What is Computer Crime?
Computer crime, also known as cybercrime, is any illegal activity involving a computer or network. This can include unauthorized access to a computer or network, using fraudulent emails or websites to obtain personal information (phishing), and using software designed to harm or damage a computer system (Malware). Other examples of computer crime include identity theft, cyberstalking, and intellectual property theft. Computer crime can have serious consequences for individuals and organizations, and it is important to protect yourself and your computer systems from these types of activities.
Types of Cybercrime
1) Hacking
Hacking is the unauthorized access to or manipulation of computer systems, networks, or data. It refers to exploiting vulnerabilities in computer systems and networks to gain unauthorized access to sensitive information or cause harm. Hacking can take many forms, from simple password cracking to sophisticated cyber attacks that exploit multiple vulnerabilities. Hacking is often used for malicious purposes, such as stealing sensitive information, spreading Malware, or disrupting critical systems and services.
However, there is also a type of hacking known as ethical hacking or white-hat hacking, where individuals use hacking techniques to identify and report security vulnerabilities in computer systems and networks. This hacking is performed with the system owner's permission to improve the system's security.
Regardless of the type of hacking, it is illegal and unethical to gain unauthorized access to computer systems, networks, or data. The consequences of hacking can range from civil penalties and fines to imprisonment, depending on the nature and severity of the offense.
Is Hacking Good or bad?
Hacking can have positive and negative consequences, depending on the context and the hacker's motives.
On the one hand, ethical hacking can be a valuable tool for improving the security of computer systems and networks. Ethical hackers can help organizations and individuals better protect their information and prevent malicious attacks by identifying and reporting vulnerabilities.
On the other hand, malicious hacking, also known as "black hat" hacking, can have serious negative consequences, including theft of sensitive information, disruption of computer systems, and financial loss. Malicious hacking can also harm individuals and organizations by violating their privacy and undermining trust in technology.
In general, hacking without proper authorization is illegal and unethical, regardless of the intention behind the act. Ethical hacking should only be performed with prior permission from the owner of the tested system, and all activities should comply with relevant laws and regulations.
Difference Between Hacker and Cracker
The terms "hacker" and "cracker" are often used interchangeably, but they have distinct meanings.
A hacker is a person who uses their technical knowledge to gain unauthorized access to systems, networks, or computers. Depending on the context, this term can have either a positive or negative connotation. For example, individuals who use their skills for ethical purposes, such as identifying and reporting security vulnerabilities, may be referred to as a "white hat" or "ethical hacker".
A cracker, on the other hand, is a person who uses their technical skills for malicious purposes, such as stealing sensitive information or disrupting computer systems. This type of individual is often called a "black hat" or "cybercriminal".
The term "hacker" is a more neutral term that can describe individuals with positive and negative motives. In contrast, the term "cracker" has a primarily negative connotation and represents individuals who engage in malicious activities.
Types of Hacker
There are several types of hackers, including:
Black Hat Hackers: are individuals who use their skills for malicious purposes, such as stealing sensitive information or disrupting computer systems. They are often called "crackers" or "cyber criminals".
White Hat Hackers: These are individuals who use their skills for ethical purposes, such as identifying and reporting security vulnerabilities to improve the security of computer systems. They are often called "ethical hackers" or "security researchers".
Grey Hat Hackers: These individuals may have both malicious and ethical motives and may engage in hacking activities that are not necessarily illegal but still unethical.
Script Kiddies: These individuals use pre-written scripts or tools to hack without a deep understanding of the underlying technology.
Nation-State Hackers: Individuals sponsored by a government to carry out hacking activities for political or military purposes.
It is important to note that hacking can be illegal and result in severe consequences, such as fines and imprisonment. Ethical hacking should only be performed with prior authorization from the owner of the tested system.
2) Phishing
Phishing is a computer crime in which criminals use fraudulent emails or websites to obtain personal information from unsuspecting victims. These emails or websites may be from legitimate sources, such as banks, government agencies, or online retailers. They may ask for sensitive information such as login credentials, credit card numbers, or Social Security numbers.
