IMAP4 (Internet Message Access Protocol)
Introduction
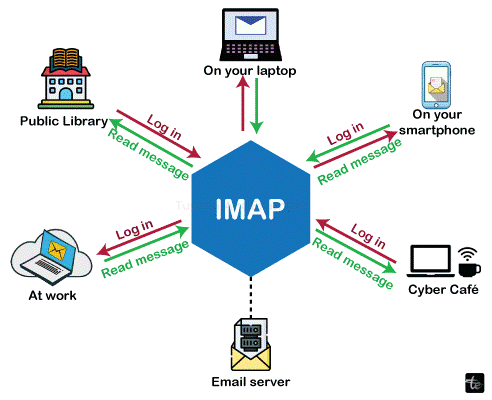
IMAP stands for Internet Message Access Protocol. It is an inbound email protocol. Email messages are saved on a mail server and can be seen and edited by the receiver just like if they were locally stored on their device or devices. With IMAP, users can preserve draft messages on the server, flag messages for follow-up or urgency, and organize communications into folders. Additionally, users can have several email client programs that communicate with the email server to continuously display the messages that have been read and those that have not.
The Internet standard protocol known as Internet Mail Access Protocol version 4 (IMAP4) stores and retrieves messages from Simple Mail Transfer Protocol (SMTP) sites. Like Post Office Protocol version 3 (POP3), Internet Mail Access Protocol version 4 (IMAP4) offers extra functionalities as detailed in this entry.
Features of IMAP
Key characteristics of the Internet Message Access Protocol are as follows:
- Multiple mailboxes: It allows users to maintain multiple mailboxes and send messages back and forth between them.
- Organize emails: Users can create folders and categories to better arrange their messages.
- Synchronization: This feature lets users synchronize their folders amongst their devices.
- Get mail from the distant server: IMAP lets users view their emails from a distance while maintaining server copies.
- Set flags: This feature enables users to quickly track read and unread messages by implementing message flags. Every message's status is kept, and the user can view it on their devices.
- Verify details before downloading: Before choosing to download, users can see emails and the email header, which includes the sender, subject, and date.
- Download a section of a message only: IMAP allows users to download a subset of a message.
- Search: This function enables users to look through email content.
- Hierarchy: IMAP enables users to create an email hierarchy according to the message's priority.
Versions of IMAP
A TOPS-20 server and a Xerox Lisp Machine client were used to construct the first Interim Mail Access Protocol. The original intermediate protocol definition and software are no longer in existence. The intermediate protocol's syntax was incompatible with all other versions of IMAP, even though some of its commands and answers were comparable to those of IMAP2.
IMAP2
The Interactive Mail Access Protocol (IMAP2), first described in RFC 1064 in 1988 and then revised in RFC 1176 in 1990, swiftly replaced the interim protocol. IMAP2 was the first version made available to the general public and incorporated command/response tagging.
IMAP3
An incredibly uncommon variation of IMAP is IMAP3. In 1991, it was released as RFC 1203. It was composed especially as a rebuttal to RFC 1176, which suggested changes to IMAP2. The market has never accepted IMAP3. In 1993, the Interactive Email Access Protocol (RFC1203), Version 3, was classed as a Historic protocol by the IESG. Rather than starting with RFC 1203 (IMAP3), the IMAP Working Group started with RFC 1176 (IMAP2).
IMAP2bis
IMAP2 was expanded to accommodate MIME body structures and provide mailbox management features (new, remove, rename, and upload messages) that were not present in IMAP2 with the introduction of MIME. The specification for this experimental iteration, IMAP2bis, was never released as anything other than a draft. The IETF IMAP Working Group released an online draft of IMAP2bis in October 1993. RFC 1176, RFC 1064 (IMAP2), and the unpublished IMAP2bis.TXT document served as the foundation for this draft. As of December 1992, the IMAP2bis.TXT draft recorded the current status of additions to IMAP2. Pine 4.00 and subsequent versions support IMAP4rev1, but early versions were widely distributed with support for IMAP2bis.
IMAP4
The early 1990s saw the formation of the IMAP Working Group within the IETF, which assumed control of the IMAP2bis design. The IMAP Working Group decided to rebrand IMAP2bis to IMAP4 to avoid misunderstanding.
