OSI Model
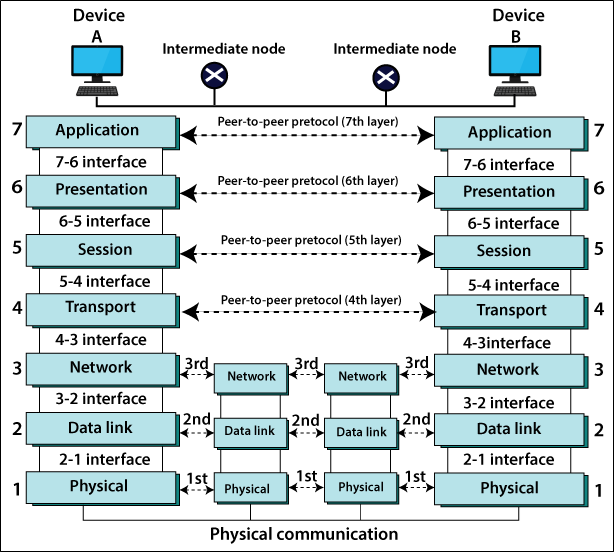
OSI Model: OSI stands for Open Systems Interconnection. The ISO (International Standards Organization) was introduced the OSI model in 1983.
The OSI model is a standard reference model for communication between two users in a network. Each layer of this model does not depend on the other layer, but the data is transmitted from one layer to another layer.
The OSI model describes how to send and receive data in a network. All layers of the OSI model have their different functions so that data can be easily accessed from one system to another.
OSI model divides into seven layers, as shown below in the figure.
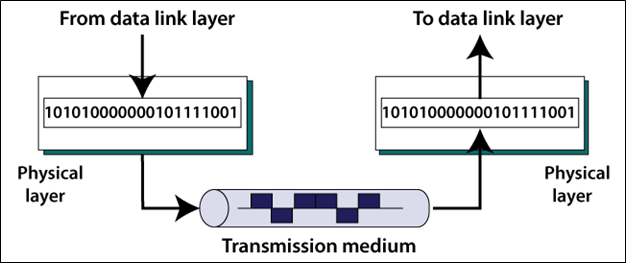
Layer 1: The Physical Layer
The first layer is the physical layer in the OSI model. This layer is also called a bit unit. The physical layer coordinates the functions needed to transmit a bit of stream to a physical medium.
It is responsible for the actual physical connection between devices. The physical layer also describes whether the communication will be wireless or wired. The repeater is a device of the physical layer. The figure shows below.
Major functions of the Physical Layers
- Physical characteristics of interface and media: It defines the interface properties between devices and transmission devices. It also defines the type of transmission medium.
- Line Configuration: There are two types of line configuration Point-To-Point Configuration and Multipoint Configuration. In a point-to-point configuration, the two devices are connected through a separate link. In a multipoint configuration, the link is shared between multiple devices.
- Data rate: In data rate, the number of bits transmitted per second, is also defined by the physical layer. In other words, the physical layer determines how long the bit lasts.
- Transmission mode: It defines which transmission mode will be between two devices in the network.
- Topology: The physical layer defines how the different devices are organized in a network such as a bus, star, mesh, ring topology.
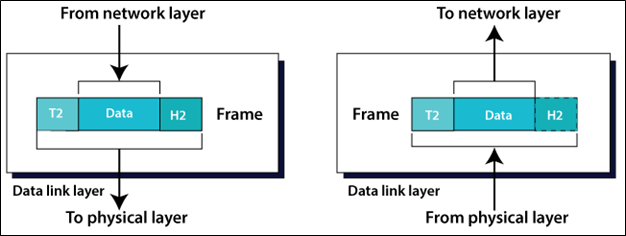
Layer 2: The Data Link Layer
The second layer is the Data Link layer in the OSI model. It is responsible for moving frames from one node to another. This layer is also called the Frame unit.
In this layer, packets of data sent by the network layer are decoded and encoded. This layer also ensures the packets of data are error-free. The figure shows below.
Major functions of the Data link layer
- Framing: The data link layer divides the bit-stream received from the network layer into manageable pieces of data units called frames.
- Flow control: If the rate at which the receiver receives the data is less than the rate at which the data is produced at the sender end, the data link layer establishes a flow control mechanism to avoid overloading at the receiver end.
- Error control: It controls the error. CRC (cyclic redundancy check) is added to the end of the frame with the trailer so that the data is error-free.
- Access Control: When two or more devices are connected to the same link, the layer will determine which device is given access.
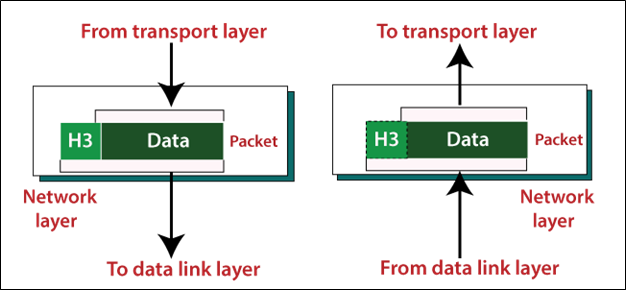
Layer 3: The Network Layer
The third layer is the Network layer in the OSI model. The data in the network layer is in the form of packets. It is responsible for the delivery of individual packets from the source to the destination. This layer is also called the packet unit. Switching and routing techniques are used in this layer. The figure shows below.
Major functions of the Data link layer
- Routing: When independent networks are connected to produce Internetworks, the connecting devices change the packets to their final end. One of the roles of this layer is to provide the mechanism.
- Logical addressing: The network layer defines a logical address so that each device on the Internet can be uniquely identified. The IP addresses of the sender and the receiver are placed in the header according to the network layer. This address distinguishes each device individually and generically.