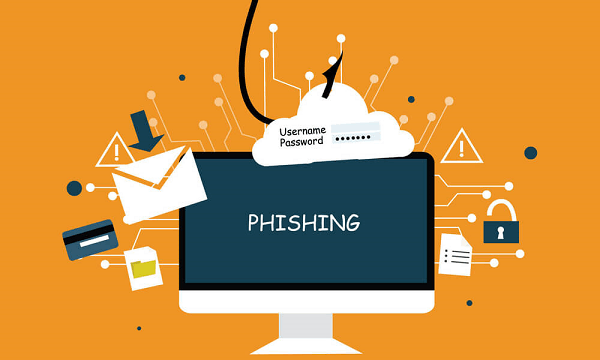
Phishing attacks typically use social engineering techniques to trick victims into providing personal information, such as urgent-sounding language, scare tactics, or a sense of urgency. These emails may have links or attachments that, when clicked, will install Malware on the victim's computer or redirect to a fake website that looks real.
Phishing can also occur via phone calls, text messages, and instant messaging.
It is important to be cautious when receiving unsolicited emails, phone calls, or messages, and do not provide personal information unless you are certain of the sender's authenticity. Additionally, it's recommended not to click on any links or download any attachments from suspicious emails or messages and to use anti-phishing tools like browser extensions, email filters, and two-factor authentication.
Types of Phishing
Phishing is an online scam designed to trick individuals into revealing sensitive information or making unauthorized financial transactions. There are several different types of phishing attacks, including:
Email phishing involves sending emails that appear to come from a trusted source, such as a financial institution or a well-known company. The emails contain a link leading to a fake website that steals sensitive information.
1) SMS phishing (SMiShing): This involves sending text messages that contain a link to a fake website. The goal is to trick the recipient into entering sensitive information on the fake website.
2) Vishing involves making phone calls that appear to come from a trusted source, such as a bank or government agency. The goal is to trick the recipient into revealing sensitive information over the phone.
3) Spear phishing: This type of phishing targets specific individuals or organizations. The attacker will gather information about the target, such as their name, job title, and company, to create a more convincing scam.
4) Clone phishing involves creating a duplicate of a legitimate email sent to the target but with a different attachment or link. The goal is to trick the recipient into clicking on the malicious attachment or link.
These are some of the most common types of phishing attacks. It's important to be aware of these scams and to take steps to protect yourself, such as being cautious of emails and links from unknown sources and not clicking on suspicious attachments or links.
Steps of Phishing
The general steps of a phishing attack are:
- Research: The attacker will research their target to gather information such as the target's name, job title, and other personal information.
- Crafting: The attacker will use the information gathered to craft a compelling message, often in an email or instant.
- Spreading: The attacker will send the message to the target, often using email or instant messaging services.
- Tricking: The attacker will trick the target into clicking on a link or attachment in the message, taking them to a fake website or downloading Malware.
- Stealing: If the target falls for the trick and enters their sensitive information on the fake website or opens the Malware, the attacker will steal this information and use it for malicious purposes.
Note: Phishing attempts can take many forms, such as phone calls or text messages, and can be done using social engineering techniques.
3) Malware
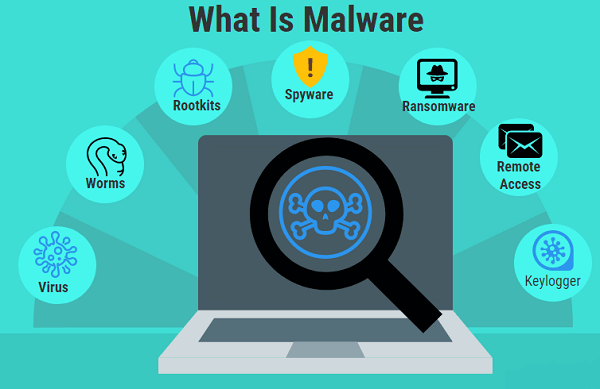
Malware, short for malicious software, refers to any software specifically designed to harm or exploit vulnerabilities in a computer system or network. This can include viruses, worms, trojan horses, ransomware, and other types of software. Malware can be spread through various means, such as email attachments, infected websites, or security vulnerabilities in software. The goal of Malware is typically to gain unauthorized access to a system, steal sensitive information, or disrupt the normal functioning of a computer.
Types of Malwares
There are many different types of Malwares, each with its specific characteristics and methods of operation. Some common types of Malwares include:
1) Viruses: A type of Malware that attaches itself to a legitimate program or file and replicates itself when the program is executed.
