What is Message-passing Technique in OS
Introduction
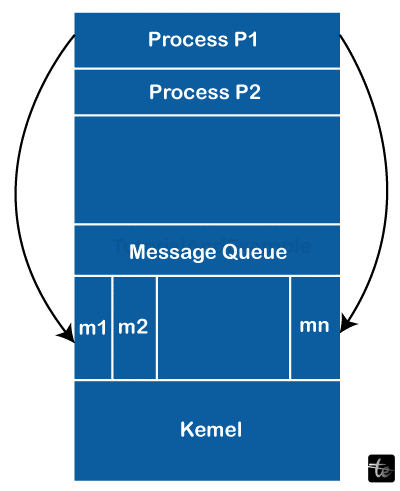
In operating systems, message passing is a communication method where processes share data via messages. By enabling programs to send and receive data independently, it makes inter-process communication easier. Different kinds of data, including commands, signals, and data payloads, can be contained in messages. This method improves distributed systems' modularity and scalability and makes it possible for separate processes to work together without interruption. In an operating system environment, message passing—which can be synchronous or asynchronous—is essential for developing stable, concurrent applications.
The following are the main points of message passing:
- Within message-passing systems, messages are sent and received over a communication channel between processes. How, therefore, should the agreement be made?
- Some topology systems define the pattern of the connection given by the channel.
- A network is the grouping of the channels.
- According to their definition, distributed systems are made up of a geographically dispersed group of computers. Thus, a direct connection between a computer and another node is not conceivable.
- Therefore, in the Message-Passing Model, every channel is private.
- What information must be sent via the network is determined by the sender. A phone call is one instance.
- Only once the destination worker chooses to receive the data is the data truly conveyed. For instance, when someone answers your phone and begins to respond.
- Time is not a barrier. It is in the hands of the person who answers your call after how many rings. He can keep you waiting forever by not returning your call.
- Both parties must actively participate in network communication for it to be successful.
The algorithm
- Let us examine a network made up of n bidirectional point-to-point channels called p0, p1, p2,... pn-1.
- Node and may be Node unaware of who's at the other end. Thus, the topology would be set up in this manner.
- Only the processes know from where the message needs to be sent once communication has been established and message transmission starts.
Characteristics
The following are the features of the message-forwarding model:
- Message forwarding is mostly used for communication.
- It is utilized in distributed contexts when communication activities are located on distant computers connected by a network.
- Since the message-passing feature offers a means of communication and action synchronization between the communicating processes, no code is needed in this instance.
- Because message passing is implemented via kernel (system calls), it takes a long time to complete.
- It is helpful for sharing modest amounts of data to avoid disagreements.
- Comparing message passing to shared memory technique, communication is slower.
The benefits of the Message Passing Model
- Very understanding of extended communication lags.
- Easier to construct devices with tremendous parallelism.
- It can tolerate longer communication latencies better.
- Message-passing libraries offer superior performance and speed.
Disadvantages of the Message Passing Model
- A programmer must perform all tasks.
- It is slower since it takes longer to establish a connection.
- Cooperative operations are typically needed for data transfer, which can be challenging to do.
- Programmers find it challenging to create portable applications using this paradigm because most message-passing implementations consist of an embedded source code library of subroutines. Once more, the programmer is obliged to handle everything in\dependently.
Conclusion
By providing a useful and flexible means for processes to interact with one another, operating systems use message passing to increase system concurrency and flexibility. Owing to its asynchronous structure, robust and distributed computing environments with enhanced scalability and responsiveness may be created.