Java Networking
Networking
Networking is a way of communicating the devices. It is made up of various technologies like computers, switches, routers that are interconnected and share data among themselves.
The two common network protocols:
1. TCP/IP
TCP stands for Transmission Control Protocol/Internet Protocol that allows reliable communication between two applications. TCP/IP specifies data exchange over the end-to-end communications and specify how it should be broken, transmitted, routed, packets, addressed, and received at the destination. TCP/IP is compatible with all the operating systems. TCP/IP is a highly scalable and routable protocol that searches the most efficient path through the network. The two main protocols in TCP/IP protocol suite serve specific functions:
- TCP: The application can create channels of communication across the network. It also manages how messages are assembled into smaller packets and then transmit it over the Internet and re-assembled in the right order at the destination address.
- IP: It defines how to address and route each packet to make sure it reaches the right destination.
2. UDP
UDP stands for User Datagram Protocol, a connectionless protocol that allows the packets of data to be transmitted between the applications. It is an unreliable and connectionless protocol, so there is no need to establish a connection before transferring the data. UDP permits packets drops instead of processing delayed packets. There is no error checking in UDP. UDP is more efficient, based on both latency and bandwidth. It is useful when it reduces the requirement of computer resources, the transmission of Real-time packets, mainly in multimedia applications. It is used for simple request-response communication when the size of data is less. It is a suitable protocol for multicasting as UDP supports packet switching. UDP is used for routing some update protocols. It is usually used for real-time applications that cannot tolerate uneven delays between sections of a received message.
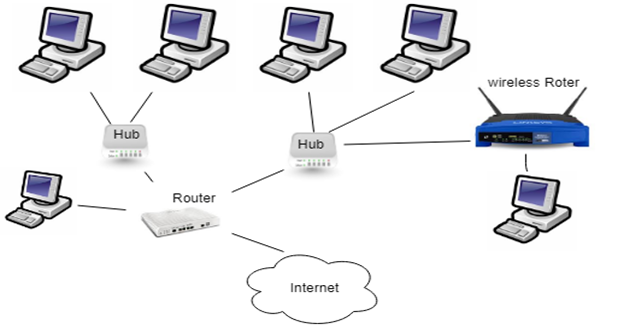
Networking has the following modules, such as:
- Clients and Servers.
- IP Addresses.
- A network hub, switches, and cables.
- Routers and firewalls.
Client and Server concept
It is an essential architecture to communicate with each other over the network.
Server
- The server is the computer that holds services and every single information related to the clients such as media files, database-related matters, and keep the website for Google search page, etc.
- It provides services in the form of webpages and sends it out when requested by the client.
Client
- The client is a different computer that requests to view, download, or search the content from the server, such as to request for Google web page, etc.
- A client connects to the server and other clients over a network to exchange the information and data.
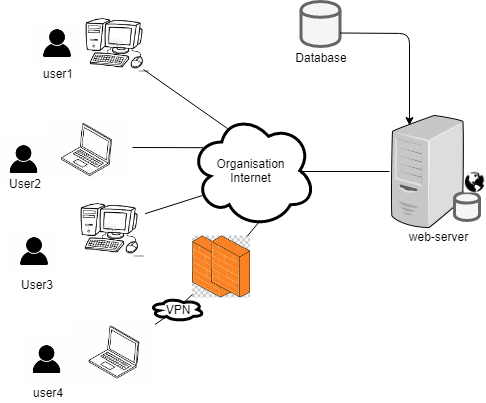
Mechanism of a working client-server architecture
In a client-server architecture, the client computer sends a request for data to the server, the server accepts the request of the client, process it, and deliver the data packets requested back to the client. One unique feature is that the server computer has the potential to manage numerous at the same time.
On the network, the server can locate anywhere, and if the client has its IP Address, it can access its services efficiently. The client asks for the services like website accessed from the server computer. The respective site is delivered through the server and displayed on the client web browser in the form of webpages.
IP Address
It is a unique address to identify the computer on the network. It is used for directing the data across a network, computers need to identify their destinations and origins. It is an identification which is known as IP Address.
Two types of IP Address:
- IPv4
- IPv6
IPv4 address
The IPv4 protocol is assigned for 232 addresses. Addresses in IPv4 is 32-bits long. There is a maximum of 4,294,967,296 unique addresses. IPv4 is 32- bit binary number that contains two sub-addresses i.e., the network and the host, with an imaginary boundary separating them. An IP address is represented as 4 octets of numbers from 0-255 represented in decimal form. An IPv4 address is represented in dotted-decimal notation, with every eight bits (octet) represented by a number from 1 to 255, each separated by a dot. An example of an IPv4 address is 192.168.17.43.
