Switching Techniques
Introduction
There may be more than one path connecting the sender and the recipient in big networks. The optimal path for data transmission will be determined by the switching strategy.
Systems are connected via switching mechanism to provide one-to-one communication.
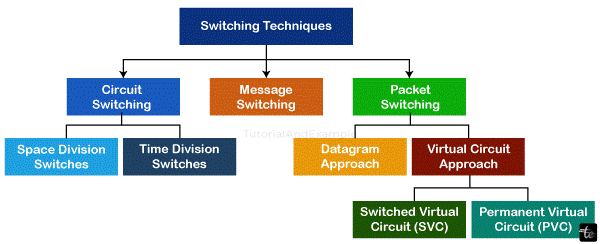
Categorization of Switching Methods:
1. Circuit Switching
A dedicated path between the sender and the recipient is established by the switching technique known as circuit switching.
With the Circuit Switching Technique, the dedicated path will stay in place until the link is broken once it has been established.
In a network, circuit switching functions similarly to how a phone does.
Before any communication may occur, the entire path must be present.
When using the circuit switching technique, a request signal is sent to the recipient whenever a user wishes to transfer data, voice, or video. The recipient then responds with an acknowledgment to confirm that the dedicated way is available. The data is transferred via a dedicated path upon acknowledgment.
In public telephone networks, circuit switching is utilized. It is employed for voice communication.
Circuit switching technique allows for the transport of fixed data one bit at a time.
There are three stages to circuit switching communication:
- Circuit configuration
- Data transmission
- Disconnect Circuit
Circuit switching utilizes two technologies:
- Space Division Switches:
Space Division Switching is a circuit switching technology where a physically distinct collection of crosspoints is used in a switch to accomplish a single transmission line.
Crossbar switches can be used to implement space division switching. A control unit can enable or disable a crossbar switch, which is a semiconductor gate or metallic crosspoint.
Semiconductors are used in the construction of the Crossbar switch. Consider the FPGA-based Xilinx crossbar switch.
Space Division Switching features nonblocking switches, great capacity, and fast speed.
There are two types of Space Division Switches:
Crossbar Switch: A switch with n input lines and n output lines is called a Crossbar switch. There are n2 crosspoints—intersection points—in the crossbar switch.
Drawbacks of the Crossbar switch:
As the number of stations rises, so does the number of crosspoints. Thus, for a huge transition, it becomes very expensive. Using a multistage switch is the answer to this problem.
- Multistage Switch:
The crossbar switch is divided into smaller components and then connected to create a multistage switch.
There are fewer crosspoints as a result.
There will always be another route available in case the first one fails.
Advantages of Circuit Switching:
- The communication channel is set aside for the Circuit Switching method.
- Its bandwidth is fixed.
Drawbacks of Circuit Switching:
- The pace of data transmission is the only thing that delays once the dedicated connection is established.
- The connection establishment process takes a lengthy time—roughly 10 seconds—during which no data may be sent.
- Since each link needs its own path, it is more expensive than other switching methods.
- It is inefficient to use since the path's capacity is squandered as soon as it is created and no data is conveyed.
- Even though the channel is free in this instance, no further data may be exchanged because the connection is devoted.
- Message Switching
A message is sent as a whole unit and routed through intermediary nodes where it is stored and transmitted. This switching approach is known as message switching.
There is no dedicated path established between the sender and the recipient when using the message switching mechanism.
The message's destination address is attached. Because the message is routed through the intermediary nodes according to the information included in the message, message switching offers dynamic routing.
The most effective routes are provided by message switches because of the way they are programmed.
Every node saves the complete message before forwarding it to the subsequent node. The term "store and forward network" refers to this kind of network.
Switching between messages considers each one as a separate message.
Benefits of Message Switching:
- Devices that communicate with each other exchange data channels, which increases the effectiveness of utilizing available bandwidth.
- It is possible to change the message size that is sent over the network. As a result, it can handle data of any magnitude.
- The network can be controlled by message priority.
- Due to the message being briefly stored in the nodes, traffic congestion can be decreased.
Drawbacks of Message Switching:
Enough storage must be included in the message switching so that they can hold messages until they are forwarded.
The message switching technique's ability to store and transfer data may be the cause of the long delay.
- Packet Switching
A switching approach called packet switching sends the message all at once, but breaks it up into smaller parts that are transmitted separately.
The message breaks up into smaller units called packets, and at the receiving end, each packet is assigned a unique number that allows it to be sorted in sequence.
The headers of every packet include information such as the sequence number, source address, and destination address.
Across the network, packets will move in the quickest direction.
At the receiving end, every package is put back together in the right order.
The message will be transmitted again if there are any missing or corrupted packets.
The acknowledgment message is delivered if the packets are received in the correct order.
Methods Used in Packet Switching:
Two methods exist for packet switching:
- Datagram packet switching:
This technology uses packets, known as datagrams, each of which is regarded as a separate entity. Every packet includes destination information, which the switch uses to route the packet to the intended recipient.
At the receiving end, the packets are put back together in the right order.
The path is not fixed when using the Datagram Packet Switching approach.
To forward the packets, intermediate nodes make the routing decisions.
Another name for Datagram Packet Switching is connectionless switching.
- Virtual Circuit Switching:
Another name for virtual circuit switching is connection-oriented switching.
When using virtual circuit switching, communications are sent down a prearranged path first.
The connection between the sender and the recipient is established through the usage of call request and call accept packets.
In this instance, the path remains fixed while a logical link is in place.
Benefits of Packet Switching:
- Expense-effective: A certain amount of expense is reduced when using the packet switching technique since switching devices do not need a large amount of secondary storage to hold the packets. As a result, we may declare that the packet switching method is economical.
- Reliable: Packets can be diverted if a node is busy. This guarantees dependable communication through the use of the Packet Switching technology.
- Effective: The technology of packet switching is effective. It makes excellent use of the available bandwidth because it doesn't require any pre-established paths and allows multiple users to use the same communication channel at once.
Drawbacks of Packet Switching:
- It is necessary to retransmit lost packets if the network is damaged or overcrowded
- Applications that demand high-quality, low-latency services cannot be implemented using the packet switching technique.
- If mistakes are not fixed, it may also result in the loss of important data.
- A packet switching technique uses extremely sophisticated protocols that are expensive to implement.
Conclusion
Through analyzing various strategies like circuit switching, packet switching, and message exchanging, it's obvious that every method offers particular benefits and disadvantages.
Circuit switching lays out a correspondence way among source and collector, guaranteeing low idleness and reliable data transmission. In any case, it's less adaptable and less effective in using network assets contrasted with bundle exchanging. On the other hand, packet switching allows for better resource utilization and scalability by splitting data into smaller packets. It works well in taking care of explosions of information yet may experience packets misfortune.
Message switching, albeit more uncommon today, includes sending the whole message all in all. It's more straightforward yet experiences longer transmission times and higher possibilities of mistakes. Utilizing the strengths of each, combining these methods or implementing hybrid models frequently improves network performance.
At last, the selection of switching strategy relies upon factors like information volume, traffic designs, and required speed.