2) Worms: A type of Malware that can spread itself across networks without needing a host program.
3) Trojan horses: A type of Malware that disguises itself as a legitimate program or file to trick a user into installing it.
4) Ransomware: A type of Malware that encrypts a victim's files and demands a ransom payment in exchange for the decryption key.
5) Adware: A type of Malware that displays unwanted ads on a user's computer.
6) Spyware: A type of Malware designed to collect personal information without the user's knowledge or consent.
7) Rootkits: A type of Malware designed to hide the presence of other Malware on a system.
8) Banking malware: Malware designed to steal financial information, such as credit card numbers and online banking credentials.
It's important to note that some of these types of Malwares could overlap in functionality; a single piece of Malware could have multiple capabilities or functions.
Symptoms and Indicators of Malware Infection
Here are some indicators that show that Malware has infected a System:-
1) When a System is slow or unresponsive, it may be malware-infected
2) Unusual pop-ups or ads to indicate malware infection
3) Changes to the homepage or search engine
4) Unique toolbars or software installed
5) Degraded system performance or frequent crashes
6) Programs and files that are not working or missing
7) Antivirus alerts or other security software warnings
8) Unexpected system shutdowns or restarts
9) Unexplained data usage or network activity
10) Unusual network behavior or messages.
Impact of Malware on Individuals and Society
Malware can have a significant impact on an individual, including:
A) Financial loss: Malware can steal sensitive information such as bank account numbers and passwords, leading to unauthorized transactions and financial losses.
B) Personal information theft: Malware can also steal personal information such as addresses, Social Security numbers, and credit card numbers, leading to identity theft and fraud.
C) System damage: Malware can damage or destroy the files and programs on an individual's computer, leading to the loss of important data and the need for costly repairs or replacements.
D) Reduced privacy: Malware can monitor an individual's activities and steal personal information, reducing privacy and potentially exposing sensitive information.
E) Reduced system performance: Malware can slow down an individual's computer, making it difficult to perform routine tasks and leading to frustration.
Individuals need to protect their devices and information by using antivirus software, updating software regularly, being cautious when opening attachments or clicking on links, and using strong passwords.
Difference between Malware and Spyware
Malware and spyware are two types of malicious software often used for different purposes and have other characteristics.
Malware is a general term used to describe any software that is intended to cause harm to a computer or network. Malware can include viruses, Trojans, worms, ransomware, and other types of malicious software. The primary aim of Malware is to cause damage, steal data, or disrupt a computer's or network's normal functioning.
Spyware, on the other hand, is a type of Malware designed to gather information about a user's online activities without their knowledge or consent. Spyware can monitor users' keystrokes, track their internet activity, and collect personal information, such as login credentials, credit card numbers, and other sensitive data. Spyware is often used for cyber espionage and identity theft.
The main difference between Malware and spyware is the intention behind their creation. Malware is intended to cause harm to a computer or network, while spyware is intended to gather information about a user's online activities. Both types of software can have serious consequences for victims and should be taken seriously.
4) Identity Theft

Identity theft is a cybercrime where a person fraudulently obtains and uses another individual's personal information, such as their name, Social Security number, credit card number, or other identifying information, without their permission, to commit fraud or other crimes. This can lead to financial losses, damage to credit scores, and other negative consequences for the victim.
Types of Identity Theft
There are several types of identity theft, including:
1) Financial identity theft: This type of theft involves the unauthorized use of a person's financial information, such as credit card numbers, bank account information, or Social Security number, to make purchases or withdraw money.
2) Medical identity theft occurs when someone uses another person's identity to receive medical treatment, obtain prescription drugs, or file false insurance claims.
3) Criminal identity theft is when someone pretends to be another person when arrested or during any legal proceedings.
4) Social Security identity theft is when someone uses another person's Social Security number to obtain employment, housing, or other benefits.
5) Synthetic identity theft: This is a complex robbery in which a criminal combines real and fake information to create a new identity.
6) Child identity theft is when someone steals the identity of a minor, often to open lines of credit or obtain government benefits.
7) Senior identity theft is when someone targets elderly individuals and steals their personal information for financial gain.
