Back Trace in C
The series of function calls that brought the program to its current executing point is known as a backtrace in C. It is a method for tracing the execution path backward, beginning at a particular location in the source code and continuing through the calls to functions that brought the code to that location.
In debugging, backtraces are frequently used to determine the events that resulted in a problem or unanticipated action in software. When a problem arises, developers can identify the root cause and comprehend the execution flow by looking at the backtrace.
The <execinfo.h> header in C has several methods to record and print backtraces. The two primary roles in question are:
Backtrace Method:
- The return address of the function calls are stored in an array by this function, which also records the current call stack.
- It accepts as parameters an array of void* and the array's size.
backtrace_symbols Use:
- This function creates an array of strings representing each function or address on the call stack from an assortment of void pointers it received from the backtrace.
- A reference to a collection of strings is returned.
Example Code:
#include <stdio.h>
#include <execinfo.h>
#include <stdlib.h>
void the_function() {
void* callstack[128];
int frame = backtrace(callstack, 128);
char** symbols = backtrace_symbols(callstack, frame);
if (symbols == NULL) {
perror("backtrace_symbols");
exit(EXIT_FAILURE);
}
for (int i = 0; i < frame; ++i) {
printf("%s\n", symbols[i]);
}
free(symbols);
}
int main() {
the_function();
return 0;
}
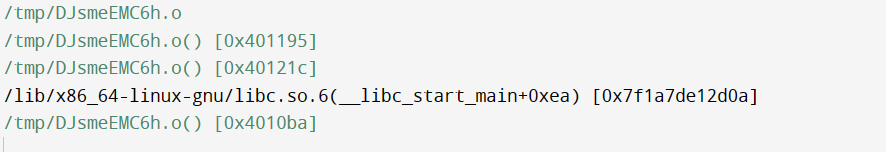
Output:
Key points of backtrace in C
- Definition:
In C, a backtrace is a series of calls to functions that give details on the path taken by the program's execution to reach a certain location.
- Debugging Instrument:
When debugging a program, backtraces are frequently utilized to determine the precise order of calls to functions that resulted in failures or unexpected behaviour.
- Header File:
C has functions for recording and deciphering backtraces in its header file.
- Using libexecinfo for linking:
It is often required to link to the libexecinfo library when using backtrace functions.
constraints on the backtrace in C
- Absence of Symbol Information:
Symbol identifiers for all locations in the call stack might not be included in the information returned by backtrace_symbols, particularly if the application has been optimized or debug indicators are unavailable.
- Inlining and Optimizations:
Some compiler adjustments, like function inlining, can result in an incomplete or less meaningful backtrace. The backtrace might not show different instances of inserted functions.
- Removed Binary Options:
Removing symbols from the binaries for releasing builds may cause the backtrace to contain little or no symbol information. Executables that are ready for production often have this.
- Generating Dynamic Code:
Just-In-Time (JIT) compiled or dynamically produced code occasionally may not be adequately represented in the backtrace.
- Handlers of Signals:
The status of the signal's processing code, rather than the program's execution path, may impact the backtrace while a signal controller is active.
- Platform-Related Differences:
Multiple platforms and operating systems may exhibit differences in the behavior and data returned by backtrace functions.
- Implications for Security:
Backtraces are helpful for debugging, but releasing implementation details in an operational environment could put users' security at risk.
- Insufficient Contextual Data:
Although they don't fully record the program state, backtraces offer details about the call stack. It might be essential to use additional debugging methods or tools to obtain a full picture of the behaviour of the software.
- Intricate Control Flow:
When dealing with extremely complicated control flows or concurrency, analyzing the backtrace alone may be insufficient.
applications of backtrace in C
- Troubleshooting System Failures:
Getting a backtrace of a program crash can be useful in determining the precise order of calls to functions that caused the crash. This data is essential for identifying the problem's underlying cause.
- Error Analysis:
Backtraces are useful for examining unexpected behaviour and mistakes in software. Developers can learn more about how the program got into trouble by looking at the call stack.
- Corrupt Memory:
When corruption of memory or fragmentation errors occurs, a backtrace can reveal which function calls resulted in the memory-related problem.
- Unresolved Exclusivity:
A backtrace can help identify the sequence of events that led to an unhandled exception and help determine the cause of the issue
- Analyzing performance and creating profiles:
looking at the function call hierarchy, backtraces can be utilized for profiling and performance analysis, which aids developers in understanding the performance features of their code.
- Finding Leaks in Resources:
Memory leaks and other resource leaks can be found via backtraces. Developers can monitor the distribution and disposal of hardware and software by looking at the call stack.
- Diagnostics and Logging:
When certain events or problems occur during the execution of a program, developers can generate comprehensive diagnostics logs by integrating backtraces into logging systems.
- Quality Control and Testing:
Backtraces are useful for tracing events that result in failures in development and quality management procedures. Developers can use this information to replicate and resolve issues that have been reported.
- Analysis of Dynamic Code:
Analyze the code execution dynamically by looking at the function's call stack.
Recognize how the software behaves and flows under control in various situations.
- Analyzing the Root Cause:
Use backtrace information to find the core cause of unusual behaviours or breakdowns in complex systems.
Determine the source of problems and comprehend how various elements interact.
- Automated Examination:
Automated test framework should incorporate backtrace data to enable troubleshooting if tests fail.
Enhance unit tests' capacity for diagnosis.
- Managing Exceptions:
Record backtrace data to help identify the exception's cause when handling exceptions.
Enhance notifications of errors by adding call stack context.
