Resource Allocation Graph in Operating System
Resource Allocation Graph in OS
We use the resource allocation graph for the pictographic representation of the state of a system. The resource allocation graph contains all the information related to the processes that are holding some resources and also waiting for some more resources.
Resource allocation graph consists of all the information which is related to all the instances of the resources means the information about available resources and the resources which the process is being using.
In the Resource Allocation Graph, we use a circle to represent the process and rectangle to represent the resource.
Components of RAG (Resource Allocation Graph)
There are two components of the resource allocation graph:
- Vertices
- Edges
- Vertices: - In the resource allocation graph, we use two kinds of vertices:
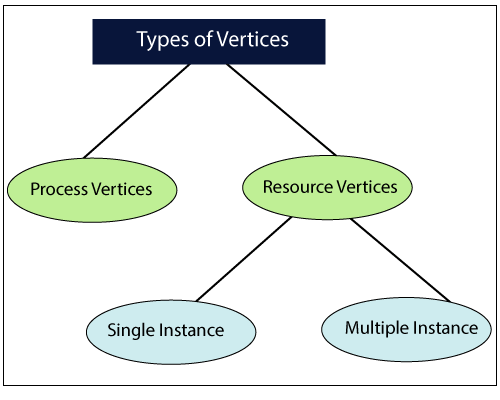
- Process Vertices
- Resource Vertices
Process Vertices: - To represent a process, we use process vertices. We draw the process vertices by using a circle, and inside the circle, we mention the name of the process.
Resource Vertices: - To represent a resource, we use resource vertices. We draw the resource vertices by using a rectangle, and we use dots inside the circle to mention the number of instances of that resource.
According to the number of instances that may exist in the system, there are two types of resource vertices, i.e., single instance and multiple instances.
Single instance resource type: - In single instance resource type, we use only a single dot inside the box. The single dot indicates that there is one instance of the resource.
Multiple instance resource type: - In multiple instance resource type, we use multiple dots inside the box. Multiple dots indicate that there are various instances of the resources.
2. Edges: - There are two types of edges we use in the resource allocation graph:
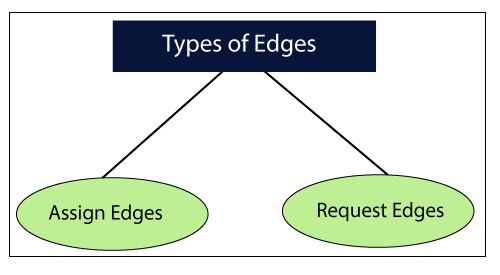
- Assign Edges
- Request Edges
Assign Edges: - We use an assign edge to represent the allocation of resources to the process. We draw assign edges with the help of arrow in which the arrow head points the process, and the process tail points the instance of the resource.
Request Edges: - We use request edge to signify the waiting state of the process. Just like in assign edge, an arrow is used to draw arrow edge. Here, the arrow head points the instance of a resource, and tail of the process points to the process. For example, if a process needs ‘n’ instances of resource type, then we will draw ‘n’ assign edges.
Example of (RAG) Resource Allocation Graph
Example of Single Instance Resource Type
In the following example, we have two processes P1, and P2 and two resources which are R1, and R2. This example is a kind of single instance resource type, and it contain a cycle, so there is a deadlock in the system.
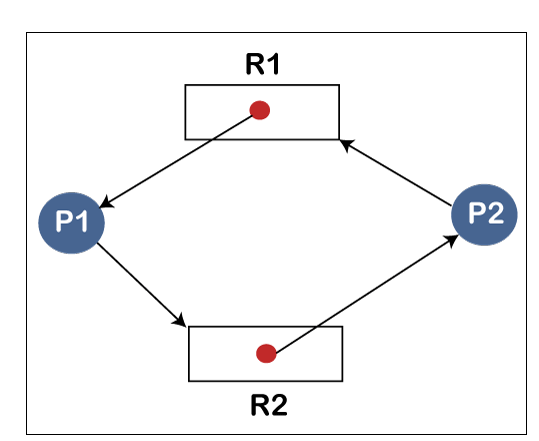
| Allocation | Request | |||
| R1 | R2 | R1 | R2 | |
| Process P1 | 1 | 0 | 0 | 1 |
| Process P2 | 0 | 1 | 1 | 0 |
Available = [R1 R2] = [0 0]
We can see in the following table, there is no instance of resource available, and to execute the process we need a resource. So, no process will be executed, and both the processes keep waiting for a long time. So, we can say that there is a deadlock in the system.
- Example of Multiple Instance Resource Type
The term multiple instances means the resources are having more instances. In the following example, we have three processes, which are P1, P2, and, P3 and three resources, which are R1, and R2.
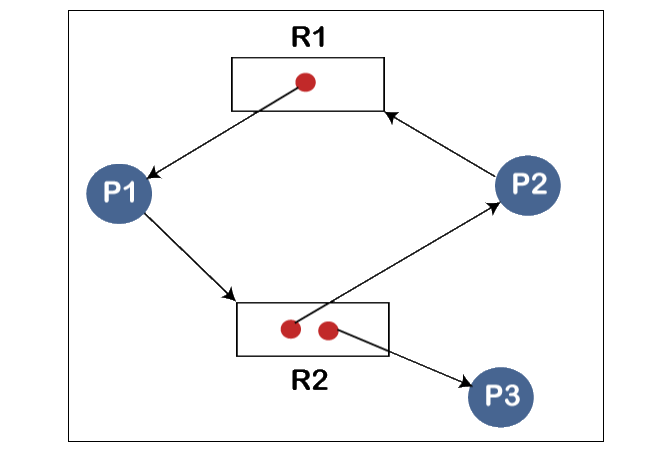
| Allocation | Request | |||
| R1 | R2 | R1 | R2 | |
| Process P1 | 1 | 0 | 0 | 1 |
| Process P2 | 0 | 1 | 1 | 0 |
| Process P3 | 0 | 1 | 0 | 0 |
Now we check the current Availability = [R1 R2] = [0 0]
Now by using this availability, we check whether we can fulfill the request of any of the processes or not.
We can fulfill the demand or request of P3 because P3 is demanding nothing. So, when the process P3 gets successfully executed, we terminate the process P3.
Then we calculate availability,
Availability = [0 0] + [0 1]
= [ 0 1]
Now, based on the current availability, we can fulfill the requirement of the P1 process. So, we assign the requested resource to the process P1. When the process P1 executes successfully, then we terminate the process P1.
Now we again calculate availability
Availablity = [0 1] [1 0]
= [1 1]
Now, again based on the current availability we fulfill the requirement of process P2 because the P2 process satisfies the requirement. So, we allocate the requested resource to the Process P2. When the process P2 executes successfully, then it terminates, and we again calculate the availability.
Availability = [1 1] + [0 1]
= [1 2]
So, in this example, there is a safe sequence P3, P1, P2, and all the processes are executed successfully. So, we can say that system is in a safe state, and there is no deadlock in the system.
Related Posts:
- Components of Operating System
- File Access Methods in Operating System
- Directory Structure in Operating System
- File Allocation Methods in Operating System
- Banker’s Algorithm in Operating System
- Virtual Memory in Operating System
- Paging and Segmentation in OS
- Fixed Partitioning in Operating System
- Disk Scheduling Algorithms
- Look Disk Scheduling
- Turn Variable or Strict Alternative Approach
- Strategies for Handling Deadlock