Layer 4: The Transport Layer
The fourth layer is the Transport layer in the OSI model. It is responsible for the transfer of a message from one process to another. Although the network layer monitors the distribution of individual packets from source to destination, it does not recognize any connection between these packets. The transport layer also confirms a successful data transfer and re-transmits the data if an error is detected. The figure shows below.
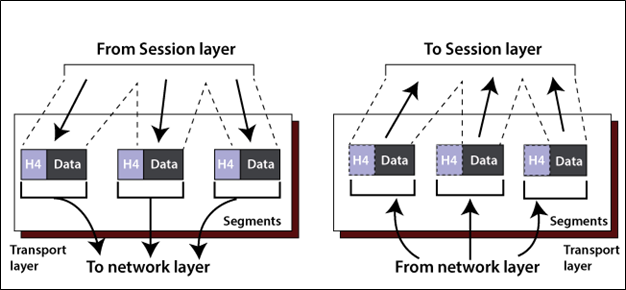
Major functions of the Transport Layer
- Segmentation and reassembly: When this layer receives a message from the upper layers, it divides the message into many abstract segments. Each segment has a sequence number so that each segment can be easily identified.
- Connection control: It provides two types of connection: - Connection-oriented and Connectionless. In a connectionless, it is done by the user diagram protocol (UDP). It sends the message directly to the destination without established the connection. UDP is faster than TCP because TCP does not establish the connection. In Connection-oriented, it is done by the transmission control protocol (TCP). In Connection-oriented, it establish the connection first, then send the message to the destination. UDP is slower than TCP because first UDP established the connection then sent the message.
- Flow control: The transport layer is responsible for flow control, similar to the data link layer. However, flow control in this layer is done end to end instead of a single link.
- Error control: The transport layer is responsible for error control, similar to the data link layer. However, error control in this layer is done end to end instead of a single link.
Layer 5: The Session Layer
The fifth layer is the Session layer in the OSI model, which controls connections between many computers. It manages, establishes, and terminates the session connection between two communication hosts. The figure shows below.
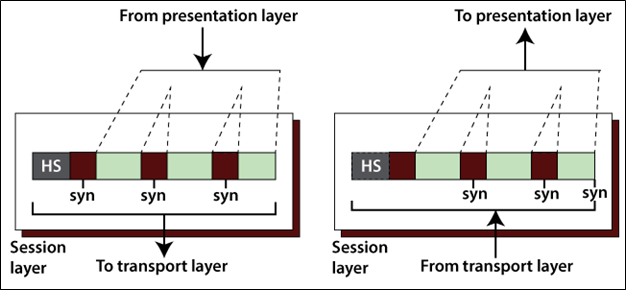
Major functions of the Session Layer
- Dialog control: In the session layer, it allows two systems to enter a dialog that allows the communication between two processes in either half-duplex mode or full-duplex mode.
- Synchronization: It allows us to add the checkpoints into the stream of data. For example, suppose the system is sending a message of 1000 bits, it inserts the checkpoints after every 50 bits and to ensure that each 50 bits unit is received and acknowledged individually. In this case, if a crash happens during the transmission of 453 bit, that only needs to be a retransmission of 401 to 453. Previous of 401 bits are not required to re-sent.
Layer 6: The Presentation Layer
The sixth layer is the Presentation Layer in the OSI model. In the Presentation layer, it deals with the syntax and semantics information which exchanges between two systems. The figure shows below.
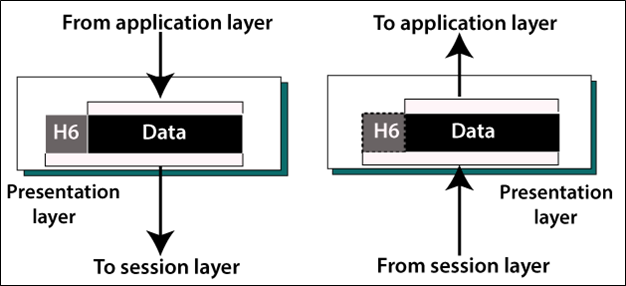
Major functions of the Session Layer
- Translation: It converts a message to compatible bit-streams before being transmitted because various computers use various encoding methods. It is responsible for interoperability between these various encoding methods, which is changing the message into a standard format.
- Encryption: Encryption means to transform the original message into another form, that will not be readable by others.
- Compression: In Compression, it reduces the number of bits to be transmitted over the network.
Layer 7: The Application Layer
The seventh layer is the Application Layer in the OSI model. The end-user is the closest of application layer. This layer enables user access to the network. It allows remote logging into the application. The figure shows below.
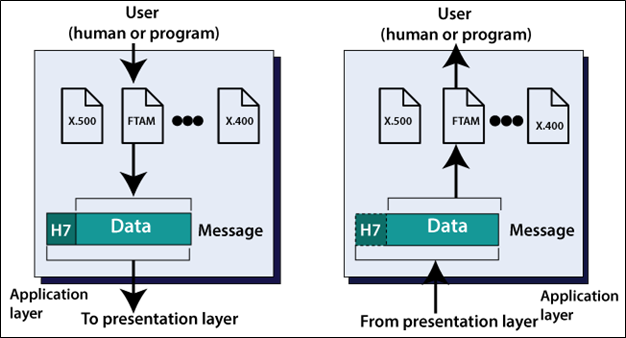
Major functions of the Session Layer
- Network Virtual Terminal: It's a physical terminal to the software version. It provides remote host services.
- File transfer, Access, and Management: It allows a user to access, retrieve, and manage the files from a remote host.
- Mail services: It provides email forwarding and storage.