures: If one device in a star topology network fails, it will only affect the connection to that specific device and not the entire network.
- High performance: Since each device has its own dedicated point-to-point link to the central hub, traffic congestion is minimized and overall network performance is improved.
- Easy to troubleshoot: Since each device is connected to a central hub, it is easy to identify and isolate problems in the network.
- Enhanced security: Star topology networks can be designed with security features such as firewalls and access controls that can be implemented at the central hub.
Disadvantages of Star topology
Some disadvantages of a star topology in a network include:
- Single point of failure: The central hub is a single point of failure, meaning that if it fails, the entire network will go down.
- Limited cable length and number of devices: The overall size of a star topology network is limited by the maximum cable length and the number of devices that can be connected to the central hub.
- Higher cost: A star topology network can be more expensive to set up and maintain due to the cost of the central hub and additional cabling required.
- Limited scalability: Adding new devices to a star topology network may require additional hubs or switches to be added, which can be costly and complex.
- Limited redundancy: In case of central hub failure, there is no backup hub or switch to take over which means no redundancy.
In conclusion, a star topology network is a type of network architecture where all devices are connected to a central hub. This type of topology offers many advantages such as easy installation and configuration, isolated failures, high performance, and easy troubleshooting. However, it also has some disadvantages such as a single point of failure, limited cable length and number of devices, higher cost and limited scalability. Additionally, it has specific characteristics such as centralized hub, point-to-point connections, independent devices, easy to expand, improved signal quality and easy to troubleshoot. Star topology is a great option for small to medium-sized networks as it provides a good balance of performance, security, and ease of management.
4. Tree Topology
Tree topology is a type of network architecture in which a central device (known as the root node) is connected to multiple other devices, which are connected to other devices in turn, creating a hierarchical structure that resembles a tree. Each level in the hierarchy represents a network segment, and all devices on a given level are connected to the level above it through a single connection to a parent device. This type of topology is commonly used in wide area networks (WANs) and large local area networks (LANs) to segment the network into smaller, more manageable sections.
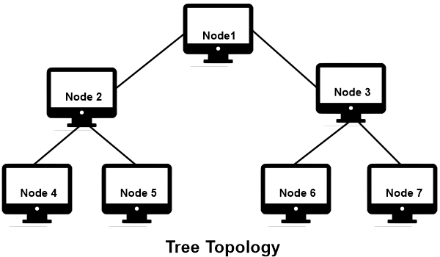
Fig 1.6: Tree Topology
Characteristics of Tree Topology
Some characteristics of tree topology in computer networks include:
- Hierarchical structure: The network is organized in a hierarchical manner, with a central device (root node) at the top and multiple devices branching out from it.
- Point-to-point connections: Each device is connected to one parent device and multiple child devices.
- Segmentation: The network can be divided into smaller segments, making it easier to manage and troubleshoot.
- Scalability: Tree topology can accommodate a large number of devices by adding more branches to the hierarchy.
- Redundancy: Each device has at least one backup path to the root node, providing redundancy in case of a failure.
- Limited Broadcast domain: The Broadcast domain is limited to the particular segment only and does not propagate to other segments
- Limited Bandwidth: As the network grows, the bandwidth available at the lower levels of the hierarchy may become limited.
- Centralized management: The root node acts as a central point of control and management for the entire network.
Advantages of Tree Topology
Some advantages of tree topology in computer networks include:
- Hierarchical structure: The network is organized in a hierarchical manner, making it easy to understand, manage and troubleshoot.
- Segmentation: The network can be divided into smaller segments, making it easier to manage and troubleshoot.
- Scalability: Tree topology can accommodate a large number of devices by adding more branches to the hierarchy.
- Redundancy: Each device has at least one backup path to the root node, providing redundancy in case of a failure.
- Centralized management: The root node acts as a central point of control and management for the entire network.
- Easier to add new devices: As new devices are added to the network, they can be easily connected to an existing branch, rather than requiring a complete rewiring of the network.
- Cost-effective: Tree topology is relatively inexpensive to implement and maintain compared to other network topologies.
- Suitable for WAN: Tree topology is suitable for wide area networks as it allows to connect multiple LANs together with a central hub.
Disadvantages of Tree Topology
Some disadvantages of tree topology in computer networks include:
- Single point of failure: The root node acts as a central point of control and management, and if it fails, the entire network may become inaccessible.
- Limited bandwidth: As the network grows, the bandwidth available at the lower levels of the hierarchy may become limited.
- Limited broadcast domain: The Broadcast domain is limited to the particular segment only and does not propagate to other segments.
- Not suitable for small networks: Tree topology may not be suitable for small networks as it can be complex to implement and manage.
- High maintenance: As the network grows, the number of connections and devices increases, which can make it difficult to manage and troubleshoot.
- Limited fault tolerance: If a link or device on a branch fails, the entire branch may become inaccessible.