Working of IMAP4

SMTP is the basic message transport technology for sending email over the Internet, but it doesn't offer any capability for message archiving or retrieval. Since most consumers don't have a dedicated Internet connection, SMTP hosts need to be constantly linked to one another.
IMAP4 offers methods for keeping SMTP messages in a container known as a mailbox. Before a user connects to download and view messages using an IMAP4 client like Microsoft Outlook 2000 or Microsoft Outlook Express, the messages that each user receives are stored on an IMAP4 server.
There are some capabilities in IMAP4 that POP3 does not provide.
To be more precise, IMAP4 enables users to:
- Access several folders, including public folders.
- Make folder hierarchies for storing messages.
- After reading a message, leave it on the server so they can access it later from a different location.
- Look for a specific message to download.
- Mark a message as read.
- Download only certain messages or attachments.
- Check the message headers before downloading.
An IMAP4 client initially creates a Transmission Control Protocol (TCP) connection using TCP port 143 to retrieve a message from an IMAP4 server.
After identifying itself to the server, the client sends the following IMAP4 commands to the server:
- SELECT: Choose a specific folder to view its messages.
- LIST: Returns a list of folders in the client's inbox.
- FETCH: Gets specific message content.
- LOGOUT: Closes the IMAP4 window.
The Exchange Server from Microsoft supports IMAP4. Mobile users who dial up and check their mail from numerous locations find IMAP4 especially helpful because IMAP4 clients can allow read messages to remain on the IMAP4 server. The drawback is that because users frequently leave a lot of messages on the server, IMAP4 servers utilize more resources than POP3 servers.
Sending and Receiving emails with IMAP
Here's a brief overview of how to send and receive emails using IMAP:
Sending emails
- Emails are sent using the Simple Mail Transfer Protocol (SMTP).
- Between the client and email server, a Transmission Control Protocol (TCP) connection is established. The server is informed to expect an email by this connection.
- The client sends the email to the server along with several commands.
- To determine the recipient's IP address and verify the email's domain name system (DNS) record, the email server employs a proprietary mail transfer agent (MTA) application. The MTA converts the DNS record into an IP address to determine where to send the emails.
- SMTP searches for a mail exchange (MX) record linked to the recipient's domain name. (The MX record is used to specify the SMTP routing criteria for messages.) The email is routed to the relevant server if an MX record is present.
Retrieving emails
- The email-receiving protocol is defined by IMAP.
- The email is accessible from any device and may be read by the client. These emails can only be accessed with an Internet connection since IMAP is an intermediary between the email client and server.
- To access their messages, an email client connects to the email server when a user logs in. The email message is not downloaded until the user clicks on it. However, the user can view a preview of it (including the sender and subject line).
- Until they are erased, the inbox owner's emails can be accessed through both the server and client connection.
Advantages of IMAP
The majority of IMAP implementations allow for multiple logins. Thanks to this feature, users can now connect to the email server from multiple devices simultaneously. For instance, users can simultaneously access their email using the Outlook desktop program and the Outlook app on their iPhones.
POP3 does not allow for multiple accesses; downloaded emails vanish from the server and are, therefore, not accessible later on from another device. Therefore, POP3 is only appropriate when consumers consistently check their email on the same device.
For customers who frequently travel or need to check their email from several devices or places, IMAP offers more flexibility in terms of access. The mail client developers are left to manage the specifics of handling numerous connections, as the protocol does not specify this.
To sum up, IMAP offers the following benefits:
- Email functions like search and sort are supported.
- The IMAP server supports IDLE extensions (push mail), which show emails in the inbox as unread and do away with the need for users to set up a polling interval or click "receive."
- Additionally, emails can be accessed quickly and efficiently from multiple devices, and the server can accommodate multiple users sharing a single mailbox. Finally, the email can be used offline.
Disadvantages of IMAP
IMAP has an authentication system, but because the client's username and password are transmitted in cleartext, anyone who knows how to use a protocol analyzer can simply get around the authentication procedure. An Exchange Server environment administrator can circumvent this security vulnerability by encrypting IMAP traffic using SSL.
IMAP is a widely used email retrieval mechanism in general. The rise in popularity of mobile devices like tablets and smartphones can be attributed to this: if you need to access your email while using many devices or while on the go, IMAP is the best option.
Conclusion
In conclusion, how we get our emails has become much more flexible thanks to Internet Message Access Protocol (IMAP). It is unquestionably one of the most significant protocols that give us rapid and simple access to our email correspondence.