Differences Between Trunk Port and Access Port
This article will help you in providing a detailed comparison between Trunk Port and Access port. Before comparing trunk and access port let us understand what they are.
What is a Trunk port?
In computer networking, a trunk port is a type of port that is used to carry traffic between network switches. Specifically, a trunk port is a port that can carry multiple VLANs (virtual LANs) simultaneously, as opposed to an access port that carries traffic for only one VLAN.
When two switches are connected, they exchange information about the VLANs that they have configured. The trunk port on each switch is responsible for carrying traffic for all of the VLANs between the switches. This allows the switches to communicate with each other and enables devices on different VLANs to communicate with each other.
For a port to be designated as a trunk port, it must be configured to use a trunking protocol, such as IEEE 802.1Q. This protocol adds a special header to Ethernet frames, which indicates the VLAN to which the frame belongs. When a frame is received on a trunk port, the switch reads the VLAN ID from the header and forwards the frame to the appropriate VLAN.
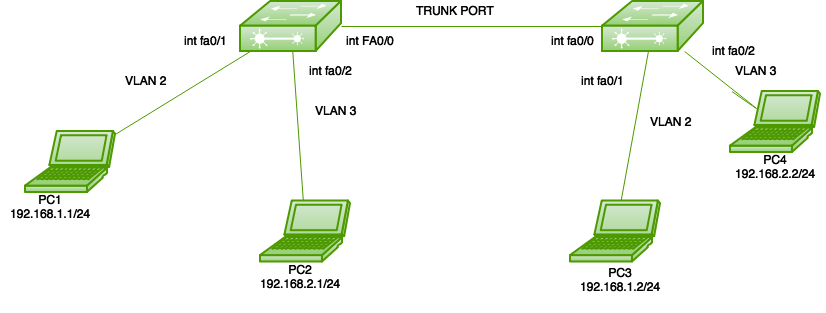
Trunk ports are commonly used in enterprise networks to segment traffic and improve network performance. By separating traffic into different VLANs, network administrators can reduce network congestion and improve the overall efficiency of the network. Trunk ports are also used in virtualization environments, where they allow virtual machines running on different hosts to communicate with each other as if they were on the same physical network segment.
What is Access Port?
Top of FormIn computer networking, an access port is a type of port on a switch that is used to connect end devices, such as computers, printers, or servers. An access port is designed to carry traffic for only one VLAN (virtual LAN) at a time, unlike a trunk port, which can carry traffic for multiple VLANs.
When a device is connected to an access port, it is automatically assigned to the VLAN that is configured on the access port. This allows network administrators to control which devices can communicate with each other on the network. Access ports are typically used to connect end devices to the network, while trunk ports are used to connect switches and carry traffic for multiple VLANs.
Access ports are usually configured with a specific VLAN ID, which determines which VLAN the port belongs to. When a device sends traffic on an access port, the switch adds the VLAN ID to the Ethernet frame, and forwards the traffic to other devices on the same VLAN. If the device sends traffic to a device on a different VLAN, the switch blocks the traffic from reaching the other VLANs.
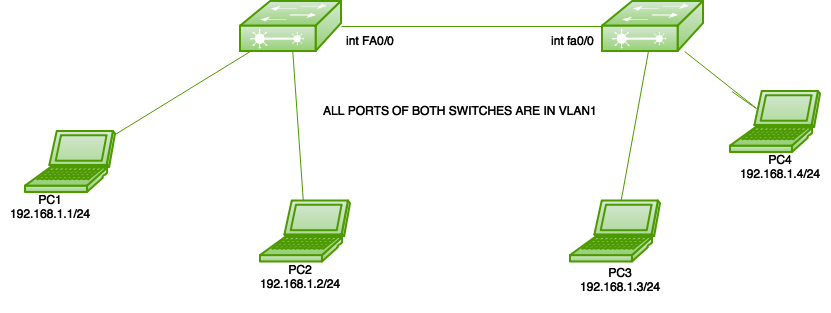
In addition to separating network traffic, access ports are also used to provide security and control over the network. By assigning devices to specific VLANs, network administrators can prevent unauthorized access to the network and reduce the risk of security breaches.
Access ports are an important component of network design and are commonly used in both small and large networks. They provide a way to manage network traffic and ensure that devices are connected to the appropriate VLANs, which helps to improve network performance and security.
Differences between Trunk and Access Port
| S.No | Trunk Port | Access Port |
| 1. | It is Used to connect switches. | It is Used to connect end devices, such as computers, printers, or servers. |
| 2. | It carries traffic for multiple VLANs simultaneously. | It carries traffic for only one VLAN at a time. |
| 3. | Trunk Port must be configured with a trunking protocol, such as IEEE 802.1Q. | Access Port does not require any special configuration. |
| 4. | It allows switches to communicate with each other. | It does not allow switches to communicate with each other. |
| 5. | It can carry traffic for all VLANs configured on the switch. | It can carry traffic for only one VLAN configured on the switch. |
| 6. | It can be used to connect switches in different locations or buildings. | It typically used to connect end devices within the same location or building. |
| 7. | It is used to reduce network congestion and improve performance. | It is used to provide security and control over the network. |
| 8. | It is used to segment network traffic. | It is used to isolate devices and control which devices can communicate with each other. |
| 9. | It is used in virtualization environments to enable communication between virtual machines. | Access Port is not used in virtualization environments. |
| 10. | It allows devices on different VLANs to communicate with each other. | It does not allow devices on different VLANs to communicate with each other. |
| 11. | It can be used to carry multiple types of traffic, such as voice and data. | It typically used to carry only data traffic. |
| 12. | Trunk Port must be manually configured with the appropriate VLAN IDs. | It automatically assigns devices to the VLAN configured on the port. |
These are some of the key differences between trunk ports and access ports. Understanding these differences is important for designing and configuring effective network topologies. So, this is all about the comparison between trunk and access ports. Hope you understood this topic.