How to hack a computer?
How to hack a computer?
The human species are very inquisitive, and with the popularity of the Internet and modern technologies, they are becoming highly tech-savvy. The digital world is evolving every minute. With advancement, there are challenges for securing all our digital data such as cloud data, net banking, google drives, etc. and protecting them from cyber hacking. To prevent such attacks, cybersecurity is achieved. We can describe cybersecurity as a system of shielding networks, software, data and computer systems, illegitimate malware and digital attacks. These unauthorized attacks are known as “hacking.”

The social understanding of hacking is someone that exploits computers and steals people’s information. Of course, this definition is correct, and too many people think this is precisely what it is. But this is just one side of the mirror and is an incomplete definition.
“Hacking refers to method of exploiting weaknesses in a computer network to attain unauthorized entree to data and information, whereas a hacker is a person who attempts to hack into computer systems.”
Hacker's actual definition is someone who used technology for purposes over what is meant for now. That doesn't sound too bad. It wouldn't have a lot of successful technology today it's such as the complete Apple if it wasn't for Steve wasn’t hadn’t being a hacker. So it wasn't the hackers like Steve. There wasn't yet we had a revolutionary company like Apple. Maybe some people see that it is a good thing and open; we help by saying Apple is a revolutionary company.
Types of hackers
This is a misconception that hacking he's always unethical. But it depends on the motives with which the hackers are performing their jobs. So from hacking, we get inventions and can make a difference to humanity if we use it in the right way. It means that we can move forward in a technological world and why things like secure online banking exist, also we get open source software programming languages and much more. Guess what else is made of hacking- the Internet.
- White Hat Hacker: In reality, these people are all good guy hackers, but how to label them. The hackers with a purpose and who work in an environment and enjoy the problem solving an intellectual challenge are known as white hat hackers. White hat hackers expose the loopholes in the structure by hacking into the PC legally to protect it from authorized access or fetch information used in legal works. They perform all the activities legally under the supervision and acknowledgment of government. Hence they are also known as ethical hackers.
- Black Hat Hacker: The people who do hacking for their gain, such as people who were exploited, make money illegally by exploiting rules, and thus, they are known as a black hat hacker.
- Gray Hat Hacker: Finally, we also have a third category known as a gray hat hacker. Gray Hat Hackers are a blend of both white and black hackers. The ethical standards false, and they are purely altruistic and filled with malicious tasks. They do not get a company’s permission to start breaking into their data and information. They may not try to them about the security holes. Discovered sniper abilities in the system and reported to the system, which is a good actor, but they do this without seeking the others' approval.
Hacking Computer: Using Bypassing Login Method
Bypassing a login method refers to hoping the computer’s login screen and directly entering the PC's home screen. This method was initially discovered to login to your computer in case you have forgotten your password. But later, hackers used the Bypass login method to fulfill their malicious intent to crack into someone else’s computer without their authority. Before we start, we need to get acquainted with three types of Microsoft logging accounts, which are as follows:
- Local User Account: They are authenticated with a local computer and we can reset or bypass their settings.
- Microsoft online account: This user account is authenticated from another server.
- Domain user account: Both Microsoft online account and domain user account are somehow identical as both accounts are authenticated from another server and cannot be bypassed easily.
The second thing we need to understand is the type of user that we can have in a computer system i.e., whether it an administrator or is any standard user. Window 10 doesn’t permit to tamper the Administrator account or bypass its password as the administrator have the rights to access all folders or files within a computer system. Standard user accounts have limitations and they can only access the files stored within their account. Thus, bypass login methods are useful to hack standards user accounts.
Below down we will be discussing the step-by-step procedures to skip or bypass Windows 10 password login:
Step 1: Understand what this will accomplish.
Although Windows 10 doesn't permit to misuse or tamper the current Administrator account settings you can create a loophole by adding a new administrator user account using the installation drive and Command Prompt. Thus, you can access the key account's files and folders.
Step 2: Windows 10 installation tool.
We need to have a working computer and a blank flash drive with a size capacity of 4 or 8 gigabytes in size. To create a Windows 10 installation tool, follow the below steps:
- Plug in the flash drive to your working PC.
