What is Protocol?
A protocol is a set of rules for formatting and processing data in networking. These rules govern the users on the network stating the instructions to format and process the data shared on the network. These rules are essential to be implemented. Various devices are connected to the network, and they can be smartphones, laptops, or personal computers. Moreover, the user can also use various software to access the network to ensure that the communication between different devices and software goes smoothly.
Most of the protocols used during networking are similar to the language. In real life scenario, the person from different countries may have difficulty communicating in the native language of the other. Still, they can choose an entirely different language to communicate with instead of doing so.
The protocol can also be explained as an official language like many international organizations have certain languages that can be used to perform communication. Similarly, when we talk about networking, if one system in the network uses Internet Protocol to communicate on the internet, then to establish a connection with the other system, it is necessary for the system to also use Internet Protocol.
If any of the protocol does not use the Internet Protocol, it will not be possible to establish a connection between both computers. Several activities can be performed on the internet, requiring different rules. The network is divided into different layers; each layer has its protocol to perform its tasks. The OSI model defines the various layers of the network, and it is sometimes taken as a reference to discuss the protocols in networking.
OSI Model in Networking
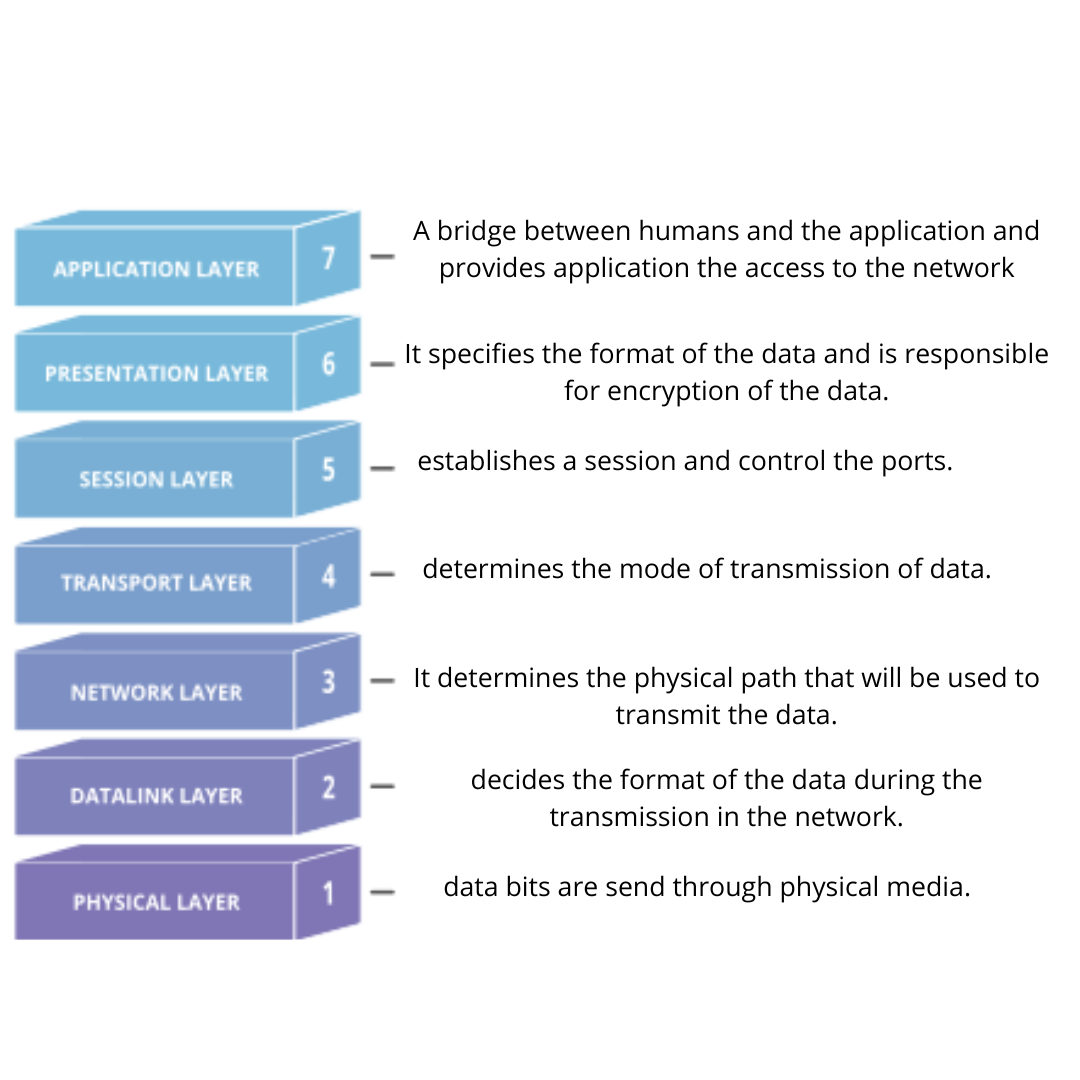
OSI Model stands for Open System Interconnection Model, is the standard model that describes the structure and working of the network. In the OSI model, the network is divided into 7 layers, every layer has its task to perform, and they have different protocols to perform the functions effectively.
For example, the Internet Protocol is responsible for directing the data packets; it states the source form where the data packet originates and where the data packet is headed to.
