What is Data diddling?
Data diddling, or data manipulation, is a type of computer-based fraud in which data is altered or changed to cause harm, gain an advantage, or conceal fraudulent activities. This can be done by changing data values, modifying data fields, deleting data, or adding data to a database or computer system. Insiders, such as employees or contractors, often do data diddling with an authorized computer system or database access.
External attackers who have gained unauthorized access to the system can also carry it out. The consequences of data diddling can be serious, ranging from financial losses and damage to reputation to legal liabilities and regulatory violations. To prevent data diddling, organizations should implement strong security measures, such as access controls, authentication, and data encryption, as well as monitoring and auditing tools to detect and prevent unauthorized changes to data.
Protection from Data diddling:
To protect against data diddling, organizations should implement the following measures:
1. Access control: Limiting access to sensitive data to only authorized personnel is crucial in protecting against data diddling. Access should only be granted to those who need it to perform their duties.
2. Authentication: Passwords, two-factor authentication, biometric verification, or other authentication methods can help verify the identity of users accessing the data.
3. Data encryption: To prevent illegal access and modification, data should be encrypted both in transit and at rest.
4. Regular backups: Regularly backing up data can help the organization recover lost or damaged data in case of a successful data diddling attack.
5. Monitoring and auditing: Implementing monitoring and auditing tools can help detect and prevent unauthorized changes to data. These tools can alert security personnel when unauthorized access or changes to data occur.
6. Employee training: Educating employees about data security best practices, including the risks of data diddling, can help reduce the likelihood of insider attacks.
7. Continuous security assessment: Regular security assessments can help identify and address vulnerabilities that attackers could exploit. These assessments should include technical and non-technical measures, such as policies and procedures, employee behaviour, and physical security. By implementing these measures, organizations can significantly reduce the risk of data diddling and improve their overall data security posture.
Process of Data diddling:
Data diddling typically involves the following steps:
1. Identifying the target data: The attacker identifies the target data they want to manipulate, such as financial records, personal information, or transaction data.
2. Gaining access: The attacker gains access to the target system or database by exploiting vulnerabilities or obtaining login credentials.
3. Modifying the data: Once the attacker has access, they modify the target data, either by changing values, deleting records, or adding new entries.
4. Covering their tracks: By erasing audit logs or changing records to make it appear that someone else performs the changes, the attacker may try to hide their traces to avoid being discovered.
5. Exploiting manipulated data: Once the data has been used, the attacker can exploit it for financial gain, political advantage, or other purposes.
6. Continuing the attack: In some cases, data diddling may be an ongoing attack where the attacker continues manipulating the data over an extended period, gradually escalating the attack's impact.
Data diddling seriously threaten data security and can cause significant harm to organizations and individuals. Preventing data diddling requires a comprehensive approach to data security, including measures to detect and prevent unauthorized access and tools to monitor and audit data changes.
Methods of Data diddling:
There are various methods of data diddling that attackers may use to manipulate data, including:
SQL injection: This involves exploiting vulnerabilities in web applications to inject malicious SQL commands into a database, allowing the attacker to modify data in the database.
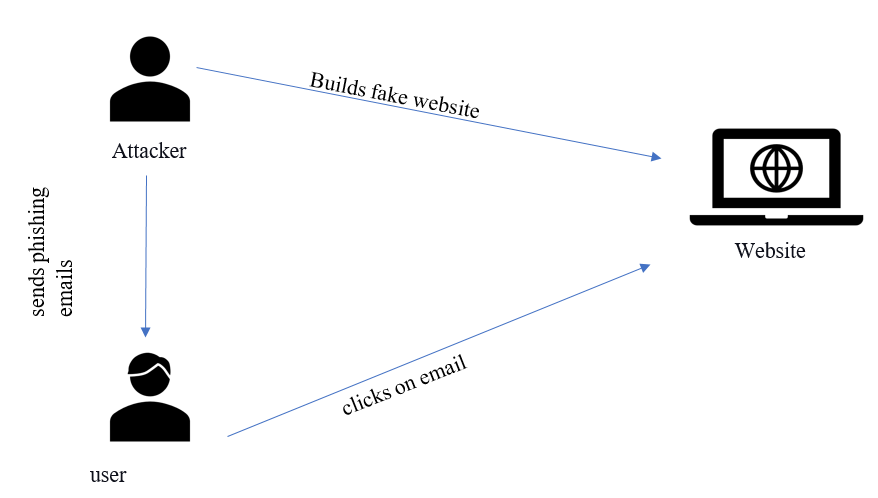
Social engineering: Attackers may use social engineering techniques to trick users into providing login credentials or other sensitive information that can be used to gain access to a system or database.
