E-mail in Computer Network
E-mail stands for electronic mail. E-mail is an application layer service in which a user can transfer the messages and information with another user. E-mail is the most popular service of the internet.
Architecture
There are four scenarios in the architecture of electronic mail (e-mail).
First Scenario
In the first scenario of e-mail, the sender and receiver use the same system, and that is directly connected to the server. This scenario requires only two user agent (UA).
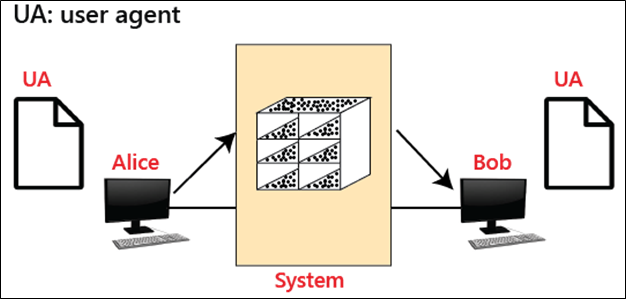
For example, let takes two user agents (Alice and Bob), that is shown in the figure. When Alice sends the mail to Bob, then Alice runs the user agent (UA) program to prepare the e-mail. After that, this e-mail is stored in the mailbox of Bob.
Second Scenario
In the second scenario of e-mail, the sender and receiver are used the two different systems. The e-mail is sent through the internet in this scenario. This scenario requires two user agents (UAs) and a pair of message transfer agents (MTAs). The example of this scenario is shown in the figure.
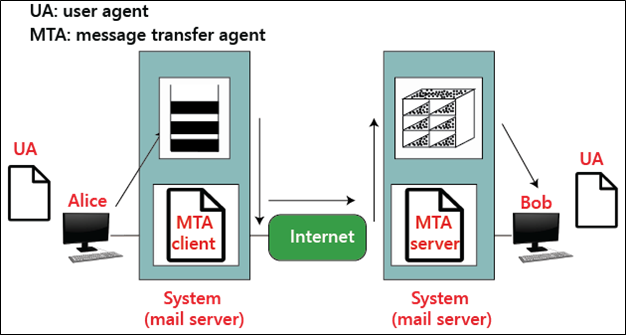
For example, let takes two user agents (Alice and Bob), which is shown in the figure. When Alice sends the mail to Bob, then Alice runs the user agent (UA) and message transfer agents (MTAs) program to prepare the e-mail through the internet. After that, this e-mail is stored in the mailbox of Bob.
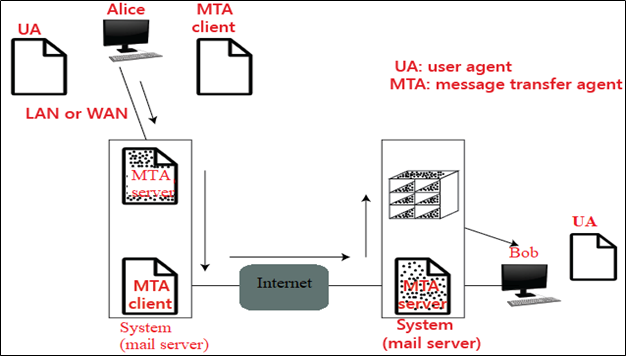
Third Scenario
In the third scenario of e-mail, the sender is connected to the server through a LAN and WAN. This scenario requires two user agents (UAs) and two pairs of message transfer agents (MTAs). The example of this scenario is shown in the figure.
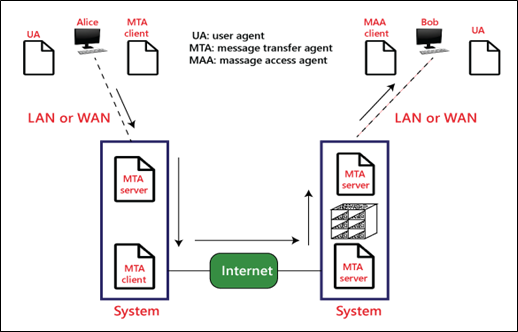
Fourth Scenario
In the fourth scenario of e-mail, the sender and receiver are connected to the server through a LAN and WAN. This scenario requires two user agents (UAs), two pairs of message transfer agents (MTAs), and a pair of message access agents (MAAs). The example of this scenario is shown in the figure.