User Datagram Protocol
User Datagram Protocol: UDP stands for the User Datagram Protocol. UDP was developed by David P Reed in 1980. It is a connection-less and unreliable protocol. In this protocol, when the data transfer occurs, it does not establish the connection between the sender and receiver. It sends the data directly. The receiver does not send any acknowledgment of the receiving data in this protocol. In the UDP, the data packet is called datagram.
UDP does not guarantee any user data, whether it will reach its destination or not. In this protocol, it is not necessary that the data reach the receiver in the same sequencer in which the sender has sent the data.
Importance of UDP
- The UDP protocol is used to transfer data where you need a higher speed than accuracy and reliability.
- If the data flow is in the same direction, UDP is used.
- It is also used for streaming applications, for example, YouTube and online gaming.
- It provides faster data transfer speed than the TCP protocol.
User Datagram Protocol Format
The UDP format is very simple. The header size of the UDP is 8 bytes (8 bytes mean 64 bits). The format of UDP is shown below in the figure.
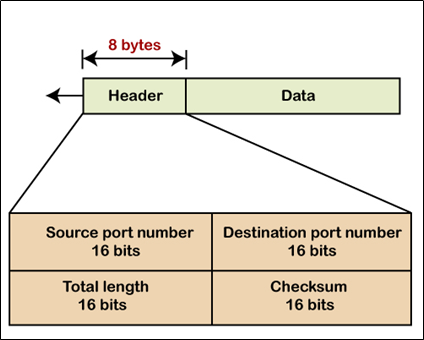
It has four fields shown below:
- Source Port Number: The size of the source port is 16 bits. It is used to identify the process of the sender.
- Destination Port Number: The size of the destination port is 16 bits. It is used to identify the process of the receiver.
- Total length: The size of the total length is 16 bits. It defines the total length of the UDP and also stores the length of the data and header.
UDP length = IP length - IP header's length
- Checksum: The size of the checksum port is 16 bits. It is used to detect errors across the entire user datagram.
Advantages of UDP
- You can easily broadcast and multicast transmission through the UDP.
- It is faster than TCP.
- It uses the small size of the header (8 bytes).
- It takes less memory than other protocols.
- Whenever data packets need to be transmitted, then UDP is used.
Disadvantages of UDP
- It is an unreliable protocol for transmission.
- There is no such function in it to know that the data has been received or not.
- The handshake method is not used in UDP.
- It does not control the congestion.
- The main disadvantage of using routers with UDP is that once transmission failure occurs, the routers do not transmit the datagram again.
UDP is used in the following applications.
- Domain name system.
- Simple network management protocol.
- Routing information protocol.
- Trivial file transfer protocol.
Services of UDP and TCP
| Services | UDP | TCP |
| Sequence data delivery | No | Yes |
| Multi-Streaming | No | No |
| Multi-Homing | No | No |
| Connection-Oriented | No | Yes |
| Connection-less | Yes | No |
| Allows half-closed connection | N/A | Yes |
| Application PDU bundling | No | Yes |
| Congestion Control | No | Yes |
| Application PDU fragmentation | No | Yes |
| Preserve message boundaries | Yes | No |
| Partial reliable data transfer | No | No |
| Selective Acknowledgements | No | Optional |