What are the elements of the Transport Protocol
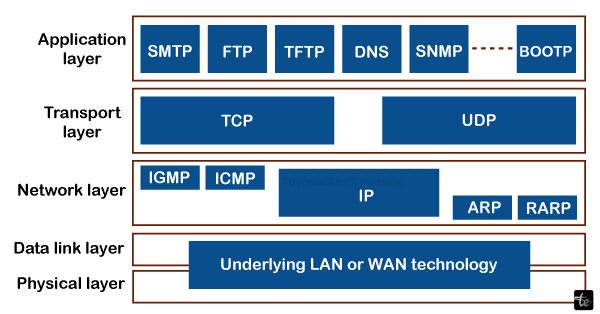
The transport layer is the subsequent layer in the TCP/IP model and the fifth layer in the OSI model. The transportation layer provides reliable delivery of services and an end-to-end link between the point of origin and the final destination. Therefore, the transport layer is called the end-to-end layer. The network layer receives services from the application layer, which is the layer above it, through the transport layer. The data encapsulation component at the transport layer is called a section.
The Transport Layer
- Processing Functions for Processing Delivery
- Device connectivity from end to end
- Using and Removing Multiplexes
- Data is reliable and accurate.
- Management of Congestion
- Regulation of Flow
- Protocols at the Transport Layer
The TCP and UDP protocols primarily represent the transport layer. Nowadays, practically all operating systems enable setups with many processors and users. This protocol at the transport layer makes links to the various ports possible. We refer to these ports as protocol ports. Data packets are sent from IP servers to destination ports and from the source port to target IP services by the transport stage protocols, which operate atop IP protocols. The specifications for the transport layer are listed below.
Transmission Control Protocol
One of the core technologies of the World Wide Web's standard suite is the transmission control protocol (TCP). It started as a supplement to the World Wide Web Protocol (IP) in the first network setup. As a result, TCP/IP refers to the full suite. Thanks to TCP, programs on servers interacting via an IP network can send a continuous stream of octets (bytes) with consistency, order, and error-checking. TCP, a component of the Transport Layer (TL) of the TCP/IP suite, is essential to many mainstream internet services, including email, file transfers, remote management, and the web as a whole. TCP is frequently used to power SSL/TLS.
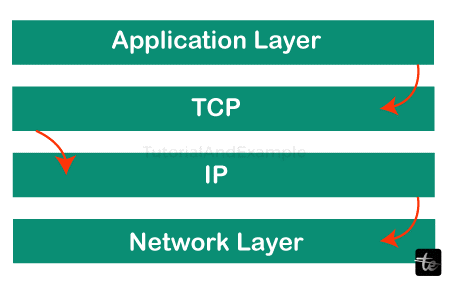
On top of IP, a protocol for transport called Transfer Control Protocol (TCP) is employed to guarantee dependable packet transfer.
Numerous issues related to packet-based communication, such as misdirected, out-of-order, duplicate, and malformed packets, can be resolved via TCP's built-in procedures.
The Internet standard stack can also be called TCP/IP since TCP is the protocol most frequently used on top of IP.
The TCP/IP approach splits the data into little bundles and then reconstructs each into the initial communication on the other end to ensure that every message reaches its destination undamaged. Rather than delivering anything at once, it is easier to retain efficiency when the data is sent in little packages.
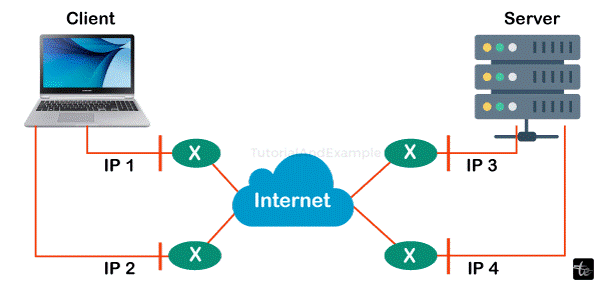
Once a message has been divided into packages, if one route is congested, but the final location is still the same, each bundle may take various paths.
Working of TCP
The communication is being dismantled at its last location and then put back together in a completely new way.
For instance, a web server analyses an inquiry for a page on the internet from a user anywhere in the globe, analyses it, and returns an HTML page to the user. The HTTP Protocol is a protocol that the server uses. Subsequently, the HTTP requests that the TCP layer establish the necessary connections and transmit the HTML file.
The information is now divided into smaller messages by TCP and sent to the Internet Protocol (IP) layer. After that, packets are delivered to their recipient via several paths.
The computer's system's TCP layer waits for the transmission to complete before acknowledging when each data packet has been delivered.
TCP/IP characteristics
A few of Transmission Control Protocol's most notable characteristics are
1. System of Segment Numbering
TCP assigns numbers to every segment to track which details are being sent or retrieved.
Data bytes that need to be sent are given a specific byte number, and segments are given sequence numbers.
Received sections are given Acknowledgment Numbers.
2. Focused on connections
It denotes that the sender and recipient will remain in communication until the process is finished.
The data is kept in its original order before and after transfer.
3. Complete Duplex
Data can be transferred simultaneously over TCP form the person who sends it to the recipient or the other way around
It improves the sender-receiver data flow's efficiency.
