Lock Variable Mechanism | Operating System
Lock Variable Mechanism
The Lock variable mechanism is a synchronization mechanism that is implemented in a user mode. It is a software procedure.
Lock variable is a solution for busy waiting that can be easily applied by more than two processes.
In the lock variable mechanism, we use a lock variable, i.e., Lock. There are two values of Lock variable, which are 1 and 0. If the value of Lock is 1, then it means the critical section is occupied, but if the value of lock is 0, then it means the critical section is empty.
If a process wants to enter into the critical section, then first the process checks the value of Lock variable, and if the value of lock is 0, then we set the value of lock as 1, and after setting the value, the process enters into the critical section. Otherwise, the process waits for its turn.
The Pseudocode of the lock variable mechanism is:
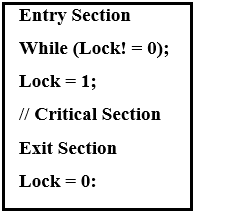
In the following Pseudocode, we have three sections, i.e., Entry section, Critical section, and the exit section.
Initially, the value of the lock variable was 0. When any process wishes to enter into the critical section, it checks the condition of the while loop. It continuously waits until the value of the lock variable is 1. Because to enter, the value of lock variable should be 1. So, it is clear that initially, the critical section is empty, and thus the process enters into the critical section, and the value of the lock variable sets to1. This means another process will wait until the value becomes 0. In the exit section, we will reset the value of lock variable as 0 when the process will exit from the critical section.
Based on four conditions, we judge every Synchronization Mechanism:
- Mutual Exclusion
- Progress
- Bounded Waiting
- Portability
In the above four conditions, the Mutual Exclusion, and Progress are the most important. So, it should be provided by each solution.
Now, based on four mentioned conditions, we analyze the synchronization mechanism:
Mutual Exclusion
In few cases, Lock Variable Mechanism does not offer mutual exclusion. By writing the pseudocode in assembly language, we can easily understand this by the point of view of the operating system.
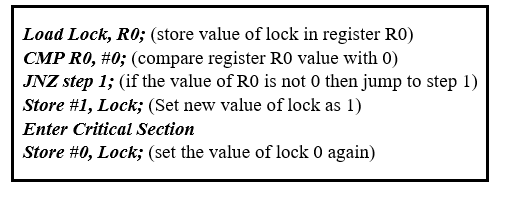
Suppose we have two processes namely P1 and P2. Process P1 needs to execute into the critical section. Thus, it enters into the entry section. So, initially, the value of the lock variable is 0, so we need to change the value of lock variable from 0 to 1, and then the process can enter in the critical section.
During this, the CPU preempts the process P1 and scheduled the process P2. Thus, it is found critical section is empty. Hence, the value of the lock variable is 0. The process P2 is also wishing to execute in the critical section. Thus, it enters into the critical section and sets the lock to 1.
After that CPU wants to switch the state of process P1from waiting state to the running state. Till now, the process P1 did not completed its execution in the critical section. The process P1 previously checked the lock variable value, and that time the Lock variable value was 0. So, P1 can enter the critical section and does not need to verify the updated value of lock.
Now there are two processes that are present in the critical section, but on the basis of mutual exclusion condition at the same time, no two processes stay in the critical section. So, the lock variable mechanism does not provide the assurance of mutual exclusion.
The limitation of a lock variable mechanism is that more than two processes can see the empty tag at the same time, and also more than one process is able to get enter into the critical section.
That’s why the lock variable mechanism does not offer the facility of mutual exclusion. That’s the reason why lock variable cannot be used.
So, the lock variable mechanism fails at the initial phase. Thus, the lock variable holds a very limited scope.