What are the Types of IPv4 Addresses
An Internet Protocol (IP) address is a special address that serves as the device's network identification. It resembles a set of guidelines controlling the data format transferred via the local Network or the Internet. Using an IP address, the Internet can differentiate among various routers, laptops and webpages. It facilitates better visual interaction between the source and the destination and acts as a distinctive device identification within a particular network.
IP address structure: An IP address is represented by four numbers; an example of a normal address maybe 192.168.1.38. The set's numbers may be in the range of 0 and 255. 0.0.0.0 to 255.255.255.255 is the whole range of IP addresses as a result.
An IP address is made up of two parts: X1. X2. X3. X4
1. [X1. X2. X3.] is the Network ID
2. [X4] is the host ID.
1. Network ID: This portion of an IP address (Internet Protocol) on the left denotes the Network of the device to which it is connected. If the device's IP address is 192.168.1.32 on a standard home network, the network ID is the 192.168.1 part of the IP address. 192.168.1.0 is the web server ID the gadget is connected to, based on the fact that providing a number without a zero is normal.
2. Hosting ID: The portion of an Internet Protocol (IP) address that the Network's connection ID failed to collect identifies a particular device within that system, known as a "host" in the TCP/IP world. With an IP address like 192.168.1.32 as a guide, the host identification 32 will be the only host ID on the 192.168.1.0 connection
The version of IP address:
IPV4 (Internet Protocol Version 4) is the name given to the original version of the Internet Protocol address. IPV4 addresses are made up of 32 bits. Internet Protocol Security (IPSec) concerning network security is required in this scenario. There are still a lot of physical addresses despite the 4,294,967,296 discussions since the quantity of real and virtual devices in use is increasing rapidly.
IPV6 (Internet Protocol Version 6) is the most recent version of a web page address. A 128-bit address is used in IPV6. Internet Protocol Security (IPSec) must be used to ensure network security.
Types of IPV4 Addresses
With 3.4 x 10^38 private IP addresses permitted, it seems adequate to serve the trillions of internet-connected devices that are already in use and will be added.
- Unicast
It is meant for a single network connection on a specific subnet and permits interaction among persons. This address is globally unique for the sole purpose of recognizing the device on an internet connection. Subnet prefix: An IP single-cast address's network prefix is a network identification or networking address. It is important to remember that every node on the matching physical or logical subnet needs to support an identical subnet prefix, which eventually becomes unique across the whole TCP/IP network.
Host ID: An IP single-cast name's host address portion. It can recognize an internet node that certain machines are connected to.
- Multicast
It applies to one or more interfaces for the Network spread across several subnets. It permits interaction from one to many. It sends discrete packets to many different places from a single source. The Class D address design incorporates those addresses.
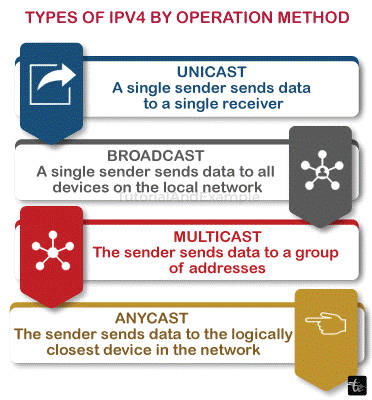
- Broadcast
It serves one-to-one communications within a subnet and is given to all the network interfaces. It transports packets across the subnet's ports from a single source. Network broadcast, subnet airing, all networks directed broadcast, and definitive broadcast are the different types of broadcast addresses. There are various classes into which internet addresses are divided. It is determined by dividing the total amount of bits used by the host ID and an address prefix of a single subnet. As a result, it can approve the number of networks and hosts in each Network.
The following are the five address classes:
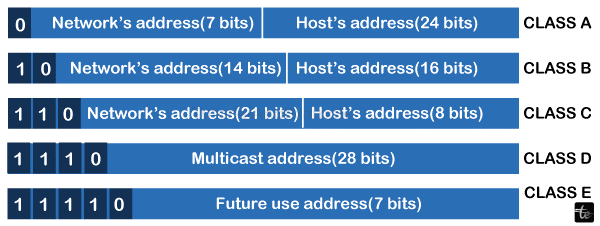
- Class A: As indicated in the following Table, it employs an 8-bit network number, the first bit always being zero. For IP unicast addresses only, it is reserved. The host class is used when a network has an abundance of hosts. It defines prefix length with a single octet. The Network contains 28 or 128 digits that it can support.