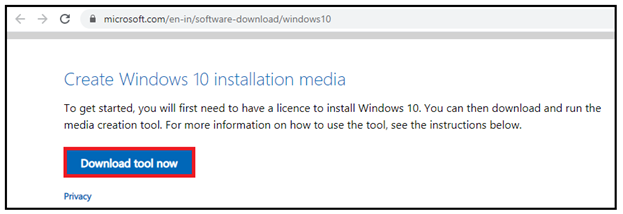
- Open your web browser; go to Microsoft website and type in ‘Windows 10 download’. The window will appear. In the Create Windows 10 installation media click on Download tool now.
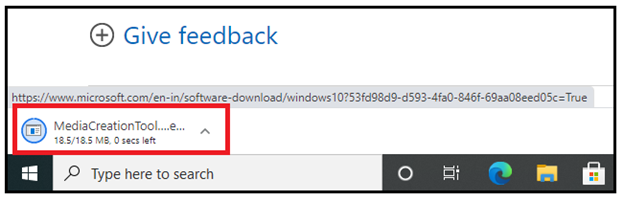
- Once the downloading is accomplished, open the file by double-clicking on the file.
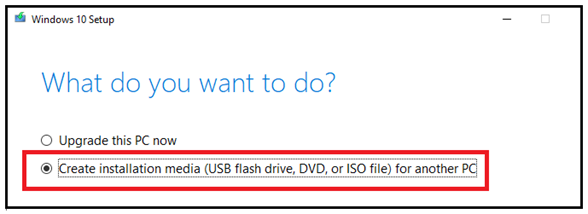
- We will make Windows 10 bootable media by following the alerts when prompted. Select the USP drive option.
- Do not remove the USB drive even if the download is finished.
Step 3: Modify the boot order of your computer.
This step is essential to necessary in order to shift your PC to start from the USP drive rather than the hard drive. We will make the Windows 10 bootable media a tool for us to reset or bypass a forgotten password.
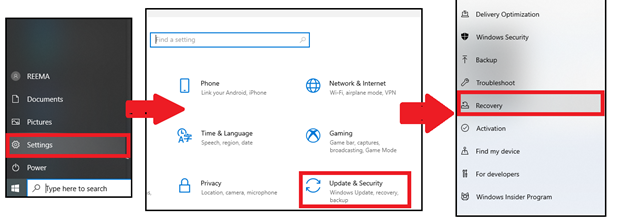
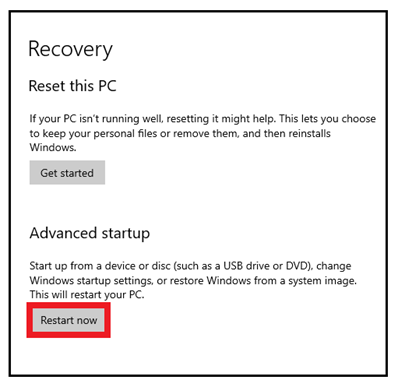
Open your start menu bar. Choose Settings -> Update and Security -> Recovery.
In the recovery dialog box, click on Restart now option.
It will open your PC’s BIOS setup. Select the Advanced or Boot tab situated under the “Boot Order” section.
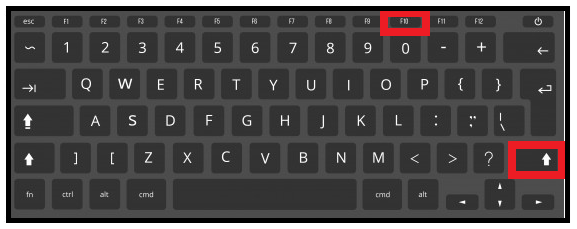
Select the name of your respective flash drive, click on the up arrow key on your keyboard and hold until the flash drive is listed at the top of the list.
Save and exit from the screen.
Step 4: Open the Command Prompt window.
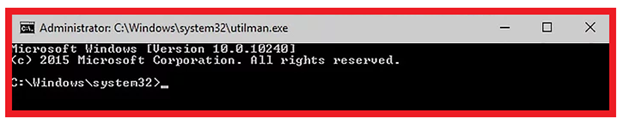
The setup screen will be prompted. Press the Shift and F10 keys simultaneously to open the Command Prompt window.
Step 5: Swap the Utility Manager with Command Prompt.