It is essential to set up a network-to-network connection. Thus, the protocol works at the network layer. Therefore, it is considered a layer 3 protocol. Considering another protocol, the Transmission Control Protocol, as the name suggests, is responsible for managing data transmission. It ensures no issues during the transfer of data between the source and the destination. The TCP works at the transport layer of the network; therefore, it is considered the layer 4 protocol.
What is a data packet?
When sharing the data on the network, the data is not sent as a single unit but is divided into small segments; each packet is called a data packet.
Network Layer Protocol
We have already discussed Internet Protocol; in the network layer, the task performed by the IP is routing the data packets. Numerous other protocols are implemented at the network layer of the internet.
IPsec: It stands for Internet Protocol Security; one of the major networking issues is security. This protocol is responsible for handling the part.
The protocol performs the following function to ensure the security of the network:
- Setting up encryption
- Authenticates the Internet Protocol connection over a VPN.
- It is not a protocol, but it constitutes various other protocols such as Authentication Header and Encapsulating Security Protocol.
ICMP: It stands for Internet Control Message Protocol. The protocol is responsible for notifying about any updates in the status of the network or any error in the network. This protocol is very important to ensure that the complete data is received at the destination. When data is transmitted, there is always the possibility of losing some data during transmission; this protocol sends a notification to the data source whenever the router fails to send one or multiple data packets.
IGMP: It stands for Internet Group Management Protocol. The protocol is similar to making a group in any social media application. The protocol is used to establish one too many connections that allow a single user to send the data to multiple devices simultaneously. This reduces the effort of the sender. It allows multiple devices to receive messages sent to a single IP address.
Some other protocols that are implemented on the internet
TCP: It stands for Transmission Control Protocol. The protocol is implemented at the transport layer of the network. The protocol's responsibility includes ensuring that all the data packets reach the destination from the source. It is required to establish a connection before implementation, and this connection serves as the path for the data packets. This protocol is often implemented with Internet Protocol (IP). Thus, it is also known as TCP/IP.
HTTP/HTTPS: Whenever the user accesses the internet, the user can find this protocol implemented at the very start of the website address. It is the basic foundation block of the world wide web. HTTP stands for Hypertext Transfer Protocol and is implemented at the application layer of the network. Today many users use internet services; the data is shared between different devices.
The data is required in a suitable format so that the application can use the data. The webpages on the internet are created using various languages such as HTML, CSS, JavaScript, and many others. The data should be interpreted before displaying it to the user. The layer at the lowest level is managed by the system's OS instead of the applications. The only thing that HTTP lacks is that it is not secure, as anyone who gains access to the HTTP message can easily read it. This issue was resolved by HTTPS. This protocol ensures security by encrypting the message.
TLS/SSL: This protocol is implemented by the Hypertext Transmission Protocol Secure (HTTPS); it is used to encrypt the HTTP message. This was previously known as the Secure Sockets Layer.
UDP: This protocol is also implemented at the transport layer. The protocol provides services that can manage some data loss but require high bandwidth, such as during live streams or playing online video games. The difference between the TCP and UDP is that the complete data transmission is not ensured in UDP, but it allows faster transmission than the TCP.
Protocols Used by the Routers
When the data is transmitted between numerous devices, especially in large networks, there is always a possibility of multiple routes to transmit the data between the source and destination. Some protocols help in determining the best route for the data transmission. They are not concerned with the transfer of the data but only suggest the route for the transmission. Some of these protocols are:
BGP: It stands for the Border Gateway Protocol implemented at the application player layer. The protocol's purpose is to make the IP address visible to every system so that the data packets can easily be sent to the destination. It is a static routing protocol, which means it cannot automatically make changes in the routing table, so they have to be performed manually.
EIGRP: The protocol determines the distance between all the routes and creates a routing table with all the paths and the distance between the routers. Once the table is created, the protocol automatically chooses the best route to transfer the data. It can make changes in the table on its own, and once the changes are implemented, they are shared with all the routers in the network. The protocol is called the Enhanced Interior Gateway Routing Protocol.
OSPF: The very first step is to determine the best path for the transmission of the data. The routers evaluate the best route considering the distance and various other factors. It will take bandwidth into account also. The protocol also maintains a database that records the data about the arrangement of the network devices and implements the Dijkstra algorithm to evaluate the network path whenever some changes occur.
RIP: This protocol can be implemented for both local and wide-area networks. The protocol is executed at the application layer. This protocol was previously used to determine the distance between the routers. The RIP was released in two versions:
The first version evaluated the path using the IP address of the destination and the number of hops required for completing the journey. The first version broadcasts the IP table to all the routers in the network, whereas the latter version sends the routing table to the multicast address.
Implementation of Protocol to Prevent Cyber Attack
Computers have always been subject to risk, but the risks increased exponentially with the ability of the system to connect to the network. In networking, the attackers can disrupt the working of the protocols. This can affect the systems that are implementing the protocol.
The attacker can use the protocol to attack the systems; multiple protocols can be used to perform a DDoS attack. They stand for distributed denial of service attacks. For example, the attacker can use the TCP protocol to flood the user with SYN requests; it initiates the handshake process until it finds an actual client. This can cause a delay in the connection and affect the efficiency of the network.