- Limited security: Security measures need to be implemented at the root node, which can be difficult to manage, especially in large networks.
- Costly: As the network grows and more devices are added, the cost of maintaining and upgrading the network may become significant.
Another important aspect to consider is that tree topology is a logical topology, meaning it describes how the network is organized and how data flows through it, while the physical topology refers to how the devices and cables are actually connected. While the logical topology can be designed to be tree, the physical topology can be different.
In summary, tree topology is a hierarchical network structure that can be used to segment large networks and provide redundancy. It's a good choice for wide area networks (WANs) and large local area networks (LANs) but it has some disadvantages like single point of failure, limited bandwidth, limited broadcast domain, not suitable for small networks, high maintenance, limited fault tolerance, limited security and costly. The best topology choice should be based on the network's purpose, size, available resources and budget.
5. Mesh Topology
Mesh topology is a type of network architecture in which each device, or node, is connected to multiple other devices, creating multiple paths for data transmission between any two nodes. This allows for a more efficient use of network resources, as data can be transmitted over multiple paths, rather than relying on a single path as in a star topology. Additionally, it provides more resilience to failures as there are multiple paths for data to travel, so if one path is unavailable, the data can still be transmitted through an alternate path. This also helps to provide more bandwidth. However, it also requires more cabling and configuration.
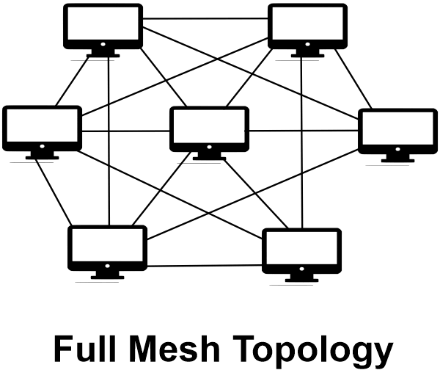
Fig 1.7: Mesh Topology
Mesh Topology divided into two categories:
- Full Mesh: In a full mesh topology, every device or node is connected to every other device or node. This provides the highest level of reliability and the most efficient use of network resources, but it also requires the most cabling and configuration.
- Partial Mesh: In a partial mesh topology, some devices or nodes may be connected to only a subset of the other devices or nodes. This provides a balance between reliability and cost, but it may not be as efficient as a full mesh topology.
Advantages of Mesh Topology
The advantages of a mesh topology are:
- Reliability: With multiple paths for data to travel, if one path is unavailable, the data can still be transmitted through an alternate path. This makes it more resilient to failures.
- Efficiency: In a mesh topology, each node acts as a relay for data transmissions, forwarding data packets to the next node on their way to their destination. This allows for a more efficient use of network resources, as data can be transmitted over multiple paths, rather than relying on a single path as in a star topology.
- Scalability: Mesh topologies can easily expand to accommodate new devices or nodes without significantly impacting the existing network.
- Flexibility: A wireless mesh topology can provide a flexible, reliable, and cost-effective network solution, especially in remote or hard-to-reach areas.
- Security: A mesh topology can provide increased security as each node in the network can act as a firewall, providing an added layer of protection for the network.
- Autonomous: A dynamic mesh topology can automatically discover and adapt to changes in the network, such as a new node being added or a node failure.
Disadvantages of Mesh Topology
The disadvantages of a mesh topology are:
- Cost: Implementing a mesh topology can be more expensive than other types of network topologies because it requires more cabling and configuration.
- Complexity: A mesh topology can be more complex to set up and manage than other types of network topologies.
- Limited scalability: In a full mesh topology, as the number of nodes increases, the number of connections and the complexity also increases exponentially, making it less scalable in certain situations.
- Limited bandwidth: In a partial mesh topology, some nodes may be connected to only a subset of the other nodes, which can result in limited bandwidth availability.
- Power consumption: Mesh nodes have to maintain multiple connections, which can lead to increased power consumption.
- Limited coverage: Wireless mesh topologies may have limited coverage areas, and may have difficulty penetrating walls or other obstacles.
- Interference: Wireless mesh networks are susceptible to interference from other wireless devices, which can disrupt the network.
In conclusion, mesh topology is a type of network architecture that provides multiple paths for data to travel between any two nodes, making it more reliable and efficient than other types of network topologies such as star topology. It can also be more scalable and provide more bandwidth. However, it can be more expensive to implement and manage, and can be more complex than other types of network topologies. Additionally, in certain situations it can be less scalable and may have limited coverage and suffer from interference. The choice of a mesh topology or any other topology depends on the specific requirements and constraints of the network and the organization.
6. Hybrid Topology
A hybrid topology is a type of network architecture that combines two or more different types of network topologies. For example, a network that combines a star topology with a bus topology is considered a hybrid topology. The purpose of a hybrid topology is to combine the strengths of different topologies while minimizing their weaknesses.