- Automation of tests and unit testing:
When using test automation frameworks, incorporate backtrace data to improve debugging abilities.
Example 1: Simple Backtrace#include <stdio.h>
#include <execinfo.h>
#include <stdlib.h>
void print_backtrace() {
void *buffer[10];
int nptrs = backtrace(buffer, 10);
char **strings = backtrace_symbols(buffer, nptrs);
if (strings == NULL) {
perror("backtrace_symbols");
exit(EXIT_FAILURE);
}
printf("Backtrace:\n");
for (int i = 0; i < nptrs; i++) {
printf("%s\n", strings[i]);
}
free(strings);
}
void func4() {
print_backtrace();
}
void func3() {
func4();
}
void func2() {
func3();
}
int main() {
func2();
return 0;
}
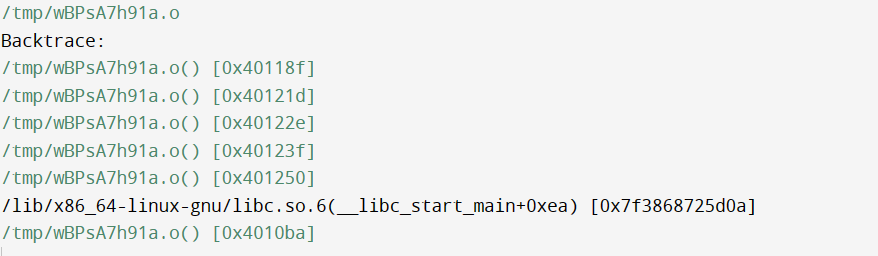
Output:
Example 2: Signal handling in a backtrace
#include <stdio.h>
#include <execinfo.h>
#include <signal.h>
#include <stdlib.h>
void print_backtrace() {
void *buffer[10];
int nptrs = backtrace(buffer, 10);
char **strings = backtrace_symbols(buffer, nptrs);
if (strings == NULL) {
perror("backtrace_symbols");
exit(EXIT_FAILURE);
}
printf("Backtrace:\n");
for (int i = 0; i < nptrs; i++) {
printf("%s\n", strings[i]);
}
free(strings);
}
void signal_handler(int signum) {
printf("Signal %d received.\n", signum);
print_backtrace();
exit(signum);
}
void func6() {
int *ptr = NULL;
*ptr = 42;
}
void func5() {
func6();
}
void func4() {
func5();
}
int main() {
signal(SIGSEGV, signal_handler);
func4();
return 0;
}
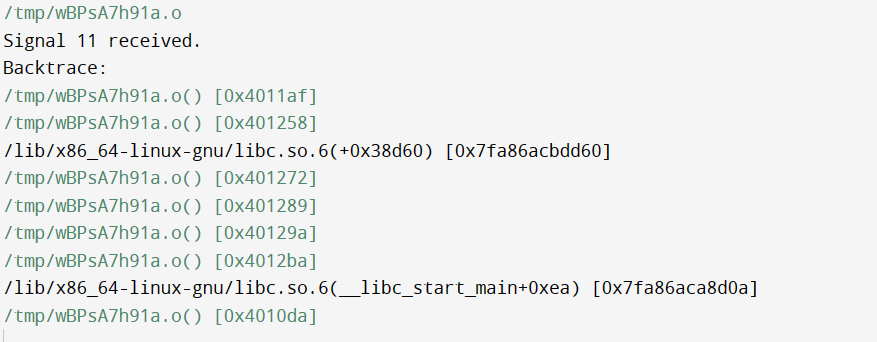
Output:
Real-time C backtrace applications
- Embedded System Fault Diagnosis:
In integrated real-time systems, rapidly identifying the core cause of unanticipated failures (such as crashes or exceptions) can be achieved by recording a backtrace.
- Industrial Control Systems:
To ensure prompt response and resolution, backtrace information can be utilized in industrial control systems to determine the events that resulted in a system failure or aberrant behaviour.
- Automotive Software Development:
Backtrace can help ensure the dependability of software components in the automotive sector by aiding in diagnosing and debugging problems in live embedded systems utilized in automobiles.
- Aerospace Systems:
In aerospace applications, backtracing is useful for comprehending the call stack in crucial situations and locating and resolving avionic software bugs.
- Medical equipment:
Backtrace can be utilized to create immediate software for healthcare devices to diagnose mistakes and unanticipated actions to ensure the safety and dependability of the equipment.
- Links and Telecommunications:
Backtrace data can be captured in real-time networking applications to help diagnose problems with packet processes, protocol dealing with, and network stack interactions.
- Systems of Finance:
High dependability is frequently required for real-time financial systems. Backtrace helps ensure the reliability of financial systems by aiding in the diagnosis of transaction processing problems.
- Automation and Robotics:
In real-time automation and robotic systems, backtrace can troubleshoot control software and find problems with motion organizing, sensor integration, and other important parts.
- Systems of Power and Energy:
Backtracing is useful in real-time power and energy systems for fault diagnosis to ensure the dependable and secure operation of systems like smart grids.
- Essential Infrastructure:
In applications that operate in real-time and are a vital component of infrastructure, such as power vegetation, water treatment plants, and transportation networks, backtrace can be extremely important.
- Switching Systems for Telecommunication:
Backtracing unexpected occurrences in telecoms switching systems can help diagnose problems with call handling and connection to the network.
- Dispersed Structures:
In distributed real-time systems, the backtrace capability can be useful for tracking the execution process across several nodes and troubleshooting communication and synchronization problems.