4. Control of Flow
The speed at which a sender delivers data is constrained by flow control. To guarantee dependable delivery, this must be done.
The amount of information that may be collected is continuously hinted at by the receiver to the sender (using a sliding window).
5. Error Control
TCP uses an error-control system to provide reliable information transfer.
Error control is focused on bytes.
Sections are examined to look for mistakes.
Error control encompasses the following: duplicated segments, out-of-order segments, damaged and lost section leadership, etc.
6. Traffic Control
The amount of internet delay is taken into consideration by TCP.
A sender's data volume determines the extent of congestion.
Advantages
- It is a trustworthy procedure.
- It offers both recovery capabilities and an error-checking mechanism.
- It provides control over the flow.
- It guarantees that the information is received at the correct location in the precise delivery sequence.
- Open Protocol is not a property of any company or person.
- Each machine on a network is given an IP address, and every location is given a domain name, enabling gadget site differentiation across the entire network.
Disadvantages
- Since TCP was designed for wide-area networks, tiny systems with little bandwidth may find it problematic due to its size.
- TCP can reduce the speed of networks since it operates across multiple layers.
- Its makeup is not generic. Thus, it is unable to convey any stack of protocol.
2 User Datagram Protocol (UDP)
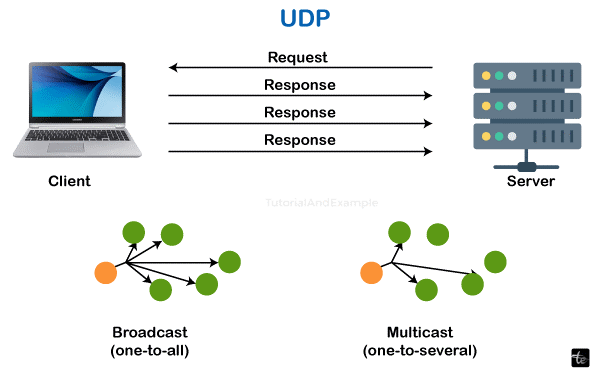
One Transport Layer protocol is called User Datagram Protocol (UDP). The Internet Protocols suite, sometimes called the UDP/IP suite, includes UDP. It is an unstable, connectionless protocol in contrast to TCP. Therefore, establishing a connection before beginning data transfer is not necessary. Low-latency and loss-tolerant connections are found over the network with the aid of UDP. Process-to-process interaction is made possible using UDP.
While Transmission Control Protocol (TCP) is the predominant protocol for the transport layer utilised by most web services, it comes at an expense in terms of extra overhead and delay. TCP guarantees speed and dependability, among other benefits. UDP enters the scene at this point. UDP is required for immediate applications like phone or video communication, live conferencing, and online gaming. Since superior performance is needed, Rather than analysing delayed packets, UDP allows packets to be dropped. Because UDP lacks error checking, it also uses a smaller bandwidth.
User Datagram Protocol (UDP) is both bandwidth and latency economical.
Working of UDP
A standardised communication protocol called user datagram protocol sends data between computers connected to a network. Nevertheless, UDP streamlines data transport by transmitting packets—or, more precisely, datagrams—directly to the recipient without requiring a two-way connection, unlike other systems like TCP. UDP acknowledges neither the sending of the order nor the arrival of messages.
Checksums and numbers of ports are two elements of UDP that help define the role that the data being transmitted plays and guarantee data integrity. Nevertheless, it doesn't call for a "handshake" between the sender and the recipient before the start of data transmission.
Because of this, sending private information over UDP is not the best choice because the recipient might receive data that is messy, broken, or contains blank spaces.
Advantages
- Data transfer via multiplex and broadcasting is also possible with UDP.
- More often than not, the UDP protocol is used for quick operations like DNS lookups.
- Since it is a connectionless protocol, focusing on the connections network is not required.
- Message transport using UDP is quick.
Disadvantages
- The delivery of a message is not guaranteed while using the Universal Data Protocol, or UDP, protocol.
- Packet loss is worse for UDP technology.
- There is no congestion control mechanism in the UDP system.
- The data cannot be transmitted sequentially using the UDP method.
3. SCTP
Stream Control Transmission Protocol is referred to as SCTP. The protocol SCTP is connection-oriented. Data is transmitted in full duplex mode from source to recipient via Stream Control Transport Protocol. A connection between hosts can be established using the unicast SCTP protocol, which employs many hosts to reach the target. Creating an association across a wireless network network is easier using the SCTP protocol. The transfer of data is dependable while using the SCTP technique. Over the World Wide Web, SCTP offers a reliable and more straightforward phone conversation. The SCTP protocol does not rely on the IP layer and offers multihoming, which can create many connection paths between two points of contact. The SCTP protocol prevents half-open relationships, which further enhances security.
Advantages
- SCTP offers a link that operates in full duplex. Information can be sent and received simultaneously by it.
- The TCP and UDP protocols' characteristics are present in the SCTP protocol.
- The IP layer is independent of the SCTP protocol.
- The secured communication is SCTP.
Disadvantages
- The apps must be adjusted appropriately to handle many streams concurrently.
- The node's transportation stack needs to be modified for the SCTP protocol.
- Programmes must be modified if SCTP is utilised in place of TCP or UDP protocol.