One example of a hybrid topology is a "star-bus" topology, which combines the centralization and easy management of a star topology with the linear scalability of a bus topology. In this topology, all devices are connected to a central hub, but the hub is also connected to other hubs in a linear fashion, creating a bus network.
Another example is "tree-mesh" topology, which combines the advantages of a hierarchical tree topology with the advantages of a full-mesh topology. In this topology, a central node or hub is connected to multiple nodes in a hierarchical fashion but these nodes are also connected to multiple other nodes.
Hybrid topologies are often used in large-scale networks such as enterprise networks, where the combination of different topologies can provide a more flexible and efficient network solution.
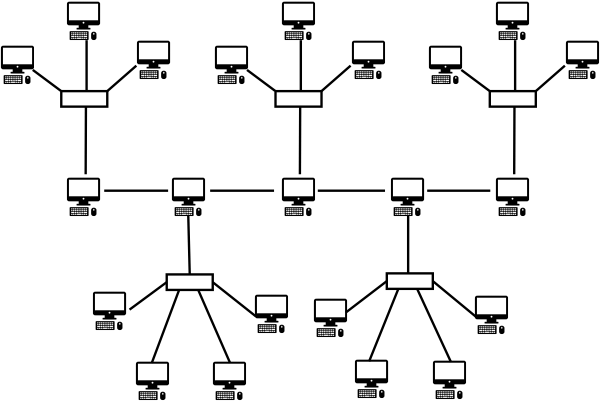
Fig 1.8: Hybrid Topology
Characteristics of Hybrid Topology
Some characteristics of hybrid topologies in computer networks include:
- They can improve network performance by utilizing the strengths of different topologies.
- They can provide redundancy and failover capabilities to increase network availability.
- They can provide a higher level of security and control over network traffic.
- They can be used to connect different types of network devices and segments together.
- They can be used to connect different geographical locations together.
- They can be more complex to design, configure and maintain than a single type of topology.
- They can be more expensive than a single type of topology.
- They can provide a balance between the advantages and disadvantages of different topologies.
Advantages of Hybrid Topology
Some advantages of using a hybrid topology include:
- Flexibility: A hybrid topology allows for the combination of the strengths of different topologies, such as the high fault tolerance of a ring topology and the high data transfer rate of a bus topology.
- Scalability: As a network grows, a hybrid topology can be easily expanded by adding new devices or connections.
- Cost-effectiveness: By combining different topologies, a hybrid topology can reduce the overall cost of a network by utilizing the most cost-effective topology for each segment of the network.
- Improved performance: A hybrid topology allows for the use of different topologies in different parts of the network, which can improve the overall performance of the network.
- Security: By using different topologies in different parts of the network, it can be more difficult for unauthorized users to access the network.
Disadvantages of Hybrid Topology
Some disadvantages of using a hybrid topology include:
- Complexity: A hybrid topology is more complex than a single topology, which can make it more difficult to troubleshoot and maintain.
- Configuration: Configuring a hybrid topology can be more difficult than configuring a single topology, as different parts of the network may have different requirements.
- Cost: Implementing a hybrid topology can be more expensive than implementing a single topology, as more devices and connections may be required.
- Limited compatibility: Not all devices are compatible with all topologies, so compatibility issues may arise when trying to connect devices in a hybrid topology.
- Limited scalability: depending on the combination of topologies used in a hybrid network, it may become difficult to scale it up or down in the future.
Additionally, it's important to note that a Hybrid topology is not a standard or predefined topology like Star, Bus, Mesh or Ring. It's a combination of one or more topologies. Therefore, it's important to carefully plan the design of a hybrid topology to ensure that it meets the requirements of the network and that it is easy to manage and maintain. It's also important to ensure that the devices and connections used in a hybrid topology are compatible with each other. In summary, a Hybrid topology can offer a lot of benefits for a network but it also comes with a set of challenges.
It's a good option when you have specific needs that can't be met by a single topology, but it's important to carefully plan the design and manage it properly.
Examples of Network Topology Tools and Software
There are several network topology tools and software available, some examples include:
- SolarWinds Network Topology Mapper: This software automatically discovers and maps network topology, and can generate detailed network diagrams.
- Microsoft Visio: Visio is a popular diagramming software that can be used to create network topology diagrams.
- Cisco Network Topology Icons: Cisco provides a set of icons that can be used to create network topology diagrams.
- PRTG Network Monitor: This software can be used to monitor and map the network topology in real-time.
- OpManager: This software can be used to monitor and map the network topology and also to manage network devices.
- Netbrain: This software can be used to create a map of the network topology, automate network documentation, and troubleshoot network issues.
- Nagios: This software can be used to monitor network devices and network topology, alerting administrators to any issues that arise.
Above are just a few examples of the many network topology tools and software available. It's important to choose a tool or software that meets the specific needs of your network and that is compatible with your existing network devices and infrastructure.