Potential Victim of Identity Theft
Anyone can be a potential victim of identity theft, but some people may be at a higher risk. This includes:
- People who frequently use public Wi-Fi or have poor online security practices
- Individuals who have suffered a data breach or have had their personal information compromised.
- Seniors, who may be less familiar with technology and more vulnerable to scams
- Children, whose identities are often used for many years before they even become aware of it
- People who are victims of domestic violence or abuse, who may have their identities stolen by their abuser
- People who regularly receive unsolicited mail, phone calls, or emails asking for personal information
- Individuals who have a lot of personal information readily available on social media.
It is important to be proactive and protect your personal information, such as regularly monitoring your financial accounts, being cautious of phishing scams, and being careful about who you share your personal information with.
5) Cyberbullying
Cyberbullying refers to using technology, such as the Internet and social media, to harass, humiliate, or threaten someone. This type of bullying can take many forms, including spreading false rumours, posting embarrassing photos or videos, and sending threatening messages. Cyberbullying can have serious and long-lasting effects on the victim, including low self-esteem, anxiety, depression, and even thoughts of suicide. It is also difficult to escape, as the victim is constantly connected to the Internet and can be reached anytime, anywhere.
It is important for individuals, especially parents, and teachers, to be aware of the dangers of cyberbullying and to educate young people on how to stay safe online. This may include teaching young people how to respond to cyberbullying, report it to a trusted adult, and block or ignore the bully.
It is also important for websites and social media platforms to have clear policies and procedures for dealing with cyberbullying, including removing harmful content and taking action against those who engage in cyberbullying.
It is important to take cyberbullying seriously and to take steps to stop it. We can create a safer and more respectful online community by working together.
Cyberbullying Activities in the Past
Cyberbullying has become a major problem in recent years as more people use technology and the Internet in their daily lives. Here are some examples of high-profile cyberbullying incidents that have taken place in the past:
Amanda Todd: Amanda Todd was a Canadian teenager who committed suicide after being bullied online and in person. She was the victim of cyberstalking, cyberbullying, and exploitation, and her story brought attention to the devastating impact of cyberbullying on young people.
Tyler Clementi: Tyler Clementi was a college student bullied and harassed online by his roommate. He was the victim of cyberbullying and privacy invasion, and his story brought attention to the issue of cyberbullying in higher education.
Megan Meier: Megan Meier was a teenager who was bullied and tormented online by a friend. She was the victim of cyberbullying and cyberstalking, and her story brought attention to the dangers of online friendships and the impact of cyberbullying on young people.
These are just a few examples of cyberbullying incidents that have taken place in the past. It is important to remember that cyberbullying can have serious and long-lasting effects on the victim, and it is crucial to take steps to prevent it and support those affected.
Types Of Cyberbullying
Cyberbullying can take many different forms. Here are some of the most common types of cyberbullying:
1) Harassment: Sending threatening or abusive messages to someone through email, instant messaging, or social media.
2) Rumor spreading: Posting false or malicious information about someone online, such as on social media or online forums.
3) Impersonation: Pretending to be someone else online and posting malicious or embarrassing content in their name.
4) Outing: Sharing someone's private information or photos without their consent, such as posting a private conversation or a compromising photo.
5) Exclusion: Purposely leaving someone out of an online group or event.
6) Cyberstalking: Repeatedly sending unwanted messages or threats to someone, causing fear or distress.
7) Online shaming: Posting photos or videos of someone in a negative light, such as videos of them being bullied or shamed in public.
These are just a few examples of the different types of cyberbullying. It is important to remember that any form of bullying, whether it occurs in person or online, is hurtful and unacceptable. If you or someone you know is being cyberbullied, it is important to seek help from a trusted adult.
Social Impacts of Cyberbullying
Cyberbullying can have a significant and lasting impact on individuals and society. Here are some of the social effects of cyberbullying:
1) Increased anxiety and depression: Cyberbullying can lead to feelings of anxiety, depression, and hopelessness in victims and can increase the risk of self-harm or suicide.
2) Decreased self-esteem: Cyberbullying can make victims feel embarrassed, ashamed, and worthless, leading to reduced self-esteem and self-worth.
3) Social isolation: Cyberbullying can make victims feel isolated and alone, as they may be reluctant to participate in social activities or form relationships for fear of further bullying.
4) Decreased academic performance: Cyberbullying can negatively impact academic performance, as victims may have difficulty concentrating and miss school due to stress or anxiety.