Utility Manager is a service which allows the user to execute the administrator account functions without even login into the admin user account. Follow the below steps to do so:
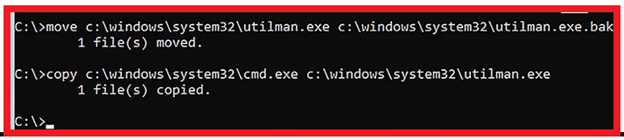
- Type the command into the Command Prompt
“movec:\windows\system32\utilman.exec:\windows\system'''32\utilman.exe.bak “
- Press the enter button on your keyboard. In the next line of the prompt , again type in
“copyc:\windows\system32\cmd.exec:\windows\system32\utilman.exe .”
- One done press the enter button.
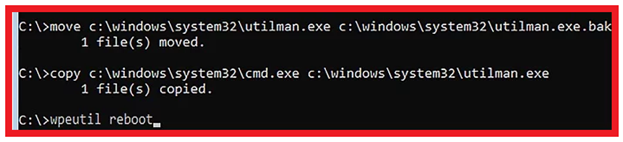
Step 6: Restart your computer.
To restart your computer, type the‘ wpeutil reboot’ command in your Command Prompt window and hit the Enter button. Make sure to delete the installation media files from the PC. It is useful to reboot the Windows to the login screen instead of backing into the installation setup.
NOTE: Sometimes, you didn’t get a chance to remove the flash drive as the Windows boots instantly into the installation setup. In this type of situation, quickly remove the USB stick and press your computer's power button.
Step 7: Open Command Prompt. Once the lock screen appears, locate for the "Utility Manager" icon and click on it. It will immediately open a Command Prompt window.
Step 8: Create your user account.
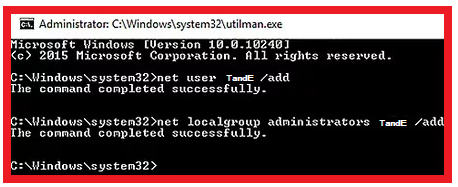
Once the Command Prompt is prompted, follow the below steps:
- Type in ‘net user name /add’ command in the prompt window.
- Press the Enter button. The cursor will be pointed to the next line of the window.
- Type in ‘net localgroup administrators name /add’ command, and it will replace the existing "name" with the user name you just made.
- Press the Enter button.
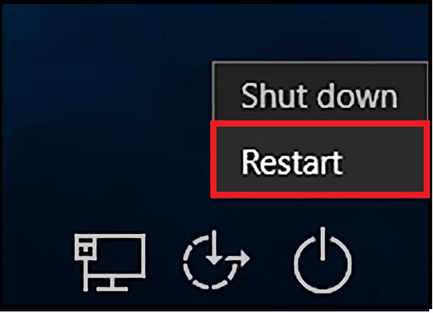
Step 9: Restart your computer again.
Once you have created the account, the next step is to press the Power icon on your keyboard. Select the Restart option from the windows prompt box. You will notice your computer will again start restarting.
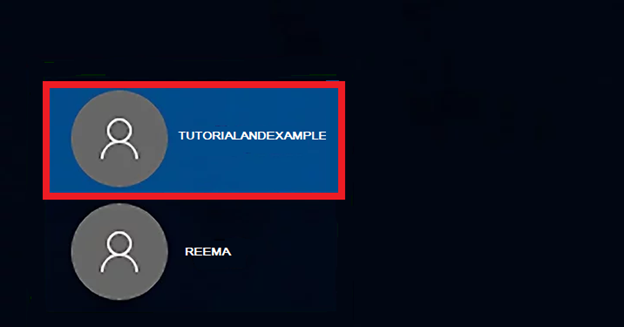
Step 10: Log in using your new account and password.
Once the restarting is finished, you would be able to login using your new admin account. Select your created user's name located in the lower-left corner of the desktop.
Step 11: Sign In as a Hacker
Windows will take some time to set up your new admin account. Once it’s finished, you can entitle yourself as a HACKER!
Tip: It’s is one of the standard methods to hack into anyone’s computer by bypassing the password. Though it’s easy still, it’s an illegal method to enter forcefully into someone’s system. It is always advisable to perform this method legally for any official purpose.