IPv4 address contains two parts. The first part of the address specifies the network, and the second part specifies the host. A host represents a server offering resource information, services, and applications to users or other nodes on the network. It is a network that uses various protocols and attaches various hosts for their inter-communications.
IPv6 addresses
To avoid the address space issue in technology and to increase the address size from 32 bits in IPv4 to 128 bits, IPv6 specifies 3.4*1038 (2128) unique addresses. These are reportedly enough addresses, assigned one to every single host on the Internet. IPv6 addresses are shown in the form of eight sets of four hexadecimal digits, and each set of numbers separates by a colon. It looks like 2DAB:FFFF:0000:3EAE:01AA:00FF:DD72:2C4A. There are no defined classes in the IPv6 version.
Network devices
Repeater
A repeater is operated at the physical layer. It is used to regenerate the signal before it becomes too weak or corrupted so that the signal can be transmitted over the network. The repeaters do not amplify the signal. They put the signal bit by bit and regenerate it at the original strength when the signal becomes weak.
Cables
Computers are connected via cables to create a network. But sometimes individual computers and cables were not able to make a good system so to overcome this issue hubs came into existence. The cable is a media that transmits the communication signals.
There are three types of cables:
- Twisted-pair cable: It is a high-speed cable that transmits the data over 1Gbps or more.
- Coaxial cable: Coaxial cable resembles a TV installation cable. Coaxial cable is expensive than the twisted pair cable and provides a high data transmission speed.
- Fiber optic cable: It is a high-speed cable that transmits the data using a light beam. It has a high data transmission speed as compared to other cables and more expensive as compared to other cables.
Hub
A hub connects multiple cables coming from different branches. Hubs do not filter the data. Data packets are sent to all connected devices. The collision domain of all hosts connected through Hub remains one. It does not have the intelligence to find out the best path for the data packets, which leads to inefficiencies and wastage. It is the way to interconnect LANs. The Hub amplifies the signal. If a device wants to communicate a message to many computers, it sends a message to the Hub. It is the responsibility of Hub to resend the message to all the computers. Hub can slow down if many computers try to send a message again and again at a time, which leads to confusing the hub.
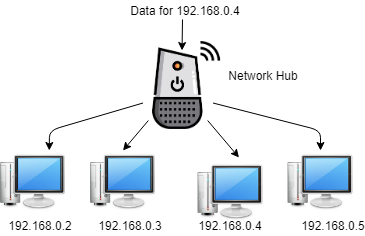
- Hub works on the physical layer (Layer 1 of the OSI model).
- Hub works internally in bus topology.
- It has 2,4,8 ports to establish communication between the devices. They allow communication to a maximum of 8 devices.
- Hub is not an intelligent device. If computer1 wants to communicate with the computer2, routers transfer the message to all the computers attached to its ports.
- The message which is broadcasted contains the sender and receiver address. It can be read or modified by the others, but it is accepted by its respective receiver.
- Hub favors a single Collision domain that has a single way to communicate with other computers. If more than one computer sends its packets, they will collide among themselves.
- Hub can only be used in the LAN network.
- Hub does not have a table to store MAC address or IP address for the computers; that is why it broadcast the messages to all the computers.
There are two types of Hub:
- Active Hub-It acts as a Repeaters as it needs electricity to run. Still, it amplifies the analog signal or regenerates the digital signal so that the signal can be transferred over a long way.
- Passive Hub-It does not require electricity. It does not amplify the signal but only receive and forward the signal.
Bridges
A bridge is operated at the data link layer. A bridge functions as a repeater, with the functionality of filtering content by reading the MAC addresses of source and destination. It is used to interconnect two LANs working on the same protocol.
The bridges are full-fledged packet switches that forward and filter frames using the LAN destination addresses. When a frame reaches the bridge interface, the bridge does not copy the frame onto all of the other interfaces. The bridge specifies the destination address of the frame and attempts to forward the frame to the destination.
The bridge determines the 48-bit destination address for the packet and directs the packet only to the cable where the recipient resides. One packet causes less congestion, thereby. A bridge may store (buffer) enough bits to interpret the destination address. It could store (buffer) a whole packet and queue it for the correct outgoing link.
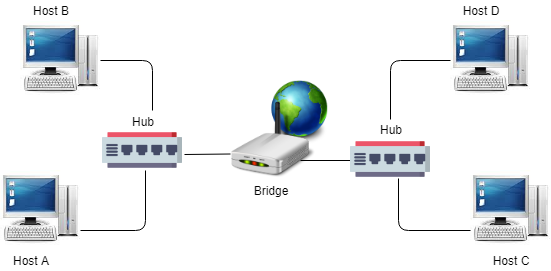
Features:
- It is an intelligent device. Bridge inspect incoming traffic and decide whether to forward or reject.
- It checks the source and destination MAC address, not IP address as the IP address do not work on the datalink layer.
