Transmission Control Protocol
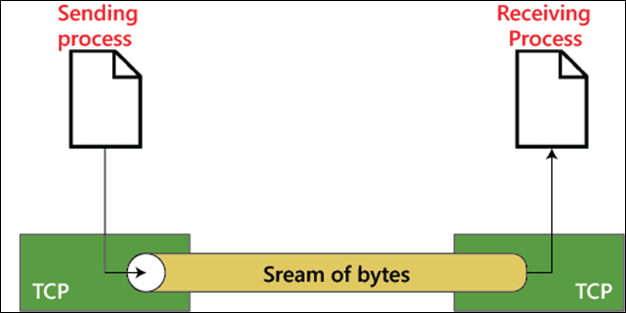
Transmission Control Protocol: TCP stands for Transmission Control Protocol. It was introduced in 1974. It is a connection-oriented and reliable protocol. It establishes a connection between the source and destination device before starting the communication. It detects whether the destination device has received the data sent from the source device or not. If the received data is not in the proper format, it sends the data again. TCP is highly reliable because it uses a handshake and traffic control mechanism. In the TCP protocol, the receiver receives the data in the same sequence in which the sender sends it. We use the TCP protocol services in our daily life, such as HTTP, HTTPS, Telnet, FTP, SMTP, etc.
Importance of UDP
- The TCP protocol is used to transfer data where, you need accuracy and reliability rather than the speed.
- Both TCP and UDP can check for errors, but only TCP can fix the error because it can control the traffic and flow of data.
TCP Segment Format
In the TCP, the data packet is called a segment. The size of the header in the segment is 20 to 60 bytes. The segment format of TCP is shown below the figure.
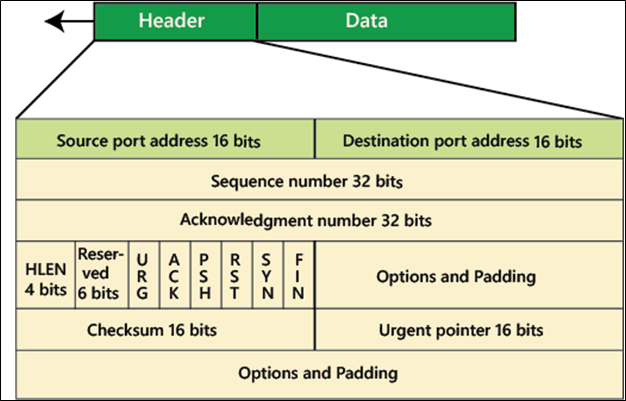
- Source Port Address: The size of the source port is 16 bits. It is used to define the port address of the application that sends the segment.
- Destination Port Address: The size of the destination port is 16 bits. The destination port is used to define the port address of the application that receives the segment.
- Sequence Number: The size of the sequence number is 32 bits. It defines the unique number of the data in the segment.
- Acknowledgment number: The size of the acknowledgment number is 32 bits.
- Header Length: The size of the header length is 4 bits. It indicates the header of the application. The header length can be lies between 20 and 60 bytes. Therefore, the value of this field is 5 (5 × 4 = 20) and 15 (15 × 4 = 60).
- Reserved: The size of this field is 6 bits. This field is for future uses.
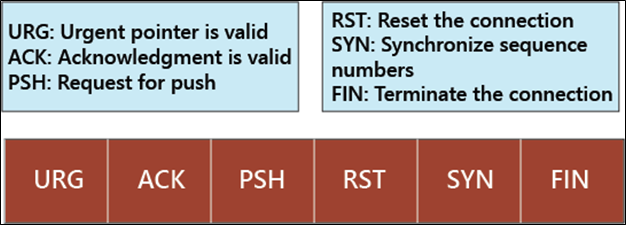
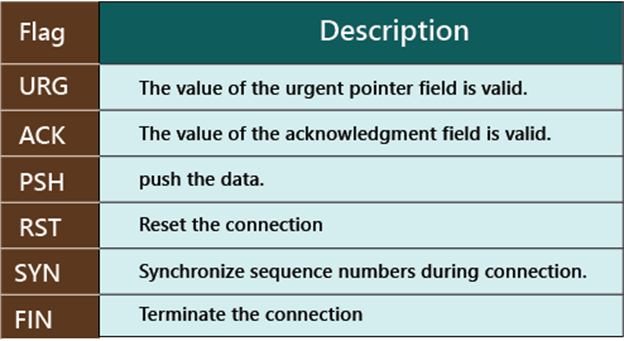
- Control Flag: The size of this field is 6 bits. It defines the six different control bits or flags, as shown in the figure.
- Window Size: The size of the window field is 16 bits. It defines the size of the sending window of the sender.
- Checksum: The size of the checksum field is 16 bits. The checksum field is used for error control. It is mandatory in TCP.
- Urgent Pointer: The size of the urgent pointer field is 16 bits, which is only required when the URG flag is set. It is used for urgent data in the segment.
- Options and Padding: The size of options and padding field vary from 0 to 40 bytes.
Advantages of TCP
- Retransmission: In the TCP, when a data fail, this protocol sends that data again after a specific time.
- TCP can fix the error because it can control the flow-control and congestion control.
- TCP can easily detect the errors.
- In the TCP protocol, the receiver receives the data in the same sequencer in which the sender sends it.
Disadvantages of TCP
- The data transfer speed of the TCP protocol is less than the UDP protocol.
- TCP protocol cannot broadcast and multicast the message.