5) Decreased overall well-being: Cyberbullying can negatively impact physical and mental health and lead to long-term health problems such as heart disease, stroke, and sleep disorders.
These social effects of cyberbullying demonstrate why it is important to prevent cyberbullying and support those affected. Educating individuals, especially young people, is also important to educate them on how to use technology and the Internet responsibly and safely.
Protection Against Cyberbullying
Here are some steps individuals can take to protect themselves against cyberbullying:
Be cautious about what you share online: Be mindful of what you post on social media, and avoid sharing personal information, photos, or other sensitive material that could be used against you.
Use privacy settings: Adjust your privacy settings on social media and other online platforms to limit who can see your information and posts.
Block and report bullies: If someone is bullying you online, block them and report their behavior to the platform or website.
Don't engage with the bully: Avoid responding to or engaging with the bully, as this may escalate the situation.
Seek support: Talk to a trusted adult or counselor about what is happening, and seek their help in dealing with the situation.
Educate others: Teach others about the dangers of cyberbullying, and encourage them to use technology responsibly.
Be an ally: If someone is bullied online, speak up and positively support them.
These steps can help individuals protect themselves against cyberbullying, but it is also important for society to take action to prevent and address this issue. This may include increased education and awareness, stricter laws and enforcement, and better support and resources for victims.
6) Pornography
Pornography is a controversial and polarizing topic, with some viewing it as a form of free speech and expression. In contrast, others consider it morally wrong and degrading to individuals, especially women. The growth of the Internet has significantly impacted the accessibility and availability of pornography, and it remains a major issue in many countries, with debates ongoing about censorship, regulation, and control. Pornography can be considered a form of cybercrime if it involves creating, distributing, or possessing illegal or underage sexually explicit material. This can include child pornography, which is illegal in most countries and considered a serious offense. Distributing or possessing child pornography can result in severe legal penalties, including imprisonment. Additionally, creating and distributing non-consensual or revenge pornography, which involves the dissemination of sexually explicit images or videos of someone without their consent, is also illegal in many countries and is considered a form of cybercrime. The production, distribution, and possession of such material can have serious consequences for the victims and those who engage in these activities.
Child Pornography
Child pornography refers to any sexually explicit material involving minors, meaning individuals under 18. This material can include photographs, videos, and other forms of media that depict sexual acts, nudity, or sexual exploitation of children. The creation, distribution, and possession of child pornography is illegal in most countries and is considered a serious offense. The following are some of the types of child pornography:
1) Photographic child pornography - photographs that depict sexual acts, nudity, or sexual exploitation of minors.
2) Video child pornography - videos that depict sexual acts, nudity, or sexual exploitation of minors.
3) Computer-generated child pornography - digitally created images that depict minors engaged in sexually explicit acts.
4) Child erotica - sexually suggestive material that involves minors but does not depict sexual acts.
It is important to note that child pornography is a form of child abuse and can cause serious harm to the minors involved. The production, distribution, and possession of child pornography are illegal and punishable by law, and those who engage in these activities can face severe legal consequences, including imprisonment.
Laws in India Against Child Pornography
In India, the production, distribution, and possession of pornography, including child pornography, is illegal. The laws related to pornography are primarily governed by the Indian Penal Code (IPC) and the Information Technology Act 2000.
Under the Indian Penal Code, obscenity, including the production, distribution, and sale of obscene materials, is a criminal offense punishable by imprisonment and fines. The Information Technology Act 2000 includes provisions for punishing those who produce, distribute, or possess obscene materials, including child pornography, over the Internet.
In India, the distribution of pornographic materials, including through the Internet, is prohibited, and individuals can be held liable for accessing, distributing, or possessing such materials. However, it should be noted that the enforcement of these laws can vary, and the production and distribution of pornography remain a significant problem in India.
It is important to note that viewing, distributing, or possessing pornographic materials, including child pornography, is illegal and can have serious consequences, including imprisonment. Individuals and organizations should report suspected child pornography to the relevant authorities.
Laws and Rules Regarding Cybercrime
Laws and regulations regarding cybercrime vary by country, but most have established rules to address various forms of cybercrime, such as hacking, identity theft, and cyberstalking. Some common rules and regulations related to cybercrime include the following:
1) Computer Fraud and Abuse Act (CFAA): A federal law in the United States that makes it illegal to access computers or computer systems without authorization.