- Class B: It allows a network and hosting address to have 16 bits each. The initial two bits are always 10. From IP unicast addresses, it is far away. Two octets are used for a particular network, and the final two are used for host IDs. Large to medium-sized networks are their primary applications. Up to 65,536 hosts can be accommodated in 16,384 networks using Class B addresses.
- Class C: For IP unicast addresses, it is far away. They fit the definition of tiny networks. The final octet contains host IDs; the first three identify a particular network. Up to 2,097,152 networks containing up to 254 hosts each can use the Class C addresses. The initial three bits are always set to 110.
- Class D: Broadcasting Internet Protocol (IP) addresses are defined by it.
- Class E: For practical reasons, these addresses were set aside.
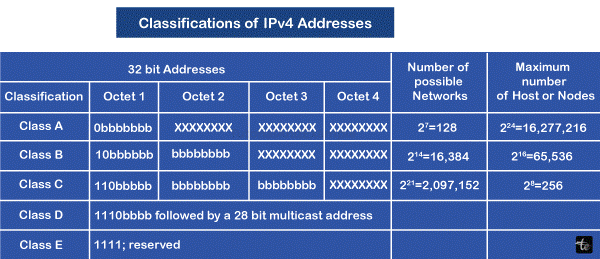
The categorization of addresses using IPv4 is shown in the Table.
IP Address Types
Public, private, fixed, and dynamic are the four categories of IP addresses. Their local network location determines their private and public addresses, which should be utilized inside the Network's boundaries and accessible outside of it.
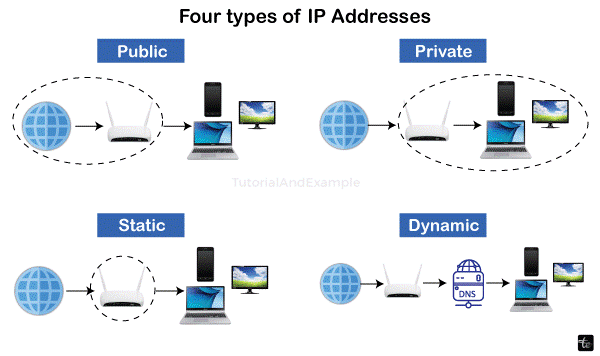
- Public IP address:
An IP address that is encrypted by different servers and devices is known as an IP address that is publicly accessible. At that point, you link these gadgets to your internet connection. Some even refer to this IP address as their external one. An IP address that can be accessible over the World Wide Web is known as a public IP address. The public Internet Protocol (IP) address is a unique worldwide address assigned to a computer device, similar to the postal address used for mail delivery to your residence. The servers that will enter the public IP address are the web server, email server, and any other server device with direct access to the Network. Only one device is provided with Internet Address Protocol, which is distinct across the globe.
- Private IP address:
This includes PCs, iPhones, iPads, and Bluetooth-capable gadgets like smart televisions, printers, and speakers. Your home will likely have more private Internet Protocol (IP) addresses as the Internet of Things expands. These items must be uniquely identifiable to your router; most devices require mutual authentication. As a result, each device that divides the Network is given a distinctive private IP address that your router generates.
- Static IP Address:
A static IP address is not valid. On the other hand, the Dynamic Host Configuration Protocol (DHCP) server will supply a dynamic IP object to change. Although not dynamic, the Static IP address can be modified as part of routine network administration. Static IP addresses are unchangeable; once given, they never change over time. Additionally, this kind of IP aids in providing you with additional device details.
- Dynamic IP address:
A dynamic IP address is always changing. A dynamic IP address is not constantly the same and varies periodically. You might have a strong IP address if you receive cable and DSL service. Since dynamic IP addresses are too costly, Net service providers give them to their clients. Your IP address is given to you directly from the address pool rather than as a fixed address. A new number is assigned to the previous number, and it is returned to the lake after some weeks, days, or occasionally months. ISPs rarely give customers who reside there a static IP address; if they do, the cost is typically higher. Although dynamic IP addresses are inconvenient, you can access them for free and with ease if you have the correct equipment.