TCP/IP model in Computer Network
TCP/IP model
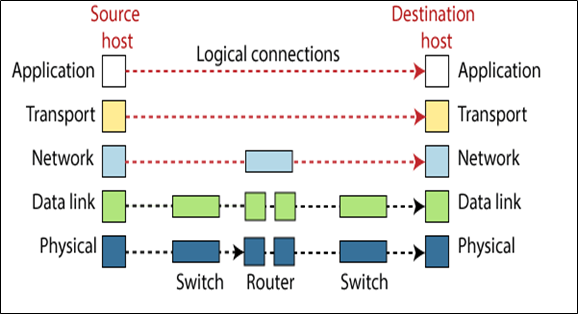
The TCP/IP model was developed by DARPA (Defense Advanced Research Projects Agency) in the 1970s. Therefore, the TCP/IP model is not the same as the OSI model. The original TCP/IP model has defined the four layers: Host-To-Network layer, Internet layer, Transport layer, and Application layer. But now it contains five layers Physical layer, Data link layer, Network layer, Transport layer, and Application layer.
Physical layer
The physical layer is the 1st layer of the TCP/IP. At the Physical layer, is communication between two nodes or hops. The physical layer at the TCP/IP supports all standard and established protocols. At this layer, the unit of the communication layer is a single bit.
Data-link layer
The data link layer is the 2nd layer of the TCP/IP. At the Data link layer, is communication between two nodes or hops. The Data-link layer at the TCP/IP supports all standard and established protocols. At this layer, the unit of communication is the frame.
Network layer
The network layer is the 3rd layer of the TCP/IP. This layer acts as the Network Layer of the OSI Model. The main feature of this layer is provided to connectionless communication in the network. The network layer at the TCP/IP model follows the internetworking protocol. Often defined as the network layer is known as the internet layer.
The common protocols used within the Network protocols
- Internetworking Protocol: The Internetworking Protocol (IP) is a mechanism used by TCP / IP for communication. Internetworking protocol is an unreliable protocol for best-effort delivery service. The term of best effort means that IP provides no tracking or error checking. It is a connectionless protocol. At the Internetworking protocol, the data is transport in packets form that is called as the datagram. Each packet is transported separately.
- ARP (Address Resolution Protocol): Address Resolution Protocol is used to connect logical addresses to physical addresses. ARP protocol is used to detect the physical address of a node considered to have an IP address.
- RARP (Reverse Address Resolution Protocol): RARP is the opposite of ARP. The RARP allows a host to detect its IP address when it only knows its physical address. RARP is used when a computer is linked to a new network or when any diskless computer is booted.
- ICMP (Internet Control Message Protocol): The ICMP is a mechanism which sends the message to the sender about the query and error reporting. The hosts and gateways use it to transfer the information about the datagram problems back to the sender.
- IGMP (Internet Group Message Protocol): The IGMP is used to facilitate the transfer of the message to the group of the receiver at the same time.
Transport layer
The transport layer is the 4th layer of the TCP/IP. The transport layer at the TCP/IP model is responsible for managing end-to-end communications. The transport layer provides three protocols UDP, TCP, and SCTP. UDP and TCP are responsible for the delivery of messages from one process to another process. The SCTP protocol was developed later to meet the needs of newer applications.
- UDP (User Datagram Protocol): UDP is a simple transport layer communication protocol. It is a connection-less protocol. When data transfer occurs, this protocol does not establish the connection between the sender and the receiver. UDP is an Unreliable Protocol.
- TCP (Transmission Control Protocol): TCP is a Connection-Oriented Protocol. When data transfer occurs, this protocol does establish the connection between the sender and the receiver. TCP is a reliable protocol.
- SCTP (Stream Control Transmission Protocol): SCTP is the combination of the best features of the TCP and UDP protocol. SCTP was introduced to support newer applications over the internet, such as video calling and voice messages.
Application layer
In the TCP/IP model, the application layer is equivalent to the combination of the session layer, presentation layer, and application layer in the OSI model. The application layer is related to providing network service to applications.
The common protocols used within the Application Layer are, such as Telnet, FTP, HTTP, SMTP, POP3, and NFS.