Backdoor access: Attackers may install a backdoor on a system, bypassing security controls and manipulating data undetected.
Malware: Attackers may use malware, such as keyloggers or spyware, to steal login credentials or gain access to a system, allowing them to manipulate data.
Insider threat: Insiders, such as employees or contractors with authorized access to a system or database, may manipulate data for personal gain, revenge, or other motives.
Data interception: Attackers may intercept data in transit, such as over an unsecured Wi-Fi network, and modify it before it reaches its destination.
Exploiting system vulnerabilities: Attackers may exploit software, hardware, or network infrastructure vulnerabilities to gain unauthorized access to a system or database and manipulate data.
To protect against these methods of data diddling, organizations should implement strong security measures, such as access controls, authentication, data encryption, monitoring, auditing, regular security assessments, and employee training.
Effects of Data diddling:
Data diddling refers to maliciously altering data or information in a computer system without the knowledge or consent of the owner or user of the system. The effects of data diddling can be serious and far-reaching, including:
- Financial loss: Data diddling can lead to financial loss, either directly or indirectly. For example, a hacker may alter the payment information in a company's database to redirect payments to their account, causing the company to lose money.
- Reputation damage: Data diddling can damage an individual's or organization's reputation if the altered data is made public or used to discredit them.
- Legal consequences: Data diddling can result in legal matters, especially if the altered data is used to commit a crime, such as fraud or theft.
- Data loss: Data diddling can lead to the loss of important data or information, especially if the altered data is critical to the operation of a system.
- Operational disruption: Data diddling can disrupt the normal operation of a system, leading to downtime or reduced productivity.
- Privacy violations: Data diddling can compromise the privacy of individuals or organizations, especially if sensitive data is altered or used for malicious purposes.
Overall, the effects of data diddling can be severe and long-lasting. Individuals and organizations must take steps to prevent it, such as implementing strong cybersecurity measures and regularly monitoring their systems for suspicious activity.
Laws for Data diddling:
The laws for data diddling can vary by country, but it is generally illegal and can result in criminal charges such as computer fraud, identity theft, or even hacking.
- For example, data diddling may violate the Computer Fraud and Abuse Act (CFAA) in the United States. This federal legislation makes it unlawful to gain unauthorized access to a computer purposefully or to use that access for an extended period. Violators may face fines and imprisonment depending on the offense's severity.
- In the European Union, data protection laws such as the General Data Protection Regulation (GDPR) may also apply in cases of data diddling. The GDPR gives individuals the right to control their data and imposes heavy fines on organizations violating these rights.
It is important to note that the laws surrounding data diddling constantly evolve as technology advances and new threats emerge. Therefore, individuals and organizations must stay up-to-date with the latest regulations and best practices to ensure they are not inadvertently breaking the law. Additionally, seeking legal advice in cases of suspected data diddling or other cybercrimes is always recommended.
Cases related to Data diddling:
There have been numerous cases related to data diddling over the years.
- One example is the case of Kevin Mitnick, a notorious hacker who was arrested in 1995 for multiple offenses, including data diddling. Mitnick was known for using social engineering techniques to gain access to computer systems. He had hacked into the systems of numerous companies and government agencies, including Motorola, Sun Microsystems, and the FBI. He was eventually caught and sentenced to five years in prison, followed by three years of supervised release.
- Another high-profile case involving data diddling was the Target data breach of 2013. Hackers gained access to Target's computer systems and stole the credit and debit card information of approximately 40 million customers. The breach was caused by a vulnerability in Target's payment processing system that the hackers exploited. The fallout from the Target breach was significant, with the company facing multiple lawsuits and a loss of customer trust. The incident also spurred greater awareness of the importance of cybersecurity and data protection.
These cases illustrate the seriousness of data diddling and the potential consequences for those who engage in such activities. They also highlight the importance of strong cybersecurity measures and the need for companies and organizations to protect their data and systems from hackers and other cyber threats.