What is a Kensington Lock?

A Kensington Lock is a security device similar to the lock, which is used to secure bicycles. Kensington Lock consists of a metal cable insulated with rubber. One end of this cable is mounted with metal and provides multiple locking options to its consumers.
Kensington, a division of ACCO Brands, is headquartered in Burlingame, California. Kensington is the inventor and the market leader in providing anti-theft solutions to more than a hundred electronic devices. It has shown its expertise in this field for almost 25 years and has sold over 20 million security locks. Kensington has successfully gained the trust of well-known global MNCs such as HP and Lenovo.
What is Kensington Security Slot, and where is it found?

Kensington Security Slot is a small metal augmented hole or slot found in modern-day electronic devices such as laptops, projectors, printers, external hard drives, desktops, gaming consoles, etc. The location of the hole may vary according to the different products and their models, but generally, in laptops, it is found either on any one side or at the back.
This Kensington slot in the electronic devices is the place where the Kensington Locks are attached to secure the systems.
Types of Security Slots
1) Kensington Security Slot – This is a traditional and first-generation slot that Kensington has been developing for more than twenty-five years. These slots are generally a little bigger than the next-generation slots developed by Kensington. Global companies like Dell and HP that partnered with Kensington during its initial era used to have these slots on their devices.
2) Kensington Nano Security Slot – With the success of its traditional slots, Kensington continuously designed and invented slots that are much thinner and lighter that would not just be used in personal computers but be compatible with almost every electronic device such as mobile phones, hard drives, etc. These slots are 70% small compared to their previous slots.
3) Kensington ClickSafe Security Anchor – This uses modern technologies and makes its usage much easier and simple by just enabling one-tap secure features to its users.
Two most used locking options provided by Kensington are given below:
1) Lock with Keys: This consists of a metal lock mounted on one side of the cable, and it provides keys with which consumers can lock or unlock it.

2) Combinations Locks: This allows consumers to set a combination code with which both the locking and the unlocking can be done. There are no keys for this kind of lock.
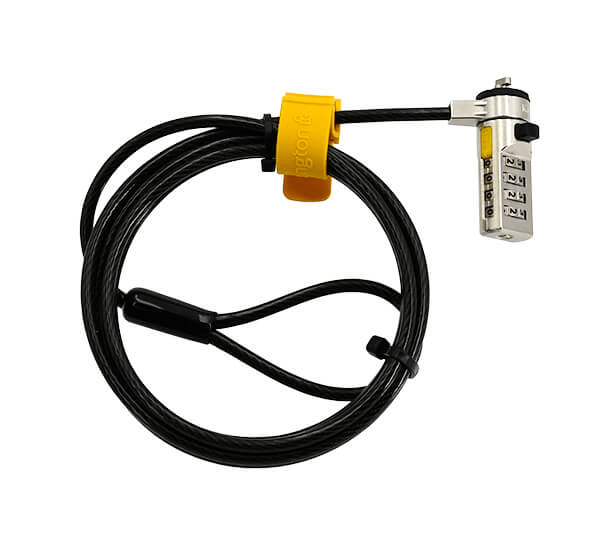
The other end of the metal cable in the Kensington Lock comes with a loop which allows the consumers to loop or tie around this cable to some heavy and stationary object. This ensures that the electronic device gets attached to the heavy object until and unless it is unlocked.
Features of Kensington Locks
- Rigid and Strong Head Lock: The Kensington Lock uses the best quality material to construct its lock. The head of the lock attaches firmly to the Kensington Security Slot and makes it very difficult to pull off until and unless the user unlocks it himself. This lock is also resistant to tamper and meets the modern generation industry needs.
- Ample options of combination codes: Kensington Locks are very secure as it provides more than ten thousand easy-to-remember combination codes that the consumer can set to secure its system.
- Innovative Designs: Kensington Lock comes with modern-day designs and makes it very handy to use. Kensington Lock is built with a push-button design which makes attaching the lock to the security slot easier and quicker.
- Cut Resistant Cable: Kensington Lock has solid and thick carbon steel cables that are properly insulated, thus making it tough to cut down.
- Register and Retrieve: If ever the consumer forgets the Kensington combination code Kensington makes it very easier and quicker to retrieve the code via registering it to their online combination code program.
- Compatible: Kensington Locks were not only invented to secure personal computers but it is designed and developed so that it fits into more than a hundred modern-day electronic devices. Some of them are laptops, desktops, televisions, printers, etc.
Which Kensington Lock is best suited for me?
Kensington Locks are made keeping in mind every type of consumer. Different people have different needs, for example, a student might not require a high-level locking system compared to an employee working in a public place.
Let’s see what Kensington has for different types of consumers.
Consumers who work in public places
People working in a public place, say a restaurant or in a cafe, requires a strong securing system. Kensington has a product named MicroSaver 2.0 Portable Keyed Laptop Lock, which has a long and tough cable that perfectly matches the consumer requirements. The head of this lock gets strongly attached to the slot, thus enabling high security.
IT field workers
Kensington ClickSafe 2.0 Keyed Laptop Lock is best suited for this kind of consumer as it provides one tap locking feature which is hassle-free and easier to use. As this provides very high-level security, it is one of the most commonly used and demanding products among the consumers.
Devices having no security slots.
Kensington offers N-17 Combination and Keyed locks for devices having no slots. Devices require no modifications as it comes with the new non-invasive locking technology. By providing strong security, it is also very handy to use.