- The bridge is broadcasted to all devices at the first time, then it is broadcast to one of the segments of either side as it knows the MAC address of the device on its port.
- It is used to connect multiple network segments or LAN segment.
- It can filter data traffic.
- Bridges decrease the traffic on the LAN by dividing it into two segments.
- It has two collision Domains.
Switches
A switch is a networking device that works on the data link layer device. It makes efficient communication as it does not forward packets that have errors and forward good packets selectively to correct port only. A network switch is a device that is used to connect multiple computers inside LAN (Local Area Network). Network switches perform at the second layer (Data Link Layer) of the OSI model. The basic function of a Network switch is to forward layer 2 packets (Ethernet frames) from source device to destination device.
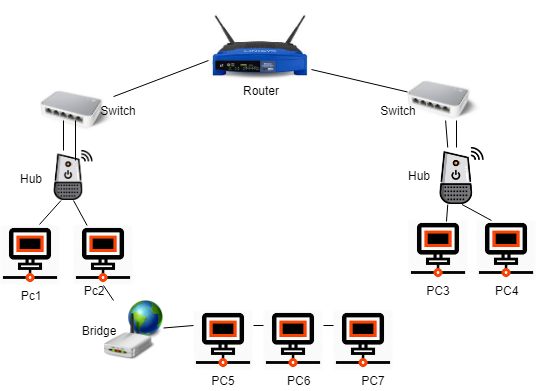
Features:
- It is an intelligent device and also works on the Data Link layer.
- The switch has multiple collision Domains, so there is less chance of collision of messages, among others.
- It has full-duplex communication.
- It maintains a CAM table based on the MAC address. It will communicate among all the devices on the basis of the CAM table.
- First, it will broadcasts then unicast and multicast.
- Every port of the switch is a separate collision domain.
- The switch has one Broadcasting domain.
- It has a maximum of 48 switch ports.
- It is slow as compared to others.
Types of switches
- Store and forward switch- The switch buffers and verify each frame before forwarding it. It is a little bit slow but very reliable.
- Cut through switch- The switch reads up to the frame hardware address before starting to forward it. No error checking.
- Fragment Free Switch- A method that attempts to retain the benefits of both store and forward and cut through check first 64 bytes.
Routers and Firewalls
Routers
A router relates to the network device that routes data packets based on their IP addresses. The router is mainly a Network Layer device. A Router connects WANs and LANs and has a dynamically updating routing table based on which they make decisions on routing the data packets. Routers are the first device in your network that gives you internet connectivity.
Features:
- It is the layer 3 device.
- It is a WAN device.
- The router is an internetworking device. It can communicate between two or more different networks.
- The router has a routing table and maintains Network ID and port number in its table. It communicates the messages based on its Network ID.
- It mostly uses WAN, not LAN.
- In the router, every port has its broadcast domain for broadcasting the messages.
- It has 2,4,8 ports.
- It is fast as compared to others.
Firewalls:
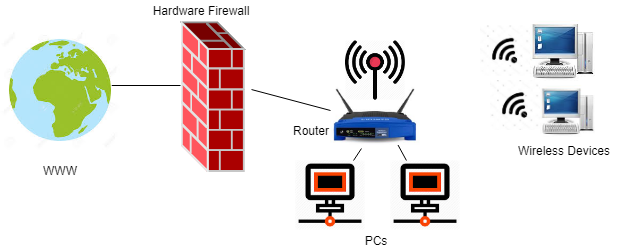
They can filter users and keep them out of private networks. Firewalls are network security appliances. Most of the small networks have perimeter-hardware firewalls, for controlling access and securing local networks from the outside world. Due to this reason, most perimeter firewalls also have routing capabilities.
The routers route traffic between two separate networks, firewalls monitor the traffic and block unauthorized traffic coming from the outside into your network. Few firewalls contain antivirus mechanisms to protect your network from viruses and unwanted emails.
There are many software firewall programs you can install on your computer, such as McAfee total protection, Norton antivirus, etc.
Gateway
A gateway is a connecting device used to connect remote networks with the host network. Generally, it acts as an entry or exit point. Mostly gateway is operated at the application layer.
A gateway is a way to connect two networks that may work upon different networking models. They work as a messenger agent that take data from one system, interpret it, and transfer it to another system. Gateways are also referred to as protocol converters and can operate at any network layer.
Uses of computer Network
- Resource sharing
These are the resources that are shared, such as programs, printers, and data among the users on the network.
- Server-client model
The computer networking is used in the server-client model. A server acts as a central computer, used to store the information, and maintained by the system administrator. Clients act as a machine used to access the information stored in the remote server.
- Communication medium
The computer network offers the communication medium among the users.
- e-commerce
The computer network is also important in businesses. We can perform business over the internet.