2) Electronic Communications Privacy Act (ECPA): A federal law in the United States that regulates the interception and disclosure of electronic communications.
3) Data Protection Acts: Laws in many countries regulate personal data collection, storage, and use.
4) Identity Theft and Assumption Deterrence Act: A federal law in the United States that makes it illegal to knowingly transfer or use another person's identity with the intent to commit fraud or other crimes.
5) The General Data Protection Regulation (GDPR): A European Union regulation that protects personal data and privacy.
6) Convention on Cybercrime: An international treaty that provides a framework for cooperation among nations to combat cybercrime.
Individuals and organizations must know and comply with relevant laws and regulations in their jurisdiction. Failure to do so can result in legal consequences, such as fines and imprisonment. Additionally, organizations may be subject to additional rules, such as industry-specific regulations, that require the protection of sensitive information.
How to Prevent Cybercrime
Preventing cybercrime requires a multi-layered approach that involves a combination of technical measures, education, and awareness. Some steps that individuals and organizations can take to reduce their risk of being a victim of cybercrime include:
Use strong passwords: Use a combination of letters, numbers, and symbols in passwords, and avoid using easily guessable information such as birthdays or names.
Keep software up to date: Regularly update software and operating systems to address known security vulnerabilities.
Use antivirus software: Install and regularly update antivirus software to protect against Malware.
Enable firewalls: Use firewalls to prevent unauthorized access to computer systems.
Be cautious of emails and attachments: Be careful of emails and attachments from unknown or suspicious sources, as these can be used to spread Malware or steal personal information.
Educate employees: Provide training and education to employees on the importance of cybersecurity and safe online practices.
Back up data: Regularly back up important data to reduce the risk of data loss in a cyberattack.
Use encryption to protect sensitive information transmitted over the Internet or stored on computer systems.
Monitor for suspicious activity: Regularly monitor computer systems and networks, such as unauthorized access or data changes.
By taking these and other precautions, individuals and organizations can reduce their risk of being a victim of cybercrime and better protect their sensitive information.
National Cybercrime Reporting Portal
In India, the National Cyber Crime Reporting Portal is an online platform for reporting cybercrime incidents. The Ministry of Home Affairs launched the portal maintained by the National Crime Records Bureau (NCRB). The portal aims to provide a convenient and secure mechanism for citizens to report cybercrime incidents, including cyber fraud, hacking, identity theft, and cyberstalking.
The National Cyber Crime Reporting Portal provides a user-friendly interface for reporting cybercrime incidents. It enables citizens to provide relevant information, including details of the incident, evidence, and supporting documents. The portal also provides a mechanism for tracking complaints and investigations' status.
It is important to note that the National Cyber Crime Reporting Portal is not intended to replace existing reporting mechanisms, such as the local police, but to complement these existing channels and provide an additional avenue for reporting cybercrime.
Individuals and organizations are encouraged to report incidents of cybercrime to the National Cyber Crime Reporting Portal and to take appropriate measures to protect themselves from cybercrime, including using strong passwords, keeping software and antivirus systems up to date, and being cautious about providing personal and sensitive information online.
Where to Report Cybercrime
If you have been a victim of cybercrime, you can report it to the following authorities:
Local Police: Contact your local police department and file a complaint. Provide as much detail as possible about the incident, including when it occurred, how it happened, and any evidence you may have.
National Cyber Crime Reporting Portal: In India, you can report cybercrime incidents to the National Cyber Crime Reporting Portal, an online platform maintained by the National Crime Records Bureau (NCRB).
Cyber Crime Investigation Cell (CCIC): The Cyber Crime Investigation Cell is a specialized unit within the Indian police that deals with cybercrime-related cases. You can contact the CCIC to report incidents of cybercrime.
Computer Emergency Response Team (CERT-In): In India, CERT-In is the national nodal agency responsible for responding to computer security incidents and providing technical assistance to victims. You can report incidents of cybercrime to CERT-In.
Note: Reporting cybercrime as soon as possible increases the chances of the perpetrators being caught and the stolen information being recovered. Additionally, reporting cybercrime can help to raise awareness about the issue and prevent others from becoming victims.