Organizational Structure and Development in Debian Operating Systems
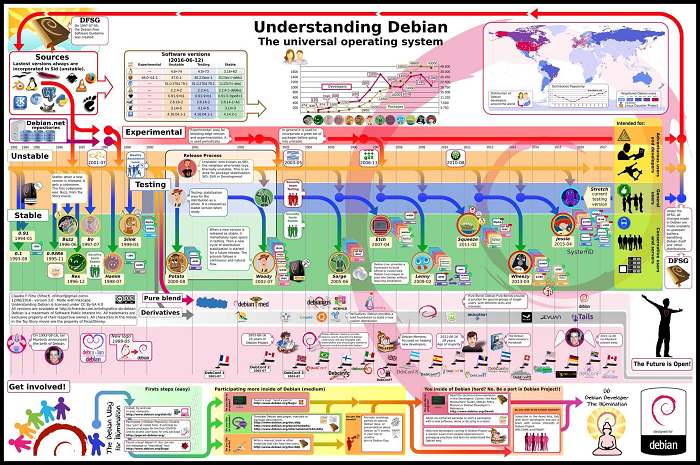
The most widely used version of Debian for desktop PCs and servers is the Stable branch. Numerous other versions, most famously Ubuntu, are built on top of Debian. The next candidate is published following a time-based freeze, and new versions are continuously updated. Debian has always created and disseminated the GNU Project's guiding principles freely. The Debian Project is a group of people united in their desire to develop an open operating system. Debian is the name of the operating system that we have developed.
- Collecting fundamental applications and tools on your computer is an operating system.
- The computer's kernel, which performs all the necessary housekeeping and enables you to launch other programs, is its most essential application.
- A piece of Software called Linux was created by Linus Torvalds and is backed by thousands of coders all over the globe.
- An operating system called FreeBSD comes with a kernel and other programs.
Debian for other systems, mainly for the Hurd, is being developed, though. The GNU effort created the Hurd as open Software. The terms GNU/Linux, GNU/FreeBSD, and GNU/Hurd refer to operating systems composed mainly of fundamental tools that are a product of the GNU effort. Also complimentary are these resources.
Of course, people want application software, which includes tools for everything from document processing to business management, gaming, and creating new Software. It has tower-like qualities. The nucleus is at the center. All of the fundamental instruments are on top of that. The program that you use to operate your computer comes next. Debian, meticulously arranging and fitting everything to function together, sits atop the structure.

Organization
The principles of Debian and the team's initiatives center on cooperative software creation and testing procedures. Consequently, significant releases are updated every two years to address security flaws and other pressing issues.
There are three founding papers for the volunteer-run Debian project:
- A collection of fundamental guidelines for how the project and its developers should behave themselves are laid out in the Debian Social Contract.
- The Debian Free Software Guidelines outline what constitutes "free software," thereby defining the types of programs allowed in the release. The foundation of the Open-Source Definition is based on these rules.
- It lists the duties of the Project Leader, the Secretary, and other roles, although it can be argued that this document stands alone and is not a part of the Social Contract.
- A network of confidence holds together the Debian developer community. Although there are about a thousand active Debian engineers, anyone can contribute to the project without being a registered developer. The initiative runs conferences and formal mailing groups for developer contact and coordination. Developers and end users use a public bug recording system to trace problems with individual packages and other duties. Internet Relay Chat is also used for coder collaboration and real-time support.
- Donations to groups approved by the leader are used to help Debian. The biggest ally is Software in the Public Interest, which also serves as the umbrella group for several other community-based free software initiatives and owns the Debian brand.
- The coders pick a project leader once a year. The leader assigns representatives to carry out specific duties and has unique powers, though they are not absolute. Delegates make choices based on what they believe is best while considering agreement and technological standards. The Schulze technique is used to conduct the polling. (Cloneproof Schwartz Sequential Dropping).
- Occasionally, project authority is shared. The Project Scud crew of developers aided Branden Robinson, but there were worries that such leadership would divide Debian into two developer classes. Second In Charge (2IC), a new post established by Anthony Towns, shared some of the leader's authority. Steve McIntyre had a 2IC and was himself a 2IC.
- The release team plans the next release, monitors the procedures, and selects the release window. The steady-release managers and following-release managers serve as the team's leaders. In 2003, release aides were first used.
- Coders, The Debian Project, receives many applications from people looking to work as coders. These candidates must undergo a screening procedure to confirm their identification, desire, comprehension of the project's guiding principles, and technical proficiency. Over time, this procedure has gotten much more difficult.
- The initiative attracts Debian developers for a variety of causes. They also want to improve the support for their preferred technology. They want to give back to the free-software community. They want to make their Debian maintenance work more accessible.
- Debian developers can quit their roles at any moment or, if required, be expelled. The "emeritus" designation is given to those who follow the retiring procedure and are eligible to rejoin after a shorter new member process.
