Aloha
Aloha
Norman Abramson and his colleagues were developed aloha at the University of Hawaii in the 1970s. ALOHA is a Multiple Access Protocol which is used for random access in the network. Aloha was designed for the wireless local area network (WLAN), which is also known as the radio broadcast. If more than one user transmits the data at the same time, then that data has a collision, and that data destroy.
Type of Aloha
Aloha has been divided into two types.
- Pure Aloha
- Slotted Aloha
Pure Aloha
Pure Aloha is also called the original aloha protocol. It's a simple but elegant protocol, i.e., whenever the system has a data frame to send, it transmits the data frame continuously. Due to which the risk of collision is very high in this aloha method. Shown in below pure aloha.
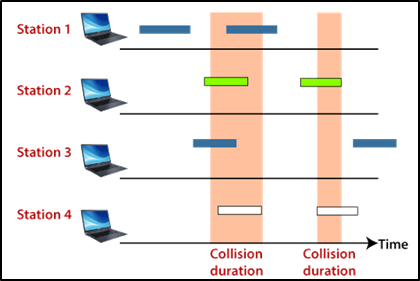
Therefore, the acknowledgment method is used to know the status of the data frame sent in the network. If the receiver doesn't provide any acknowledgment, it is understood that frames have been destroyed, and frames are re-transmitted.
- The maximum throughput occurs at G = 1/2, which is 18.4%.
- In Pure Aloha, the probability of successful transmission of the data frame is S= G* e^-2G
- In Pure Aloha, vulnerable time is: 2 * Tfr
NOTE: Pure Aloha is overall efficiency is very less due to a large number of collisions.
Example: An Aloha network uses an 18.2 kbps channel for sending message packets of 100 bits long size. Calculate the maximum throughput.
In Pure Aloha, Efficiency = 18.4%
Usable bandwidth for 18.2 kbps = 18.2 * 0.18 = 3.276 kbps
Therefore, the maximum throughput of Pure Aloha
= 1/2e * 3.276
= (18.4 * 3.276) / 100
= 0.6027
Slotted Aloha
Slotted aloha was developed to increase the performance of the pure aloha, as there are very high chances of collision in pure aloha. In this Aloha, the time of the systems is divided into slots so that the system can send only one frame to a slot, and this frame can only be sent at the beginning of the slot. If a system cannot send a frame at the beginning of the slot, then it has to wait for the next slot to start. If two systems try to transmit the frame at the beginning of a time slot. But it is better than pure Aloha because it has less chance of collision. Shown in below slotted aloha.
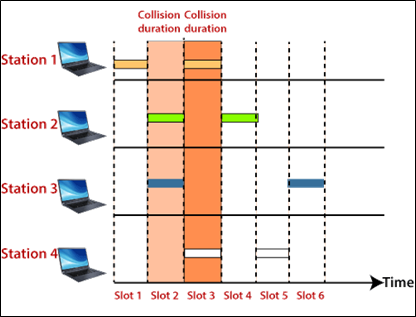
- In Slotted Aloha, maximum throughput occurs at G = 1, which is 37%.
- In Slotted Aloha, the probability of successful transmission of the data frame:
S= G* e^-G
- In Slotted Aloha, vulnerable time is: Tfr
Difference between Pure Aloha and Slotted Aloha?
| Pure Aloha | Slotted Aloha |
| In Pure Aloha, at any time can be sent the data in any station. | In Slotted Aloha, each station can send the data at the provided time slot. |
| The time is not globally synchronized in this aloha. | The time is globally synchronized in this aloha. |
| Continuous time | Discrete time |
| In Pure Aloha, vulnerable time is: = 2 * Tfr | In Slotted Aloha, vulnerable time is: = Tfr |
| The maximum throughput occurs at G = 1/2 which is 18.4%. | The maximum throughput occurs at G = 1 which is 37%. |
| Pure Aloha does not reduce to half the number of collisions. | Slotted Aloha reduces collision numbers to half, therefore doubles the efficiency. |