Development
Each piece of Software has a maintainer, a single individual, or a group of Debian writers and non-developers. The maintainer monitors source versions and ensures the package complies with Debian's quality standards and the rest of the distribution.
The package is uploaded to the "incoming" system, which checks the authenticity of the boxes and their digital signatures, by the administrator to issue a new version. If the package is legitimate, it is put in the package archive into a section known as the "pool" and sent out daily to many mirrors around the globe. The file needs to be verified with an OpenPGP-capable program. Each Debian coder has their own unique set of cryptographic keys. If another user created the packaging, developers are still accountable for any packages they submit.
An approved package is initially only accessible from the unstable version. A box must move to the Testing branch and satisfy the following requirements to be considered a contender for the upcoming release:
- It does not contain "release-critical" defects aside from those already present in testing;
- It has been unstable for a period that relies on the urgency of the changes. Release-critical weaknesses are those that are deemed necessary enough to prevent the program from being released.
- For any final translation, there are no out-of-date variants in unstable.
- The move breaks no Testing tools.
- Packages that are currently in testing or boxes that are migrating simultaneously can satisfy its requirements.
- A cold does not impede movement.
- For any final translation, there are no out-of-date variants in unstable.
- The move breaks no Testing tools.
- Packages that are currently in testing or boxes that are migrating simultaneously can satisfy its requirements.
The migration procedure occurs twice daily from the branch's perspective, keeping testing in a state of continuous beta. The release team periodically posts instructions for coders to follow as they prepare the release. After a halt, a new release happens when all crucial Software is relatively current in the Testing branch and any other pressing problems are resolved.
At that point, the testing branch becomes the new stable branch and contains all files. While release dates, published by the release administrators a few weeks beforehand, are not time-based, freeze dates are. More than one branch, typically experimental and unstable, can contain a given version of a program.
A package may simultaneously be a component of old stable, stable, practical, and dangerous and maintain the same performance across stable versions. A gathering of references into the package above "pool" can be thought of as what each branch is. Using alternative package managers is one approach to overcoming the problem of a release-critical flaw in a new application version. They maintain security management while enabling software writers to use sandbox settings.
Discharge sequence
About every two years, Debian releases a new stable version. For roughly three years, it will receive maintenance and updates for significant security or usability improvements. Stable Release Managers will decide how frequently Point Releases are made accessible. (SRM). Since Debian 6, Debian has also started its Long-Term Support (LTS) initiative. (Debian Squeeze). Now, Debian releases are eligible for five years of security assistance.
Security
The Debian group manages security via open communication. Before Steve Kemp resigned in 2011, there was a security assessment project that concentrated on packages in the stable version to search for security flaws. In 2014, he restarted his work and requested to return.
The Debian security team provides ongoing help for the stable branch; the old stable receives protection for a year. The testing security staff assists, but stability gets changes slower than testing. The protection of Unstable is up to the program maintainers.
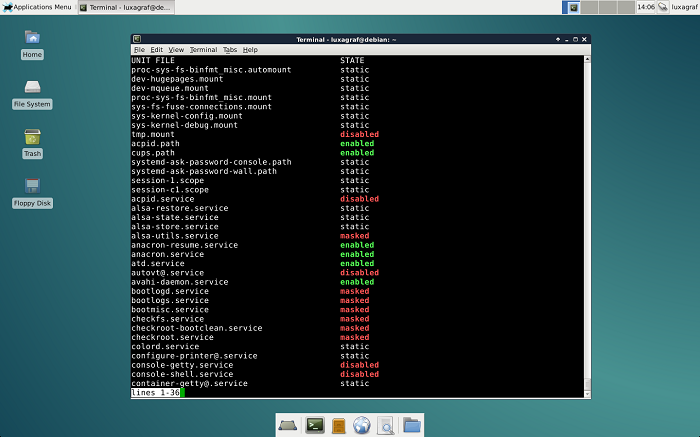
The Debian group provides manual and automated methods for hardening a Debian installation through literature and tools. Since Buster, support for AppArmor is accessible and activated by default. Debian also offers an optional hardening wrapper.
A Debian worker found that only 32,767 unique keys could be produced by the OpenSSL package included with Debian and its derivatives, including Ubuntu, in May 2008. This made several security keys susceptible to a random number generator exploit. The entire resolve process was time-consuming because it required regenerating all impacted keys and certificates because simply fixing the security vulnerability was not enough.
Value
One approach based on the COCOMO model has assessed the cost of creating all of the packages included in Debian 5.0 Lenny (323 million lines of code) to be around US$8 billion. In 2016, Black Duck Open Hub calculated that using an alternative approach based on the same model would cost about US$1.4 billion to build the existing codebase (74 million lines of code).